### Efficient File Transfers Over SSH: A Practical Guide ###
In this guide, learn how to efficiently transfer files between two servers using SSH and SFTP. Instead of downloading files to your local machine, which can be time-consuming, you can directly connect to Server B and command it to download files from Server A, drastically reducing transfer times. Experience speeds of up to 3 MB/sec and methods to maintain your privacy online. This tutorial covers connections via terminal and GUI applications like Cyberduck, while also emphasizing security and the importance of responsible usage. ###

### Efficient File Transfers Over SSH: A Practical Guide ###
E N D
Presentation Transcript
File Transfers over SSH James Watt
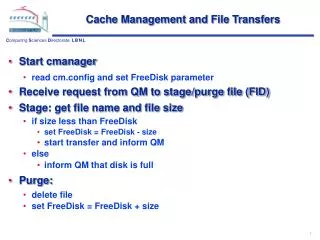
Here is an example of what you might have to do if you wish to copy a file from SERVERA onto SERVERB. For a 800mb file, it would take 39 minutes to dowload and then 3 hours 20 minutes to upload. That’s about 4 hours.
With a shell account, you can log directly into a server. From there, you can give the server commands and it will do them as if you were physically on that machine. Here I connect to Server B with SSH and tell it to download the 800mb file directly from Server A. This removes me from the middle. Since servers are typically on faster connections than your home internet, speeds server to server are quite fast (I’ve got up to 3mbytes/sec before). Now that 800mb file only takes about 6 minutes (BIG DIFFERENCE).
Then I tell it to connect to my server, gtwy.net, via ssh, using the login ‘james’.
Now I’m logged in. Anything I do is being doneas if I was physically at the computer.
Next I will run a texted basedweb browser on gtwy.net so Ican connect to apple.com anddownload the 800mb installerfor xcode. Not only will this be muchquicker, but my IP address andidentity will be hidden from theApple server.
Next I will demonstrate how to connect to oneserver and move files to another using SFTP(Secure File Transfer Protocol).This is different than the last example becausewe are sending instead of receiving.
Notice how these servers are alsoaccessible via the web browser.Not all servers run a webserverdaemon, but mine have apacheinstalled to make it easier toaccess files and data in locationsthat I can’t connect in via ssh.
Next I will use a program named “Cyberduck”to sftp gtwy.net from my local computer. Thisis a direct upload from me to the server, andit is done with a GUI application rather thanthrough the command line.
It’s hard to mask your identity over theinternet, but by connecting through ashell you are able to hide. Any program you run on your server,may it be an IRC client, a BitTorrentdownload, or an attack on a website, It will only trace backto the server. Donot use this to try to get away withsomething illegal, because the FBI willget search warrants, take your server,and use the log files to find you. In this example I log into IRC over theserver and do a “/whois” of my login.It says my IP address, but the addressit thinks I am belongs to gtwy.net, notmy laptop.