Anti-Ping Security Demo
Anti-Ping Security Demo. Active Networks Seraphim Security Roy Campbell and Dennis Mickunas University of Illinois at Urbana. Gnip pesky pings. Gnipper Active Network Application. Tasks & Goals. Demonstrate the advantages of active network security Change security dynamically

Anti-Ping Security Demo
E N D
Presentation Transcript
Anti-Ping Security Demo Active Networks Seraphim Security Roy Campbell and Dennis Mickunas University of Illinois at Urbana
Gnip pesky pings... Gnipper Active Network Application
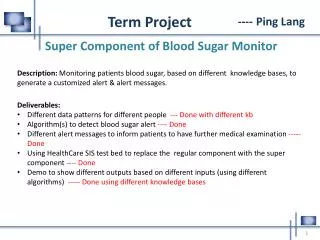
Tasks & Goals • Demonstrate the advantages of active network security • Change security dynamically • Fine grain security control • Security reconfiguration as the packet hops • Show security provisions for Classic examples
Problem Unwanted ping packets and traceroutes require active defense from Gnipper Software
Issues • What does an AN security application look like? • Enforcement: Application level versus Security System level • Authorization, Domain interaction, Granularity, Revocation • Interoperability, Backward Compatibility, Conformance with Architecture
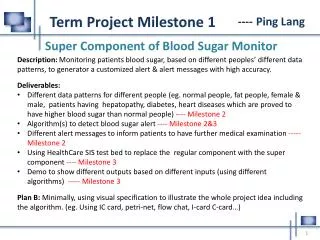
Secure ANTS Node OS Arch Ref Model Active Capabilities EE PART Classic ANTS Seraphim Reference Monitor EE PART Node OS Part Node OS Part Restructured ANTS
Innoculate the network GNIPPER VACCINE
Classic Anet has no security assurance CLASSIC ANET
Classic Anet lacks hop source security identification Security identification CLASSIC ANET
Gnipper traverse Classic Anet to node with security CLASSIC ANET
Now Pings stopped close to source OLD ANET OLD ANET
Broadcast Gnipper CLASSIC ANET
Multicast Gnipper CLASSIC ANET
Issues Exemplified • Masquerading-Can a extra node insert pings? • Impersonation- ping like another? • Replay- Can a node replay a valid ping? • Authorization-When can a principal ping? • Revocation- Can ping rights be removed? • Can security be dynamically reconfigured? • Is Gnipper correct?
Advanced Issues • Identifying capsules and capsule intent? • Functionality -- capability (for method call) versus application code (interpretation of actions) • Non-repudiation of capsule changes and code transformations in routing network • Trust model for network architecture
Status of Project • 1st Draft Active Network Security API conforming to Node Architecture and Security Architecture • Prototype reference monitor complete • Policy enforcement engine • Application Security Insights • Seraphim Active Network Security Demo
Next Steps • Trust Model • Roles and Domains • Approved Security Active Network API • Formal Verification • Demo of Security for Reliable Multicast
News Item SERAPHIM Project at University of Illinois Announces Secure ANTS Roy H. Campbell M. Dennis Mickunas Seraphim announces the availability of a secure ANTS execution environment for the ABONE. Secure ANTS incorporates the Seraphim security reference monitor and conforms to the Active Network Node OS and Active Network Security Architectures. It provides a wide range of security functions and security policies including discretionary access control and active capabilities. "Gnipper", an authenticated security program written for secure ANTS counters ping ANTS programs by revoking the specific user privileges required to perform ping. Gnipper produces a dynamic firewall that advances towards the source of a selected ping activation, preventing ping packets from penetrating beyond the dynamic firewall. Current active network research efforts propose novel network architectures to enable fast protocol and service deployment. However the dynamic and proactive nature of these active networks adds a new dimension to the security risks, and increases the of possibility of attacks by malicious user code. The goal of the Seraphim project is to build security architecture for active networks that is dynamic, reconfigurable, extensible and interoperable. We plan to extend our suite of dynamic security policies using roles and address issues of interoperability across administrative domains. Future security applications are being designed for multicast and to counter a variety of security attacks.