Workstation-Based Traffic Shaping
130 likes | 284 Vues
Presentation by Mark Meiss ( mmeiss@iu.edu ) January 2002. Workstation-Based Traffic Shaping. Motivation. New peer-to-peer file sharing applications emerge regularly The need for traffic shaping is greater than ever How can we limit peer-to-peer traffic without starving out other traffic?.

Workstation-Based Traffic Shaping
E N D
Presentation Transcript
Presentation by Mark Meiss (mmeiss@iu.edu) January 2002 Workstation-Based Traffic Shaping
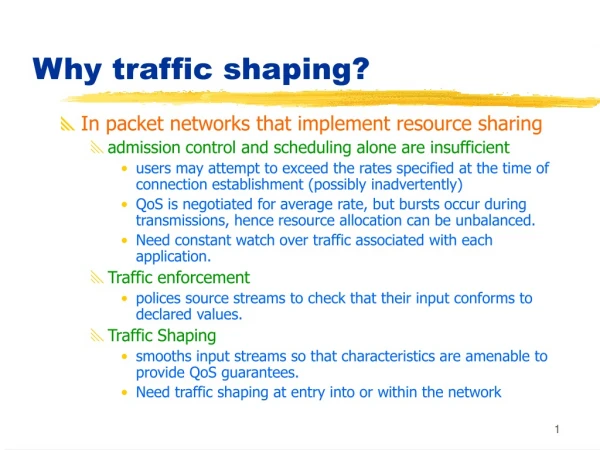
Motivation • New peer-to-peer file sharing applications emerge regularly • The need for traffic shaping is greater than ever • How can we limit peer-to-peer traffic without starving out other traffic?
Problems with Shaping • Many shapers rely on “application signatures” for shaping • Often, a signature is just a port number • Remember learning that port 6699 equals Napster?
The “Port 80” Effect • As traffic shaping becomes more widespread, peer-to-peer applications will start tunneling through TCP port 80 • The traffic we want to shape will become indistinguishable from other traffic • Packet snooping is too difficult and isn’t likely to help in the long term
Our Proposal • Shape traffic based on different factors: • Apparent amount of demanded bandwidth • Destination IP address • Create a “notch filter” so that users of interactive applications suffer the least packet loss • E-mail users shouldn’t notice the congestion
Our Proposal (cont.) • Use BGP routes to classify data according to destination • Don’t worry about port numbers or packet data at all • Our claim: A good PC running an open-source OS can shape traffic at least 200,000 packets/sec
User-Based Model User-Based Mathematical Model of Network Activity
Implementation • Development platform is Pentium III system with 64-bit 66MHz PCI slots, running Redhat Linux 7.2 • Software platform is the “Click” Modular Router: • http://www.pdos.lcs.mit.edu/click/
What Next? • Real-world testing in a few months • Goal is to get as close to Gigabit line rate as possible • Also working on benchmarking performance of Fast Ethernet and Gigabit NICs • Early results suggest large performance differences • Feedback and suggestions for additional shaping parameters are welcome