Anonymity - Background
E N D
Presentation Transcript
Anonymity - Background R. Newman
Anonymity - Beginnings • Early (pre-computer) uses for social reasons (ability to act more freely, have work accepted without prejudice, etc.) • Traffic analysis an issue prior to computers (e.g., Bodyguard of Lies) • Computer TAP solvable with cryptography • With public-key cryptography, theoretical possibility for anonymity and pseudonymity
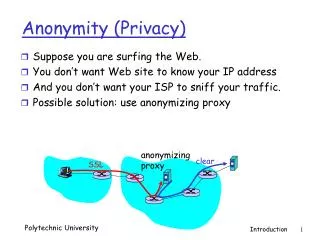
Topics • Defining anonymity • Defining privacy • Need for anonymity • Threats to anonymity and privacy • Mechanisms to provide anonymity • Applications of anonymity technology
Privacy/Anonymity Threats • Available surveillance technology • Identification technology • Increasing use of databases • Data mining • Identity theft • Increasing requirements for I&A • Increasing governmental desire for surveillance
Surveillance Facts • 1.5 million CCTV cameras installed in UK post 911 – Londoner on camera ~300 times a day http://epic.org/privacy/surveillance/ • Face recognition software used in Tampa for Superbowl • 5000 public surveillance cameras known in DC • Home and work zipcodes give identity in 5% of cases in US http://33bits.org/tag/anonymity/
Homework • Count number of video cameras you encounter all day for one day. • Record locations, submit when Canvas up. • Tally total, share total with class Friday.
Data Reidentification • Even ”scrubbed” data can be re-identified • Characteristics within the data (e.g., word usage in documents) • Intersection attacks on k-anonymized database set releases • Use of known outside data in combination with released data • Data mining – higher dimensional space gives greater specificity!
Exercise • What are legitmate limitations on anonymity? • Write down 1-2 of these • Share with neighbor • Share with class
Limitations on Anonymity • Accountability • Legal/criminal issues • Social expectations • Competing need for trust • Others?
Forms of Anonymity • Traffic Analysis Prevention • Sender, Recipient, Message Anonymity • Voter Anonymity • Pseudonymity • Revokable anonymity • Data anonymity
Topics • Defining anonymity • Need for anonymity • Defining privacy • Threats to anonymity and privacy • Mechanisms to provide anonymity • Applications of anonymity technology
Anonymity Mechanisms • Cryptography • Steganography • Traffic Analysis Prevention (TAP) • Mixes, crowds • Data sanitization/scrubbing • k-anonymity