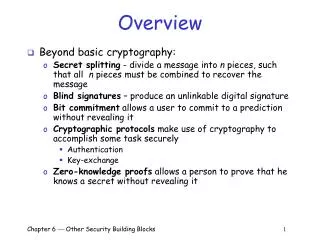
Overview
Overview. Beyond basic cryptography: Secret splitting - divide a message into n pieces, such that a ll n pieces must be combined to recover the message Blind signatures – produce an unlinkable digital signature

Overview
E N D
Presentation Transcript
Overview • Beyond basic cryptography: • Secret splitting - divide a message into n pieces, such that all n pieces must be combined to recover the message • Blind signatures – produce an unlinkable digital signature • Bit commitment allows a user to commit to a prediction without revealing it • Cryptographic protocols make use of cryptography to accomplish some task securely • Authentication • Key-exchange • Zero-knowledge proofs allows a person to prove that he knows a secret without revealing it Chapter 6 Other Security Building Blocks 1
Motivation for Secret Splitting • A professor, Carol, encrypts her grade file with a symmetric-key cryptosystem • Good: only Carol can read grades (privacy) • Good: only Carol can modify grades (integrity) • Bad: if Carol becomes incapacitated nobody else can recover the grades • Carol needs some kind of a mechanism that will allow someone other than her to decrypt the grade file in case of an emergency Chapter 6 Other Security Building Blocks 2
Secret Splitting • Secret splitting makes it possible to divide a message into n piecescalled shadows, such that: • Combining less than n shadows yields nothing • Combining all n shadows yields the message • Carol can split her key into n shadows and give one to n different people she trusts: • Good: if Carol becomes incapacitated all n people can get together and recover the grade file • Good: Unlikely that all n people would betray Carol’s trust Chapter 6 Other Security Building Blocks 3
Secret Splitting Using One-Time Pads • M = “THEKEYISTHREE” • Create four shadows: • Generate n-1 one-time pads (as long as M): • P1 = PDJEUVNSKTUEG • P2 = NBEXUYYKPAQJZ • P3 = ICMKELDAOFGMC • Encrypt M with P1: • C1 = JLOPZUYLEBMJL • T (20) + P (16) mod 26 = J (10) • H (8) + D (4) mod 26 = L (12) • E(5) + J (10) mod 26 = O (15) … Chapter 6 Other Security Building Blocks 4
Secret Split. with One-Time Pads • Encrypt C1 with P2: • C2 = XNTNUTXWUCDTL • Encrypt C2 with P3: • C3 = GQGYZFBXJIKGO • P1, P2, P3, and C3 are the four shadows • Good: all four shadows are required to reconstruct M: • Use P3 to decrypt C3 yielding C2 • Use P2 to decrypt C2 yielding C1 • Use P1 to decrypt C1 yielding M • Bad: What happens if Carol and one of the shadow holders become incapacitated? Chapter 6 Other Security Building Blocks 5
Secret Sharing • Secret sharing (also called a threshold scheme) makes it possible to divide a message into n shadows, such that: • Combining less than k shadows yields nothing • Combining any k (or more) yields the message • Example: • Carol uses a (3-8)-threshold scheme to divide her key into eight shadows (any three required to recover M) • Give three to Alice, one to Bob, two to Dave, and one each to Elvis and Fred • Carol’s key can be recovered by: • Alice (3) • Dave (2) and Bob (1) • Bob (1), Elvis (1), and Fred (1) • Etc. • Good: Need some, not all, shadows to recover the key Chapter 6 Other Security Building Blocks 6
Motivation for Blind Sig’s • Dave owns a bank • Carol has an account at Dave’s bank • Carol wants to withdraw some digital money • Carol would like for the digital money to be: • Valid – it should be accepted as payment by merchants (perhaps after some verification procedure) • Anonymous – Dave should not be able to determine where Carol spends her money • Blind signatures allow Dave to create digital money that is both valid and anonymous Chapter 6 Other Security Building Blocks 7
Blind Signatures • Blind signatures enable a user to digitally sign a document without seeing its contents • Assume Dave’s RSA public/private keys are: • Public: e = 413, n = 629 • Private: d = 53 • Before giving a message, m, to Dave for his signature, Carol can blind it • Choose a random blinding factor, b • 1 <b<n-1 • b is relatively prime to n • Example (using small numbers): m = 250 and b = 5 Chapter 6 Other Security Building Blocks 8
Blind Signatures (cont) • Carol blinds the message: B = (m (be)) mod n B= (250 (5413)) mod 629 B = 172 • Carol gives the blinded message, B, to Dave • Dave cannot read the blinded message because he does not know the blinding factor • If n is large, exhaustive search for b is unfeasible Chapter 6 Other Security Building Blocks 9
Blind Signatures (cont) • Dave signs the blinded message as he would any other message: S’ = Bdmod n S’ = 17253 mod 629 S’ = 168 • Dave sends the signed blinded message, S’, to Carol Chapter 6 Other Security Building Blocks 10
Blind Signatures (cont) • Carol unblinds the signed blinded message by multiplying it by b’s multiplicative inverse modulo n • In our example, b = 5, so b-1 = 126 since (126 5) mod 629 = 1 • Carol computes: S = (S’ b-1) mod n S = (168 126) mod 629 S = 411 • Note that the resulting digital signature, S = 411, is identical to the one that would be produced by Dave signing m = 250 with his private key! Chapter 6 Other Security Building Blocks 11
Properties of Blind Signatures • Validity – as with normal digital signatures: • Anyone can use Dave’s public key to verify his signature on the document is valid • Dave’s signature still cannot be forged or moved to another document, and Dave cannot repudiate his signature • Unlinkability – unlike normal digital signatures: • Dave cannot subsequently link the unblinded signed document to the blind document that he signed Chapter 6 Other Security Building Blocks 12
Unlinkability of Blind Signatures • Suppose: • Carol gives Dave two blinded documents to sign • Dave signs them, returns them to Carol, and keeps copies of the two blind documents • Carol unblinds them and gives Dave copies of the two unblinded documents bearing his signature • Then: • Dave will not be able to determine which unblinded document corresponds to which blinded document Chapter 6 Other Security Building Blocks 13
Example of Unlinkability • Carol gives Dave two blinded documents to sign • B1 = 542, B2 = 492 • Dave signs them, returns them to Carol, and keeps copies of the two blind documents • Carol unblinds them and gives Dave copies of the two unblinded documents bearing his signature • S1 = 217, S2 = 121 • Dave can verify his signature and learn the contents of the documents he signed: • m1 = 217413 mod 629 = 200, m2 = 121413 mod 629 = 100 • Dave cannot link an unblinded document to the corresponding blind document: • B1 = m1 and B2 = m2? • B1 = m2 and B2 = m1? Chapter 6 Other Security Building Blocks 14
Example of Unlinkability (cont) • To link an unblinded document to the corresponding blind document • B1 (542) = m1 (200) and B2 (492) = m2 (100), or • B1 (542) = m2 (100) and B2 (492) = m1 (200) • Dave must determine the blinding factor used to blind each document • Dave can use exhaustive search to find the blinding factors: • b1 = 409 since (100 × 409413) mod 629 = 542 • b2 = 557 since (200 × 557413) mod 629 = 492 • Dave knows that the first blind document he signed, B1, was m2 and the second blind document was m1 • For large values of n, exhaustive search is not feasible and therefore the signatures are unlinkable Chapter 6 Other Security Building Blocks 15
Motivation for Blind Signatures (cont) • Why would Dave sign a blind document that he could not read and create an unlinkable signature? • Recall: • Dave owns a bank • Carol has an account at Dave’s bank • Carol wants to withdraw some digital money • Carol would like for the digital money to be: • Valid – it should be accepted as payment by merchants (perhaps after some verification procedure) • Anonymous – Dave should not be able to determine where Carol spends her money • Blind signatures allow Dave to create digital money that is both valid and anonymous Chapter 6 Other Security Building Blocks 16
Digital Money Without Blind Sig’s • Carol creates a message containing a serial number and a value • Serial number = 603482, Value = $10 • Dave signs the message and deducts $10 from Carol’s account • Carol uses the signed message to pay a merchant • The merchant uses Dave’s public key to verify his signature • The merchant redeems the money with Dave for $10 • Good: Carol’s digital money is valid • Bad: Carol’s digital money is not anonymous • Dave could keep a record each serial number and to whom it was issued • When a merchant redeems digital money Dave could determine to whom that money was issued Chapter 6 Other Security Building Blocks 17
Digital Money With Blind Signatures • Carol creates a message containing a serial number and a value • Serial number = 603482, Value = $10 • Carol blinds the message before giving it to Dave to sign • Dave does not know the blinding factor so he cannot see the contents of the message (e.g. the serial number) • Dave signs the message and deducts $10 from Carol’s account • Carol unblinds the message uses the signed message to pay a merchant • The merchant uses Dave’s public key to verify his signature • The merchant redeems the money with Dave for $10 • Good: Carol’s digital money is valid • Good: Carol’s digital money is anonymous Chapter 6 Other Security Building Blocks 18
Digital Money With Blind Signatures (cont) • Problem #1: double spending • Carol uses her digital money to pay one merchant • The merchant uses Dave’s public key to verify it is valid • Carol uses the same piece of digital money to pay another merchant • The merchant uses Dave’s public key to verify it is valid • Twenty dollars worth of digital money has cost Carol $10 • Solution: merchant must check with Dave and make sure the digital money has not already been spent before accepting it Chapter 6 Other Security Building Blocks 19
Digital Money With Blind Signatures (cont) • Problem #2: fraud • Carol creates a message worth $1000 • Carol blinds the message before giving it to Dave to sign telling him it is worth $10 • Dave does not know the blinding factor so he cannot see the contents of the message • Dave signs the message and deducts $10 from Carol’s account • $1,000 worth of digital money has cost Carol $10 • Solution: Dave needs to be pretty sure of the value of the digital money without actually seeing it (and the serial number) Chapter 6 Other Security Building Blocks 20
Digital Money With Blind Signatures (cont) • Dave requires Carol to create and submit 100 messages: m1 = “Serial number = 935076, Value = $10” m2 = “Serial number = 104766, Value = $10” . . . m100 = “Serial number = 337147, Value = $10” • Carol chooses 100 different blinding factors, b1, b2, …, b100 • Carol uses the blinding factors to create 100 blinded messages • Carol gives all 100 blinded messages to Dave and tells him their value ($10 each in this case) Chapter 6 Other Security Building Blocks 21
Digital Money With Blind Signatures (cont) • Dave chooses 99 of the 100 messages at random to challenge • Dave asks Carol for the corresponding blinding factors • Dave unblinds each of the 99 messages and checks to see that each is worth $10 • If all checks succeed Dave signs the one blind message he did not challenge and returns it to Carol • Carol unblinds the message • Carol now has a valid, anonymous piece of digital money from Dave Chapter 6 Other Security Building Blocks 22
Digital Money With Blind Signatures (cont) • For Carol to get $1,000 worth of digital money for $10 she would have to: • Create 99 messages containing the value $10 • Create one message containing the value $1,000 • Hope that the $1,000 message is the one message that Dave does not challenge • Carol’s chances of succeeding are one in 100 • Dave can lower the odds of fraud by requiring 1,000 or 1,000,000 messages to be submitted Chapter 6 Other Security Building Blocks 23
Motivation for Bit Commitment • Might want to commit to a prediction without revealing it • Chuck and Bill’s virtual coin flips – Scenario #1 • Chuck thinks of a value, either ‘heads’ or ‘tails’ • Bill announces his guess • Chuck tells Bill his value • Problem: Chuck can cheat Bill • Chuck has not committed to a value - he can change it after Bill guesses • Chuck and Bill’s virtual coin flips – Scenario #2 • Bill thinks of his guess • Chuck thinks of a value and announces it to Bill • Bill tells Chuck his guess • Problem: Bill can cheat Chuck • Chuck had to reveal his value in order to commit to it Chapter 6 Other Security Building Blocks 24
Motivation for Bit Commitment (cont) • Chuck and Bill’s virtual coin flips – Scenario #3 • Chuck chooses a value, writes it on a piece of paper, seals it in an envelope, and hands the envelope to Bill • Bill announces his guess • Bill opens the envelope and both learn whether Bill was right • Good: neither can cheat • Fairness requirements: • Chuck must commit to his value in such a way that: • Chuck cannot subsequently change the value • Bill does not learn Chuck’s value until after Bill has guessed Chapter 6 Other Security Building Blocks 25
Bit Commitment • Bit commitment allows someone to commit to a prediction without revealing it • Bit commitment has two phases: • Commitment phase: one party commits to a prediction in such a way that it cannot be subsequently changed • Verification phase: the second party learns the first party’s prediction • Cheating is impossible if: • The prediction cannot be changed after the commitment phase • The prediction is not revealed until the verification phase Chapter 6 Other Security Building Blocks 26
Bit Commitment Using a Symmetric-Key Cryptosystem • Commitment phase: • Chuck chooses a random key, k, and encrypts his prediction • M = Encrypt(p,k) • Chuck gives a copy of M to Bill • Problem: easy for Chuck to change prediction by finding M such that: • Decrypt(M, k1) = 0, and • Decrypt(M, k2) = 1 • Solution: • Bill send a random string of bits, R, to Chuck • Chuck concatenates his prediction to R and then encrypts: • M = Encrypt(“Rp”, k) Chapter 6 Other Security Building Blocks 27
Bit Commitment Using a Symmetric-Key Cryptosystem • Commitment phase: • Bill send a random string of bits, R, to Chuck • Chuck concatenates his prediction to R and then encrypts: • M = Encrypt(“Rp”, k) • Chuck gives a copy of M to Bill • Verification phase: • Chuck sends k to Bill • Bill decrypts M, checks R, and learns p: • Decrypt (M, k) Chapter 6 Other Security Building Blocks 28
Bit Commitment Using a Symmetric-Key Cryptosystem • Neither can cheat: • The prediction cannot be changed after the commitment phase • A good cryptosystem will not allow Chuck to create an M such that: • Decrypt(Rp1,k1) = M • Decrypt(Rp2,k2) = M • The prediction is not revealed until the verification phase • Bill does not know the key Chuck chose and connot read M without it Chapter 6 Other Security Building Blocks 29
Bit Commitment Using a One-Way Hash Function • Commitment phase: • Chuck creates two random strings of bits, R1 and R2 • Chuck concatenates R1, R2, and his prediction, p, and sends the result through the one-way hash function, H: • h = H(R1R2p) • Chuck sends h and R1 to Bill • Verification phase: • Chuck sends R2 and p to Bill • Bill computes the hash: • h’ = H(R1R2p) • Bill verifies that h’ = h Chapter 6 Other Security Building Blocks 30
Bit Commitment Using a One-Way Hash Function • Neither can cheat: • The prediction cannot be changed after the commitment phase • A good one-way hash function will not allow Chuck to create an R1, R2, and p such that there is a collision: • H(R1R2p1) = h • H(R1R3p2) = h • The prediction is not revealed until the verification phase • Since the hash function is one-way, Bill cannot deduce p from h and R1 Chapter 6 Other Security Building Blocks 31
Cryptographic Protocols • A protocol is an agreed-upon sequence of actions performed by two or more principals • Cryptographic protocols make use of cryptography to accomplish some task securely • Example: • How can Alice and Bob agree on a session key to protect a conversation? • Answer: use a key-exchange cryptographic protocol Chapter 6 Other Security Building Blocks 32
Key Exchange with Symmetric Cryptography • Assume Alice and Bob each share a key with a Key Distribution Center (KDC) • KA is the key shared by Alice and the KDC • KB is the key shared by Bob and the KDC • To agree on a session key: • Alice contacts the KDC and requests a session key for Bob and her • The KDC generates a random session key, encrypts it with both KA and KB, and sends the results to Alice Chapter 6 Other Security Building Blocks 33
Key Exchange with Symmetric Cryptography (cont) • Agreeing on a session key (cont): • Alice decrypts the part of the message encrypted with KA and learns the session key • Alice sends the part of the message encrypted with KB to Bob • Bob receives Alice’s message, decrypts it, and learns the session key • Alice and Bob communicate securely using the session key Chapter 6 Other Security Building Blocks 34
Key Exchange with Symmetric Cryptography (cont) • The key-exchange protocol: A: => KDC (A,B); KDC: => A (E(KAB,KA), E(KAB,KB)); A: => B (E(KAB,KB)); Chapter 6 Other Security Building Blocks 35
Key Exchange with Symmetric Cryptography (cont) • Issues: • Security depends on secrecy of KA and KB • KDC must be secure and trusted by both Alice and Bob • KA and KB should be used sparingly • The use of a new session key for each conversation limits the chances/value of compromising a session key Chapter 6 Other Security Building Blocks 36
Attacking the Protocol • Alice and Bob set up a secure session protected by KAB • An intruder, Mallory, watches them do this and stores the KDC’s message to Alice and all the subsequent messages between Alice Bob encrypted with KAB • Mallory cryptanalyzes the session between Alice and Bob and eventually recovers KAB • The next time Alice and Bob want to talk Mallory intercepts the KDC’s reply and replays the old message containing KAB • Alice and Bob conduct a “secure” conversation which is protected by KAB which is known to Mallory Chapter 6 Other Security Building Blocks 37
Attacking the Protocol (cont) A: => KDC (A,B); KDC: => A (E(KAB,KA), E(KAB,KB)); A: => B (E(KAB,KB)); // Alice and Bob encrypt their messages using KAB // Mallory recovers KAB by analyzing Alice and Bob’s session A: => KDC (A,B); KDC: => A (E(KAB’,KA), E(KAB’,KB)); // Mallory intercepts the above message and replaces it M: => A (E(KAB,KA), E(KAB,KB)); A: => B (E(KAB,KB)); // Mallory reads all traffic session between Alice and Bob Chapter 6 Other Security Building Blocks 38
What Went Wrong? • Alice and Bob need to be able to distinguish between a current (or fresh) response from the KDC and an old one • Solutions: • Alice and Bob could keep track of all previously-used session keys and never accept an old session key • KDC could include freshness information in its messages • Timestamps • Nonces Chapter 6 Other Security Building Blocks 39
Using Timestamps to Establish Freshness A: => KDC (A,B); KDC: => A (E((KAB,TKDC),KA), E((KAB,TKDC),KB)); A: => B (E((KAB,TKDC),KB)); Where TKDC is a timestamp from the KDC’s clock and: • Alice and Bob’s clocks are both synchronized with the KDC’s • Alice and Bob both check the KDC’s message to make sure it was generated recently Chapter 6 Other Security Building Blocks 40
Using Nonces to Establish Freshness • A nonce is a randomly-generated value that: • Is never reused • Can be used to prove the freshness of a message A: => KDC (A,B,NA); B: => KDC (A,B, NB); KDC: => A (E((KAB,NA),KA)); KDC: => B (E((KAB,NB),KB)); Chapter 6 Other Security Building Blocks 41
Key-Exchange with Public-Key Cryptography • Alice learns Bob’s public key (by either asking Bob or some third party) • Alice generates a random session key, KAB • Alice encrypts the session key with Bob’s public key • Alice sends Encrypt(KAB,BPublic) to Bob • Bob receives Alice’s message and decrypts it with his private key • Alice and Bob encrypt their subsequent communications with KAB Chapter 6 Other Security Building Blocks 42
Attacking the Protocol • Recall the man-in-the-middle attack • If Mallory can trick Alice into thinking that MPublic is Bob’s public key • Mallory can decrypt Alice’s first message to Bob Encrypt(KAB,MPublic) • Mallory learns the proposed session key KAB • Mallory can send Bob: Encrypt(KAB,BPublic) • Alice and Bob will encrypt their subsequent communications with KAB thinking that it is secure • This is a very serious problem because it’s often difficult to be sure you know somebody’s public key Chapter 6 Other Security Building Blocks 43
The Interlock Protocol • Combating the man-in-the-middle attack: • Alice and Bob exchange public keys • Alice encrypts her message using Bob’s public key. Alice sends half the encrypted message to Bob (e.g. every other bit) • Bob encrypts his message using Alice’s public key. Bob sends half the encrypted message to Alice (e.g. every other bit) • Alice sends the other half of her encrypted message to Bob. Bob puts the two halves together and decrypts them using his private key • Bob sends the other half of his encrypted message to Alice. Alice puts the two halves together and decrypts them using her private key Chapter 6 Other Security Building Blocks 44
The Interlock Prot. (cont) • Foiling the man-in-the-middle: • Assume Mallory can trick Alice into using MPublic instead of BPublic • When Mallory receives the first half of Alice’s message she won’t be able to decrypt it and re-encrypt it with BPublic • Mallory must invent a completely new message, encrypt it and send half of it to Bob • When the second half of Alice’s message arrives, Mallory can put the two halves together, decrypt, and learn what Alice’s original message was • However, Mallory has already committed to the first half of the message and it is too late to change • Therefore, Bob will not get the message Alice sent, and Alice and Bob will probably be able to figure out that there is an intruder between them Chapter 6 Other Security Building Blocks 45
Authentication • Authentication is the process of proving your identity to someone else • One-way • Two-way • Authentication protocols are often designed using a challenge and response mechanism • Authenticator creates a random challenge • Authenticatee proves identity by replying with the appropriate response Chapter 6 Other Security Building Blocks 46
One-way Authentication Using Symmetric-Key Cryptography • Assume that Alice and Bob share a secret symmetric key, KAB • One-way authentication protocol: • Alice creates a nonce, NA, and sends it to Bob as a challenge • Bob encrypts Alice’s nonce with their secret key and returns the result, Encrypt(NA, KAB), to Alice • Alice can decrypt Bob’s response and verify that the result is her nonce A: => B(NA); B: => A(Encrypt(NA, KAB)); Chapter 6 Other Security Building Blocks 47
One-way Authentication Using Symmetric-Key Cryptography • Problem: an adversary, Mallory, might be able to impersonate Bob to Alice: • Alice sends challenge to Bob (intercepted by Mallory) • Mallory does not know KAB and thus cannot create the appropriate response • Mallory may be able to trick Bob (or Alice) into creating the appropriate response for her: A: => M(NA); M: => B(NN); B: => M(Encrypt(NA, KAB)); M: => A(Encrypt(NA, KAB)); Chapter 6 Other Security Building Blocks 48
One-way Authentication Using Public-Key Cryptography • Alice sends a nonce to Bob as a challenge • Bob replies by encrypting the nonce with his private key • Alice decrypts the response using Bob’s public key and verify that the result is her nonce A: => B(NA); B: => A(Encrypt(NA, BPrivate)); • Encrypting any message that someone sends as an authentication challenge might not be a good idea Chapter 6 Other Security Building Blocks 49
One-way Authentication Using Public-Key Cryptography • Another challenge-and-response authentication protocol: • Alice performs a computation based on some random numbers (chosen by Alice) and her private key and sends the result to Bob • Bob sends Alice a random number (chosen by Bob) • Alice makes some computation based on her private key, her random numbers, and the random number received from Bob and sends the result to Bob • Bob performs some computations on the various numbers and Alice’s public key to verify that Alice knows her private key • Advantage: Alice never encrypts a message chosen by someone else Chapter 6 Other Security Building Blocks 50