Threat Modeling Digitales Frühwarnsystem Michael Willers
360 likes | 709 Vues
Threat Modeling Digitales Frühwarnsystem Michael Willers. Agenda. Threat Modeling Process overview Get your threats What’s next? Summary. Threat. Asset. loot. Vulnerability. The Core – “Understand”. Understand Know What to Do!. Patrolled!. loot. ggrr!.

Threat Modeling Digitales Frühwarnsystem Michael Willers
E N D
Presentation Transcript
Agenda • Threat Modeling • Process overview • Get your threats • What’s next? • Summary
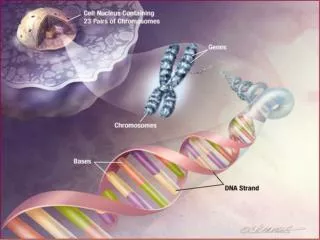
Threat Asset loot Vulnerability The Core – “Understand”
Patrolled! loot ggrr! Understand Know What to Do! Mitigation techniques
Threat Modeling Defined • Security based analysis • Find assets • Uncover vulnerabilities • Identify & evaluate threats • Base for secure design • Most vulnerable parts • Reduce overall security risk • Appropriate mitigation techniques
Threat Modeling Process Identify Assets UnderstandSecurity Entry Points DetermineThreats Use Scenarios Trust Levels System Model Identify Threats Dependencies Analyze Threats
Identify Assets • What to protect? • “For you” valuable things • Examples • Confidential data • Web pages • System availability • Anything that when compromised • prevent correct operation
Identify Entry Points • Where can be attacked? • All system boundaries • Communication interfaces • User • Other systems • Technical examples • Web service, DCOM, RPC • File system, registry, FTP...
Identify Trust Levels • Where are privilege transitions? • Lower higher privileged • Especially at entry points • Cross reference them • Thorough review necessary • Access categories • Different permissionassignments
System Model – Use Scenarios • Understand use cases • Regular users • What system is intended to do! • The adversaries view • Bad guys • What system is not intended to do! • External dependencies • Where stops your “security investigation”?
System Model – Architecture • What does the application? • Use cases, Data Flow Diagram (DFD) • Application architecture diagram • Identify the technologies Trust Boundaries ASP.NET (Process Identity) Alice Microsoft SQL Server IIS Microsoft ASP.NET Mary Bob
Store System Model – Decompose • Decomposition via DFD • Define trust boundaries Interactor B Child (1.1) Child (1.2) Interactor A Child (1.3) Interactor C
Agenda • Threat Modeling • Process overview • Get your threats • What’s next? • Summary
Identify Threats Child1.2.1 STRIDE Threat (Goal) STRIDE STRIDE Threat (Goal) Threat (Goal) KEY Threat Threat Threat DREAD Threat Sub threat Condition Subthreat DREAD Condition Condition Condition DREAD
Identify Threats: Categories • Layers for entry points • Network threats • Host threats • Application threats • Important parts of DFD • Processes & boundaries • Threat categories: STRIDE • Later on: category mitigation
Identify Threats: Documentation • Document threats by using a template: • Leave risk blank – for now ;-)
Damage potential • Affected users • -or- • Damage Threat #1 View payroll data 1.1 Traffic is unprotected 1.2 Attacker views traffic • Reproducibility • Exploitability • Discoverability • -or- • Chance 1.2.1 Sniff traffic with protocol analyzer 1.2.2 Listen to router traffic 1.2.2.1 Router is unpatched 1.2.2.2 Compromise router 1.2.2.3 Guess router password Analyze Threats: Example
Analyze Threats: Rating • Use formula: • Risk = probability * damage potential • Use DREAD to rate threats • Damage potential • Reproducibility • Exploitability • Affected users • Discoverability
Be careful! • Risk = Vulnerabilities * Impact * Probability • Full Trust ASP.NET • Vulnerabilities = 99% (VERY HIGH) • Impact = 80% (High) • Probability = 0.01% (Very Low) • So the Risk is 0.99 * 0.8 * 0.01 • Which is = 0.00792 (i.e. 0.792%) which is either LOW RISK or NO RISK
Agenda • Threat Modeling • Process overview • Get your threats • What’s next? • Summary
Threat Modeling – What’s next? • Threat modeling helps for • Get most “dangerous” portions • Prioritize security push efforts • Prioritize ongoing code reviews • Determine the threat mitigation techniques • Determine data flow ?
Threat Modeling – What’s next? • Architecture & design • Threats will / should affect decisions! • Code against the model • Focus on critical components • Test against the model • Threat based tests • “Attack the system” ?
Threat Modeling – What’s next? • Risk mitigation?? • Option 1: Do nothing • Option 2: Warn the user • Option 3: Remove the problem • Option 4: Fix It Patrolled
NTLM X.509 certs PGP keys Basic Digest Kerberos SSL/TLS Spoofing Authentication Risk Mitigation Process • Identify categoryFor example: Spoofing Threat type (STRIDE) • Select techniquesFor example: Authentication or protect secret data Mitigation technique Mitigation technique Technology Technology Technology Technology • Choose technologyFor example: Kerberos
Summary • Security is all about risk management • Threat Modeling is a process for security driven analysis and design
Uff... Questions?! Michael Willershttp://staff.newtelligence.net/michaelw Senior Software Architectnewtelligence AG