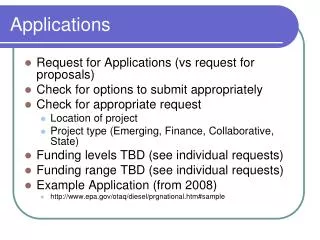
Applications
Applications. Common Distributed applications include:. E-mail . Web browsing. Digital Audio. RTP/RTCP. Voice over IP. File transfer. Remote Login. Mail Service (SMTP). Suppose that Jane Doe at marist.edu wishes to send an e-mail to elvis.presley@graceland.com


Applications
E N D
Presentation Transcript
Applications Common Distributed applications include: E-mail Web browsing Digital Audio RTP/RTCP Voice over IP File transfer Remote Login
Mail Service (SMTP) Suppose that Jane Doe at marist.edu wishes to send an e-mail to elvis.presley@graceland.com The (S)imple (M)ail (T)ransfer (P)rotocol will work as follows:
SMTP • Jane invokes her e-mail service on her local machine. • Jane supplies Elvis’s e-mail address, composes a message, and instructs the SMTP user agent (e-mail service) to send the message. • The message is sent to Jane’s mail server and placed in a queue. • The client side of SMTP, running on Jane’s mail server, uses DNS to locate the destination mail server. • Jane’s mail server opens a TCP connection to the SMTP server at the destination. Jane’s SMTP client sends the message into the TCP connection. • Elvis’s SMTP server receives the message and places it in Elvis’s mailbox. • An Elvis impersonator reads the message at his convenience.
IP header SMTP agent SMTP (client) SMTP (server) TCP header SMTP header TCP TCP TO: elvis@graceland.com Dear Elvis, I don’t believe you’re really dead. Please reply. Love, Jane Doe Text of Message IP IP SMTP Jane’s Local Host Jane’s Mail Server Elvis’s Mail Server 1. Jane invokes her local SMTP agent 2. Jane constructs e-mail message 6. Elvis’s Mail Server receives e-mail and puts it in his mailbox 3. Jane sends e-mail to her mail server for delivery 4. Jane’s Mail Server establishes a TCP connection with Elvis’s 7. TCP Connection is terminated 5. Mail is delivered via a sequence of TCP packets exchanges
SMTP Exchange of SMTP messages after an initial TCP handshake Sender: Client (Jane’s Mail Server) MAIL FROM: <jane.doe@marist.edu> Sender’s e-mail address is supplied Client (Jane’s Mail Server) RCPT TO: elvis@graceland.com Identifies the Receiver’s URL Client (Jane’s Mail Server) . Period on separate line signifies the end of message Client (Jane’s Mail Server) I can’t believe you’re really dead. Please reply. Love, Jane Doe Server (Elvis’s Mail Server) 250 Hello marist.edu SMTP Connection message acknowledged Client (Jane’s Mail Server) DATA Ready to send data • Server (Elvis’s Mail Server) • elvis@graceland.com …Recipient ok • Acknowledges previous message and indicates a valid recipient on this mail server Server (Elvis’s Mail Server) 354 Enter mail, end with “.” on sep. line Ready to receive message Server (Elvis’s Mail Server) 250 Message accepted for delivery Acknowledges receipt of the e-mail Server (Elvis’s Mail Server) 221 graceland.com closing connection SMTP connection with indicated MS closed • Server (Elvis’s Mail Server) • jane.doe@marist.edu • Sender’s URL Received ok Client (Alice’s Mail Server) QUIT Indicates no more e-mails to transmit Client (Jane’s Mail Server) HELO marist.edu SMTP Connect from (Mail Server ID) Server (Elvis’s Mail Server) Message: 220 graceland.com Meaning: Connection established with mail server ID
MIME Extensions for non-ASCII data MIME (Multipurpose Internet Mail Extensions) headers must be affixed to messages containing non-7-bit ASCII characters and multimedia) Two important MIME headers are Content-Type: Content-Transfer-Encoding: Content-Transfer-Encoding: alerts the receiving agent for e-mail that the message has been ASCII-encoded and identifies the encoding used. Content-type: indicates that the message contains non-textual data
MIME Extensions Consider the following mail message: From: yvonne@crepes.fr To: elvis@graceland.com Subject: Picture of me MIME-Version: 1.0 Content-Transfer-Encoding: base64 Content-Type: image / jpeg Cher Elvis, je t’aime beaucoup. J’envoie un photographie de moi. Avec beaucoup d’amour, Yvonne . (jpeg image here)
MIME Extension Received message Received: from crepes.fr by graceland.com; 23 April 08 15:24:39 GMT From: yvonne@crepes.fr To: elvis@graceland.com Subject: Picture of me. MIME-Version: 1.0 Content-Transfer-Encoding: base64 Content-Type: image/jpeg Cher Elvis, Je t’aime beaucoup. J’envoie un photographie de moi. Avec beaucoup d’amour, Yvonne . (image begins here)
Mail Delivery – POP3 Message transfer agent POP3 User agent SMTP POP3 Internet Client PC mailbox Sending Host ISP Host
User agent User agent SMTP SMTP POP3 Jane’s Mail Server Elvis’s Mail Server Jane Elvis’s Ghost Mail Delivery – POP3 • Jane’s MS delivers the e-mail to • Elvis’s MS 2. Jane sends e-mail to her MS 4. Elvis reads Jane’s e-mail 1. Jane composes e-mail for Elvis
POP3 Mail Access Protocol Suppose Elvis directly accesses his POP3 Server via telnet telnet graceland.com 110 # POP3 sever on port 110 +OK POP3 server ready user elvis #begin login authorization +OK pass hounddog +OK user successfully logged on #sequence and size of each msg. list • 424 • 1262 • . # MS indicates two msgs. for this user #list end with period on separate line
POP3 Mail Access Protocol (cont.) retr 1 #retrieve (copy of) first msg. From: jane.doe@marist.edu To: elvis@graceland.com Subject: I can’t believe you Dear Elvis, I can’t believe you are really dead. Please reply. Love, Jane Doe . dele 1 quit +OK POP3 server signing off
Mail Access Protocols The POP3 has the virtue of being simple and easy to implement, but it does not carry state information across separate sessions. IMAP IMAP allows the mail client to: Manipulate remote mailboxes as if they were local Can create and maintain multiple message folders Can put messages in folders and move messages between folders Allow the client to retrieve components of a message Can obtain the message header or just one part of a multipart msg. IMAP must maintain a persistent folder hierarchy for each user
Browser Browser HTTP SMTP HTTP SMTP client 2. Message is sent via HTTP to sender’s mail server 3. SMTP message sent to receiver’s mail server 4. Receiver accesses his mailbox using http Mail Access Protocols Internet Mail SMTP client 1. Sender creates an e-mail message at her browser
HTTP Nonpersistent Connection Suppose that Jane Doe wishes to access Elvis’s web site to get a list of his million seller hits. Here is the sequence of steps that follow for a nonpersistent connection. 1. Jane opens her browser (on her local PC) and connects to her internet access point. 2. Jane supplies the URL http://www.graceland.com/greatest-hits.html and the DNS name server at Jane’s access point determines the corresponding IP address.
HTTP Nonpersistent Connection (continued) 3. The HTTP client (Jane) initiates a TCP connection to the server www.graceland.com. Port number 80 is used as the default port for HTTP clients by Elvis’s web server. 4. The client sends an HTTP request message to the server via the socket established in the previous step. The message will read: GET /greatest-hits.html HTTP/1.1 Host: www.graceland.com Connection: close User-agent: Mozilla/4.0 <CR><LF> #nonpersistence #browser used by client
HTTP Nonpersistent Connection (continued) 5. The HTTP server receives the request message via the associated socket, retrieves the requested object from storage, encapsulates it in an HTTP response message (shown below), and sends it to the client. HTTP/1.1 200 OK Connection: close Date: Mon, 09 Sep 2002 15:16:33 GMT Server: Apache/1.3.0 (Unix) Last-Modified: Wed, 24 Jul 2002 09:24:21 Content-Length: 6824 Content-Type: text/html <CR><LF> (data, data, ….., data)
HTTP Nonpersistent Connection (continued) 6. The HTTP client receives the response message with the Connection close command. The client extracts the file from the response message, parses the HTML file, and finds references to JPEG objects. 7. Steps 2 – 5 are repeated for each referenced jpeg object (with appropriate modifications to the specific illustration)
HTTP Browser Browser Helper Base code Plug-in Client Machine Client Machine Server returns some MIME type information with the HTML page to tell the browser how to display the page
Status Line version sp status code sp phrase CR LF header field name : value CR LF header field name value CR LF CR LF HTTP Response Message Format Header lines : Message body
version header field name value Header Lines HTTP Response Message Format Example Status Line HTTP/1.1 200 OK Connection: close Date: Mon, 09 Sep 2002 15:16:33 GMT Server: Apache/1.3.0 (Unix) Last-Modified: Wed, 24 Jul 2002 09:24:21 Content-Length: 6824 Content-Type: text/html <CR><LF> (data, data, ….., data) status code phrase
TCP header HTTP header HTTP header TCP header HTML data HTML data HTML file TCP header HTML data Delivery of Web page – the server side The application message is broken into separate TCP packets – which are delivered (via IP) to to the destination – reassembled – and handed up to the HTTP application process
TCP header HTTP header HTTP header TCP header HTML data HTML data HTML data TCP header HTML data TCP buffer Delivery of Web page – the client side TCP packets reassembled for delivery to HTTP application
HTTP Non-persistent connection Suppose a requested Web page contains 3 embedded jpeg files and that the original html file and the three jpeg files each require 7 TCP packets with a 3-way handshake and slow start for each file transferred. (Best case scenario for non-persistence) Activity Total RTTs 3-way handshake + request 2 Packet 1 3 Packets 2 & 3 4 Packets 4-7 5 20 Repeat 3 more times
HTTP persistent connection Assume the same situation as described previously, but with a persistent connection, with pipelining, and again a best case scenario. Activity Total RTTs 3-way handshake 2 Packet 1 (with ack) 3 Packets 2 & 3 4 Packets 4-7 5 First jpeg file packets 1-7 6 Remaining jpeg files (14 pkts) 7
HTTP Caching Often during a session or across recent sessions, the client will access the same web page numerous times. The number of file transfers can be reduced by caching. Caching of web files is complicated by the following factors: Web files are updated frequently, and Web structure (links) is changed in real time
HTTP Caching The Conditional Get Step 1. User requests an uncached object from a web server Step 2. The Web server responds with an object to the client Step 3. The object is transferred to the client and displayed Step 4. One week later the client (on same PC) requests this object Step 5. Web server sends a response to the client Step 6. Client uses cached copy of the object HTTP/1.0 200 OK Date: Wed, 24 Jun 2002 17:21:03 Server: Apache/1.3.0 (Unix) Last-Modified: Wed, 24 Jun 2002 15:24:47 Content-Type: text/html (data, data, …,data) Local host still retains a copy of the file in its cache. Browser sends: GET /~jzbv/MasterMethod.htm HTTP/1.0 User-agent: Mozilla/4.0 The object (html file) is also saved in the local cache of the client HTTP/1.0 304 Not Modified Date: Wed, 01 Jul 2002 14:23:37 Server: Apache/1.3.0 (Unix) New date (Wed, 01 Jul 2002 14:23:37) is stored with cached object GET /~jzbv/MasterMethod.html HTTP/1.0 User-agent: Mozilla/4.0 If-modified-since: Wed, 24 Jun 2002 17:21:03 Note! On the Server Side, the most recently used pages will be cached in Main memory to avoid costly disk accesses whenever possible
GET tours/cancun.htm HTTP/1.0 User-agent: Mozilla/4.0 If-modified-since: (date cached) HTTP/1.0 304 Not Modified Date: (today) Server: Apache/1.3.0 (Unix) GET /tours/cancun.htm HTTP/1.0 User-agent: Mozilla/4.0 Client Proxy server (Web Cache) Web Server HTTP Caching Web Caches Proxy Server sends cached copy to client and updates time accessed Web server responds to conditional Get request Proxy server relays request to the specified Web Server User sends request for Web page to local Proxy server
Digital Audio MP3 (MPEG Layer 3) Audio Compression Main Rule – Don’t encode anything nobody’s going to hear anyway!! • MP3 is based upon Perceptual coding • If a loud sound in a frequency band masks a softer sound, don’t encode the softer sound. • Even after the louder sound has stopped, the ear will take a short period to recover, so don’t start encoding the softer sound before the ear is ready to hear it. • At each frequency there are amplitudes that the ear will not pick up, so don’t encode sounds below this threshold of audibility.
Digital Audio Waveform coding (Fourier transform) is performed to get the power at each frequency. (The signal is sampled at 32 kHz, 44.1 kHz, or 48 kHz Next an output bit rate is chosen. MP3 can compress a rock ‘n roll CD down to 96 kbps. For a classical Piano Concerto, at least 128 kbps are required. (Classical requires a higher bit rate in part because of a lower S/N ratio.) The samples are processed in groups of 1152 (about 26 msec each). Each group is passed through 32 digital filters to get the signal contribution in 32 different frequency bands. The signal is also fed into a psychoacoustic model to determine the masked frequencies. The available bit budget (number of bits allocated to a group to achieve the desired output) is divided among the 32 bands according to the previously stated rules. Finally, Huffman encoding is used to compress the transmitted output.
1, 2 Web Server Media Player 6 Browser 4 7 5 3 Disk Disk Streaming Audio • Establish TCP connection • Browser starts media player • Send HTTP GET request • Media playerreads meta file, gets URL of audio server, and gets song • Server gets meta file from disk • File sent to client • Browser writes metafile to scratch file on disk
Audio Streaming Role of the Media Player • Manage the user interface • Handle transmission errors • Decompress the music • Eliminate jitter
lost Audio Streaming To reduce error, music may interleave successive small packets of odd and even samples. A packet might contain 220 stero samples, each containing a pair of 16-bit numbers, normally good for 5 msec of music, but each alternate packet will contain 10 msec of odd and even samples. In the illustration below, loss of the fourth packet results in some degradation of the quality of the transmission, but no gap in the music. The media player will interpolate the missing pieces.
Command Server Action Audio Streaming RTSP – Real-Time Streaming Protocol RTSP Establishes a logical (virtual) connection between the Media Player and the Media Server that provides for the exchange of control (not data) packets that allow the player to have “remote control” over the server. The main RTSP Commands List media parameter DESCRIBE SETUP Establish a logical channel between player and server PLAY Start (Resume) sending data to the client RECORD Start accepting data from the client PAUSE Temporarily stop sending data TEARDOWN Release the logical channel
RTSP Media Server Control Media Player Media Server RTP Low-water mark High-water mark Audio Streaming A Push server will continuously deliver data at the playback speed or in excess of it. It may deliver data faster than the playback speed to allow for periods of congestion when it will not be able to maintain the requested rate. The media player can maintain a buffer with a high-water and low-water mark. When the buffer is above the high-water mark the player will send a PAUSE command to the server and reactivate it with a PLAY command when the level of data in the buffer reaches the low-water mark.
Multimedia Application User Space RTP Socket Interface UDP IP OS Kernel Ethernet RTP – Real-Time Transport Protocol RTP provides a transport service for a variety of real-time applications BUT It resides in the User space (Application Layer) of the protocol stack Server Multimedia Application consists of multiple video, audio, text streams that are fed intoRTP library. RTP library multiplexes these streams and encodes them in RTP packets, which are delivered as UDP datagrams Client RTP packets are delivered from the OS, and the RTP library demultiplexes the various streams and delivers them to the appropriate multimedia application.
RTP Header bits Ver. P X CC M Payload type Sequence Number Timestamp Synchronization source identifier Contributing source identifier Version – already version 2 only one opportunity for additional improvements P – indicates that the packet has been padded (to a multiple of 4-bytes) X – indicates that an extension header is present CC – Specifies how many contributing sources are present (up to 15) M – application-specific marker bit Payload type – tells which encoding algorithm is used, for example MP3 Sequence Number – numbers packets, not bytes
RTP Header, Continued Timestamp – indicates when the first sample in the packet was made. Timestamps are relative to the start of the stream. (This allows the destination to buffer and play each packet at the right number of milliseconds after the start of the stream. Synchronization source identifier – indicates to which stream the packet belongs. It provides for the multiplexing and demultiplexing of multiple streams onto a single stream of UDP packets. Contributing source identifier(s) – (if any) are used when mixers are used in the studio – the streams being mixed are listed here.
RTCP – Real-time Transport Control Protocol RTCP provides feedback on properties such as delay, jitter, congestion, bandwidth, etc. to the source. It does not transport any data! By providing regular feedback, the encoding algorithm can be regularly adapted to provide the best quality of service possible within the current environment. RTCP also handles in-stream synchronization. Different streams may use different clocks with different granularities and drift rates. RTCP is used to keep them in synch. RTCP provides a mechanism for naming the various sources which can be displayed on the receiver’s video screen. RTCP makes multimedia traffic using RTP adaptive!
Voice over IP In 1999 the number of data bits delivered equaled the number of voice bits (PCM) moved. By 2002, it was an order of magnitude greater, and growing exponentially. Since the fraction of the bandwidth used by voice was becoming negligible, and yet the average customer charge for phone service was larger than the cost for Internet service, the data network providers saw an opportunity to make a large amount of money with little additional cost by providing phone service. Requirements for a telephone network • A protocol for encoding and decoding speech (ex. PCM) • A protocol for allowing stations to negotiate which encoding will be used • A protocol for establishing and releasing connections • A protocol for regulating bit rate • A protocol for communicating with a gatekeeper (if present) (H.225) • A protocol for the actual data transmission (RTP/RTTCP)
Internet Telephone Network 11. When a party hangs up, the Q.931 call signaling channel is used to tear down the connection. When the call is terminated, the calling PC sends an RAS message to the gatekeeper to release the bandwidth. 10. Full duplex data flow now begins using RTP/RTCP 9. Subsequent packets bypass the gatekeeper and go directly to the gateway’s IP. H.245 is used to negotiate parameters of the call. It uses the H.245 control channel which is open for duration of the call 8. When called party picks up, the end office sends a Q.931 CONNECT mssg to signal the PC that it has a connection. 6. Gatekeeper responds with Q.931 CALL PROCEEDING msg to PC and forwards SETUP to the gateway 2. PC learns gatekeeper’s IP address and sends RAS to register 5. PC sends Q.931 SETUP message over the TCP connection. Message contains the phone number (or IP address, port, if PC is being called 7. The gateway then makes an ordinary telephone call to the desired phone. End office sends Q.931 ALERT mssg to PC to indicate ringing 4. After bandwidth has been granted, call setup begins. PC establishes TCP connection to gatekeeper to begin setup The H.323 Architectural Model PC on a LAN calling a remotephone Gatekeeper Gateway Zone 1. Workstation sends UDP gatekeeper discovery packet to port 1718 3. After PC registers it sends gatekeeper RAS admission msg requesting bandwidth
Speech Control G.7xx Q.931 (call signaling) RTCP RTP The H.323 Protocol Stack H.225 (RAS) H.245 (call control) UDP TCP IP Data Link and Physical protocols RAS = Registration/Admission/Status G..711 = PCM
File Transport Protocol (FTP) A Web server is “promiscuous” • The set of authorized clients may or may not be restricted • It contains a collection of attractively formatted files and transfers copies of these files upon the request of any authorized user. • Authorized clients may only extract copies of stored files – they cannot add to the existing collection • Requested files are displayed on the client’s local machine Web pages are attractively packaged, prominently advertised, and available to be displayed to any and all (authorized) clients
FTP A File Transfer Protocol differs from HTTP in the following: • An FTP client must be an authorized user on both the local and remote file system • Files can be transferred from the local to the remote file system (up loading) or from the remote to the local (down loading) • State information, such as current directory, must be maintained • Files are transferred, not displayed FTP is a private service for a highly restricted set of authorized clients
FTP FTP control services • User identification • Password verification • Create and remove directories in remote file system • Change directory in remote file system • “put”files – transfer from local to remote file system • “get”files – download file from remote directory to local directory • Delete files in the remote file system FTP establishes two parallel TCP connections to transfer a file • A control connection on port 21 • A data connection on port 20 FTP sends its control information “out of band”
FTP client FTP user interface FTP server Remote file system Local file system FTP TCP control connection port 21 TCP data connection port 20
FTP Sequence of Commands: # user ID USER elvis 331 Username OK, password required. PASS hounddog 230 User logged in, proceed. # change directory to pathname CWD greatest_hits/song_lyrics 250 Requested file action OK, completed. STOR allshookup.txt 150 File status OK; about to open data connection. 226 Closing data connection. Requested file action successful. QUIT 221 Service closing control connection. Logged out if appropriate.
FromUser ToServer FromServer Client: ToServer.writeBytes(request) Server: FromServer.writeBytes(mssg) TCP Sockets TCP connection setup Server socket Request for Web page Connection socket Delivery of Web page Server: listenSock = new ServerSocket(12) Client Socket Client: clientSocket = new Socket(host,12) Server: connectSock.close() Server: connectSock = listenSock.accept()