ATM Security
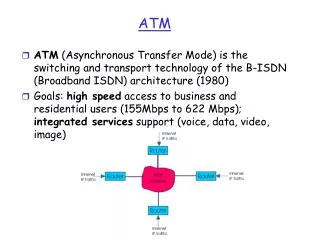
ATM Security. December 2001. Draft 12/28. Why I chose this topic. We find that many people believe that ATM is intrinsically secure. Current wisdom says: ATM’s high speed makes it impossible to extract data. ATM uses optical fibre and you can’t tap an optical circuit.

ATM Security
E N D
Presentation Transcript
ATM Security December 2001 Draft 12/28
Why I chose this topic • We find that many people believe that ATM is intrinsically secure. Current wisdom says: • ATM’s high speed makes it impossible to extract data. • ATM uses optical fibre and you can’t tap an optical circuit. • Not so - there are many things a bad guy can do and you can buy the kit to tap an optical line for about $2,000.
Agenda for the presentation • ATM - a recap • Security issues affecting ATM • Securing ATM connections
ATM Technology One International Standard Both LAN and WAN Technology Standards Based Scalable in Distance QoS Carries Multiple Traffic Types Scalable in Speed Voice/Data/Video Mb Gb A
ATM Concepts • Negotiated Service Connection • End-to-end connections, called virtual circuits • Traffic contract • Switched Based • Dedicated capacity • Cell Based • Small, fixed length A
Quality of Service is important We will accept jerky video but not jerky voice so for mixed mode traffic ATM is a key solution. QoS Data Video Audio
The ATM Cell Header Payload • Small Size • 5 Byte Header • 48 Byte Payload • Fixed Size means buffers can be fixed and switches faster • Header contains virtual circuit information • Payload can be voice, video or other data types 5Bytes 48 Bytes A
ATM Layer Physical Layer Adaptation Layer ATM System Architecture Forward Cell Through Network Add 5-Byte Header Conversion to ATM Data Types, 48-Byte Length Convert To Correct Electrical Or Optical Format Video Cell Data Cell Voice Cell Services A
ATM Adaptation Level AAL Types 1 Circuit Emulation -Constant Bit Rate (CBR) Low Bit Rate Voice (Real Time) -Variable Bit Rate (VBR) Time Invariant Data “Simple” Data • Provides Mapping Of Applications To ATM Service Of The Same Type • Segments/Reassembles Into 48 Byte Payloads • Hands 48 Byte Payloads To ATM Layer 48 Bytes 2 3/4 5 A
ATM Layer 48-Byte Payloads From AAL 5-Byte Header • Adds/Removes Header To 48 Byte Payload • Header Contains Connection Identifier • Multiplexes 53 Byte Cells Into Virtual Connections • Sequential Delivery Within A Virtual Connection } 53-Byte Cell To Physical Layer Header Contains Virtual Path and Channel Identifiers A
Physical layer Acablecancontain up to 255 virtual paths. A virtual path can contain up to 65,535 virtual channels.
Virtual channels • Virtual channels can be permanent (PVCs) or switched (SVCs). • PVCs are controlled by the carrier. • SVCs are controlled by the end user.
ATM has a future • At very high transfer rates, the 9% of bandwidth dedicated to the header is too high.Groups are working on a specification for a new version of ATM that will allow variable cell length. • The ATM Forum are looking at retaining the benefits of the 53 byte cell size whilst adopting a more flexible approach to headers. • ATM is a rival for Multi-Protocol Label Switching (MPLS) the IETF attempt to provide different switching rates for different traffic.
Security issues affecting ATM You understand IP threats so let’s apply them to ATM
ATM threats • ATM networks are vulnerable to similar attacks as IP based networks. Examples of attacks that ATM networks may suffer include: • Eavesdropping • Spoofing • Denial of Service • Traffic Analysis • Virtual Channel Theft – a unique threat suffered only by ATM.
ATM - Points of Attack Knowledge of the internals of ATM is becoming widespread as is knowledge of SNMP network management systems.
Network management • PVCs and SVCs may be configured by network management systems that may rely on Telnet. • Monitoring systems can be accessed by Web browsers, or RMON probes that make data available. • Attackers can hijack management systems and perform management functions, much as phreakers attacked phone switches.
Virtual Circuits • PVCs are controlled by the carrier and generally more secure. • SVCs are controlled by users and are becoming more popular due. • SVCs are controlled by the Interim Local Management Interface IILMI). Access to the ATM device may be as simple as hooking up a PC or accessing a router using Telnet. • Attackers can join an SVC session by using the add-to-call function of the SVC management system
Hijacking virtual circuits • Attackers obtaining access to a management console or a switch can highjack a PVC. • Once a PVC has been hijacked the options for exploiting the access depend upon how ATM is used. • If an organisation relies solely on ATM for its protection, an attacker could insert fraudulent transactions. • If the PVC is used to access the corporate network then an attacker has effectively bypassed access controls.
Virtual Circuit theft • Increasingly long distance traffic (particularly international traffic) will traverse ATM circuits owned by different carriers. • Although ATM networks are connection based, cells are switched based upon the Virtual Channel or Virtual Path Indicators in the header. • If a VCI or VPI is altered in a switch then subsequent switches will treat the cells as valid. • A user could send traffic using a higher QoS and have someone else pick up the bill.
Physical Layer • Just as with IP networks, access to physical resources must be controlled but…………. • you do not know what the physical path is. Resources may be controlled by the service provider, or more likely they will be controlled by multiple partners of the service provider. • You may not know who is carrying your data.You are unlikely to know the strength of their security and how well they restrict access to physical network resources.
Denial of Service attacks • Like many TCP/IP denial of service attacks, ATM can be attacked by repeatedly sending network commands. This requires access to the management system, but these are frequently IP based and potentially vulnerable to attack. • Examples of commands that can be exploited include diagnostic requests, or requests to be added to a virtual channel.
Scenario for an ATM attack • Tap an OC3 line, connect to an ATM analyser, sit back and monitor your confidential data. • It is not as difficult nor as expensive as you might think. You need access to the line, an optical splitter or tap, a PC with a couple of ATM network cards and some software. • Consider a posting on the following sitehttp://www.inet-one.com/cypherpunks/dir.1999.05.31-1999.06.06/msg00209.html
A Posting from Cypherpunk “We attach the two Coral/OC3mon ATM NICs to an OC-3 optical fiber pair carrying IP-over-ATM traffic. We connect the receive port of each ATM card to the monitor port of an optical splitter. The splitter carries a fraction of the light from each fiber to the receive port of one NIC. Attached to an OC-3 trunk that terminates on a switching device (e.g., an ATM switch or a router), one of the Coral/OC3mon NICs sees all traffic received by the switching device and the other NIC sees all traffic transmitted by the switching device. The Coral/OC3mon NICs capture traffic on the two directions of an OC-3 link independently.”
Optical Taps are not expensive A Century optical tap from Shomiti – costs around $150 Passive taps allow monitoring/capture/analysis of physical errors, enable full-duplex, full-line rate performance, even at gigabit rates whereas span ports do not. Passive taps also enable the dynamic insertion of network monitoring/analysis devices that need to 'see' all the traffic, i.e., RMON probes, Intrusion Detection/Security devices, and network/protocol analyzers without breaking the segment. http://www.shomiti.com/products/taps/index.html
The hardware required • IBM personal computer clone with 256 MB of main memory, a 166 MHz Intel Pentium processor, an Ethernet interface. • Two ATM interface cards, and a 33 MHz 32-bit-wide PCI bus. The ATM interface card used in the current Coral/OC3mon implementation is the Fore Systems ATM network interface card (NIC) for the PCI bus. The Intel i960 processor on this interface card allows us to optimise Coral/OC3mon operation with custom firmware.
The software required • “In response to community feedback, NLANR's (National Laboratory for Applied Network Research) Measurement and Operations Analysis Team (MOAT) and the Cooperative Association for Internet Data Analysis (CAIDA) have ported Coral/OC3mon to FreeBSD Unix (2.2.2-RELEASE). The Unix port is divided into two portions, the kernel-space device driver which deals with the Fore PCA-200E card directly and the user-space code that does the flows analysis and fulfills requests for summary reports.” http://www.caida.org/outreach/papers/Inet98/#coral
Requirements for ATM security …………….. in fact nothing new
Basic security is important • Many users of ATM believe it to be intrinsically secure - they fail to implement basic security. • Baseline security requires protection of cables, particularly in shared occupancy buildings, and control of access to components such as switches and network management workstations. • It is easy to forget all this in the desire to manage everything remotely.
Controlling access to network management facilities • Network management facilities are key to the security of ATM networks. • Strong two factor authentication is essential. • Ideally, the network management facility should not be connected to the corporate network. • If remote access is essential then the IP network (including servers and gateways) must be configured securely as you would for the most sensitive application.
You can monitor the cable • If a cable is attacked and a tap inserted, it will cause attenuation of the signal. By measuring the levels of light passing through the cable it is possible to detect any deviations from the baseline level. • Devices such as Meson’s FiberGuard monitor light levels and will trigger an alarm if a threshold is reached. They can also be used to protect unlit fibre. • If monitoring is used, it is important to ensure that any circuits used as standby are monitored since a tap may be inserted before they are used.
Encryption • Encryption is the most powerful tool for securing ATM links. It removes the domain of trust from those aspects of the network that are not under your direct control. • It ensures that if the line is tapped, the information will be of no use to the attacker. • It ensures that if an attacker hijacks a PVC they will not be able to insert fraudulent transactions. • It prevents an attacker using PVC hijack to launch further attacks on the corporate LAN. • 3DES encryption at wire speed is available at speeds up to and including OC12.
ATM Encryptor Site 3 • Provide VPN security over ATM networks Site 1 ATM Encryption sits between the ATM and Physical layers
Can you firewall an ATM network? • There is only one commercial ATM Firewall available – the Atlas produced by Bytex. • The traditional role of firewalls is to protect a networked group of computers, or enclave, from traffic coming from an untrusted outside source such as the Internet. ATLAS can perform this job, filtering cells and packets based on policies set by each customer. These policies are expressed in filters that use ATM source and destination, IP source and destination, protocol type, and port number. • The aim of the ATM Firewall is to pre-screen traffic before it reaches a conventional packet Firewall, it does not replace it.
Conclusion - Don’t Panic • If your networks rely totally or in part on ATM connections, you cannot depend on the network to protect your information. • You do not know who is carrying your traffic nor how any switches are involved. • Securing ATM networks is important but not particularly difficult. • A combination of good security practices coupled with strong encryption will enable you to secure your ATM links.