RAID Acquisition
RAID Acquisition. Computer Forensics COEN 152/252. RAID Levels. RAID 0: Just a Bunch Of Disks (JBOD) RAID 1: Mirrored RAID 5: Redundancy through parity distributed parity. RAID. Hardware RAID Two types: Special controller that plugs into one of the buses


RAID Acquisition
E N D
Presentation Transcript
RAID Acquisition Computer Forensics COEN 152/252
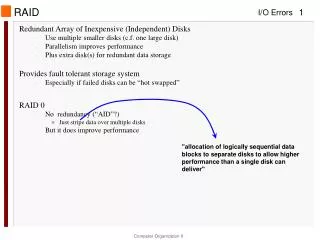
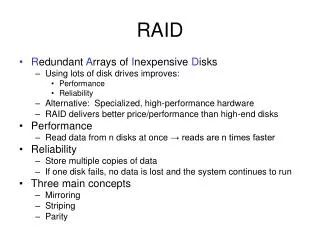
RAID Levels • RAID 0: Just a Bunch Of Disks (JBOD) • RAID 1: Mirrored • RAID 5: Redundancy through parity • distributed parity
RAID • Hardware RAID • Two types: • Special controller that plugs into one of the buses • Device that plugs into normal disk controller such as ATA, SCSI, Firewire, … • Computer sees a single volume
RAID • Hardware RAID acquisition • Step 1: Acquire and investigate complete RAID volume as a single volume • Needs big target device. • Use device drivers such as those contained on Linux distributions • Step 2: Acquire individual disks and look for hidden data in possible areas that the RAID volume did not use. • Keyword searches can also be performed on the individual disks.
RAID • Software RAID • OS sees individual disks • But sees them together as a single volume. • CPU calculates parity info.
RAID • Software RAID • Easiest: Acquire entire volume • Encase, ProDiscover can import disks from a Windows RAID volume and analyze them as a single volume. • Allows access to data that is hidden on individual disks.