POST-QUANTUM CRYPTOGRAPHY- KNOWING THE UNKNOWN CYBER WORLD -USCSI
0 likes | 11 Vues
Build a thriving cybersecurity career with top cybersecurity certification programs. Earn skills in post-quantum cryptography and related nuances without fuss!<br><br>Read more: https://shorturl.at/yJgwx

POST-QUANTUM CRYPTOGRAPHY- KNOWING THE UNKNOWN CYBER WORLD -USCSI
E N D
Presentation Transcript
POST-QUANTUM CRYPTOGRAPHY KNOWING THE UNKNOWN CYBER WORLD © Copyright 2024. United States Cybersecurity Institute (USCSI ). All Rights Reserved. ® www. uscsi nstitute.org
“ The Post-Quantum transition is an imminent challenge that the global IT industry must be prepared to confront ” -Douglas Stebila Associate Professor, Cryptography @University of Waterloo, Ontario, Canada POST-QUANTUM RAGEON! Are you all in yet? THE IS Quantum computers, Sycamore, are so powerful that they can perform calculations in a few hundred seconds; that a traditional supercomputer would take 10,000 years to do (Google Research). Demonstrating such exemplary potential is not a matter of sheer luck. It goes to the decades of smart AI evolution that have triggered such a great expanse of technology around the world. © Copyright 2024. United States Cybersecurity Institute (USCSI ). All Rights Reserved. ® www.uscs institute .org
TRADITIONAL VS QUANTUM COMPUTING QUANTUM COMPUTING CLASSICAL COMPUTING vs 1 Calculates with qubits, which can represent 0 and 1 at the same time Calculates with transistors, which can represent either 0 or 1 0 0 1 Power increases exponentially in proportion to the number of qubits Power increases in a 1:1 relationship with the number of transistors Quantum computers have high error rates and need to be kept ultracold Classical computers have low error rates and can operate at room temp 1 0 1 0 Well suited for tasks like optimization problems, data analysis, and simulations Most everyday processing is best handled by classical computers AI Understanding the Quantum ecosystem is a must as you plan to tread forward with greater cybersecurity frameworks. Looking deep into the way these genius quantum computing machines and cryptographic techniques work is a work of art and indeed requires every ounce of curiosity and integrity to master these nuances for a thriving cybersecurity career. in © Copyright 2024. United States Cybersecurity Institute (USCSI ). All Rights Reserved. ® www.uscs institute .org
HOW POWERFUL IS THE QUANTUM COMPUTING MECHANISM? Quantum computers hold the hope of the future computing generations. Quantum computers can "skip over" the linear journey through every pathway by using quantum mechanics to simultaneously consider all possible outcomes. Quantum computing works with probabilities rather than binaries. This form of computing allows for solutions to problems that are too large or too complex to solve in any reasonable time by a classical computer. Where a classical computer can sort through and catalog large amounts of data, it cannot predict behavior within that data. POPULAR USE CASES OF QUANTUM COMPUTING Quantum Chemistry Artificial Intelligence and Machine Learning Grid Optimization Financial Modeling and Portfolio Optimization Cryptography and Data Security Traffic Optimization and Smart Cities Drug Discovery and Development Weather Forecasting and Climate Modeling Design Optimization Material Science and Design Quantum in Space Protein Folding Supply Chain and Inventory Optimization Disease Risk Predictions UNDERSTANDING QUANTUM THREATS cybersecurity risks that could render ineffective encryption tools used to protect data, These are the transactions, and beyond. Quantum computers are efficiently equipped to break encryption methods at an alarming speed, making them a threat to data security. © Copyright 2024. United States Cybersecurity Institute (USCSI ). All Rights Reserved. ® www.uscs institute .org
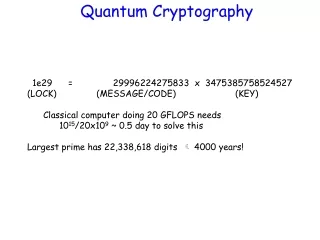
HOW DOES QUANTUM THREATEN CRYPTOGRAPHY? Quantum computing, possessing unparalleled computational power, poses a significant risk to the cryptographic protocols safeguarding our digital realm. Current cybersecurity cornerstones, such as RSA and ECC algorithms, are vulnerable to quantum advancements. These risks are rapidly shifting from theoretical to tangible due to swift progress in quantum computing. Addressing these threats demands multifaceted efforts: developing new designs and implementing novel algorithms and protocols. This process necessitates specialized skills, substantial time, and resources. With the urgency of these developments, it is imperative to act promptly, recognizing the extensive work that lies ahead. Looking at the grave urgency, it is imperative to reflect upon these questions before you pivot and try to mitigate Quantum threats. States' Regulations? Physical/Logical Attacks? Cryptanalysis? Error Computations? Navigating the quantum shift Number of Qubits? Algorithms/ Protocols? Assets Type/Life Duration? Cost/Time to Migrate? This leads you to understand that the entire gamut of quantum resistance is crucial to quantum security resistance. It involves developing secure algorithms and protocols that can withstand attacks using quantum, classical computers, and a combination of both. Quantum-resistant technologies are key to safeguarding IoT devices and ecosystems, ensuring data safety, and protecting digital assets against these emerging threats. QUANTUM CRYPTOGRAPHY PRE-QUANTUM CRYPTOGRAPHY POST-QUANTUM CRYPTOGRAPHY AKA Quantum Encryption; refers to various cybersecurity methods for encrypting and transmitting secure data based on the naturally occurring and immutable laws of quantum mechanics. A type of cryptography that uses algorithms to convert human- readable data into secret code A field of cryptography that aims to develop algorithms that are resistant to attacks from quantum computers. © Copyright 2024. United States Cybersecurity Institute (USCSI ). All Rights Reserved. ® www.uscs institute .org
POST-QUANTUM CRYPTOGRAPHY- TYPES CODE-BASED Uses error-based code for encryption. HASH-BASED Among the most secure PQC methods but the slowest as well; that scrambles variable length data as fixed-length values. POST-QUANTUM CRYPTOGRAPHY (PQC) f(x) MULTIVARIATE POLYNOMIAL Quickest method with least security offered. LATTICE-BASED One of the most secure PQC encryption methods that uses lattice-related mathematical issues. POST-QUANTUM CRYPTOGRAPHY ALGORITHMS These are powerful cryptographic algorithms that are designed to be secure against quantum computers. The best mitigation against the threat of quantum computers to traditional public key cryptography (PKC) is post-quantum computing (PQC). Also popularly known as 'Quantum Safe cryptography' or 'Quantum-resistant cryptography'; PQC algorithms will replace the vulnerable PKC algorithms used today for both key establishment and digital signatures. The security of PQC algorithms is based on mathematical problems that are believed to be intractable for both classical and quantum computers. These algorithms will not necessarily be drop-in replacements for the current PKC algorithms in protocols or systems, so system owners should begin planning for the migration to PQC. © Copyright 2024. United States Cybersecurity Institute (USCSI ). All Rights Reserved. ® www.uscs institute .org
Some of the popular PQC algorithms are: Lattice-based Cryptography NTRU: Based on the problem of finding a short vector in a special type of lattice called Cyclotomic lattice LWE (Learning with Errors): Involves distinguishing between random linear equations and the ones with noise Ring-LWE: A variant of LWE, operating over polynomial rings for efficient implementation of lattice-based cryptography Code-based Cryptography McEliece: Based on the problem of decoding a random linear code Goppa: A type of code-based cryptography; that uses Goppa codes Multi-variate Cryptography f(x) Matsumoto-Imai: Based on quadratic equation problem-solving methods, it resolves public-key encryptions UOV (Unbalanced Oil and Vinegar): Used for public-key encryption and digital signatures Hash-based Cryptography XMSS: Based on the Merkle Tree Data structure; used for digital signatures SPHINCS: Family of hash-based signature algorithms best for security and performance trade-offs Super-singular Isogeny Cryptography SIDH: Perfect for key exchange and digital signatures © Copyright 2024. United States Cybersecurity Institute (USCSI ). All Rights Reserved. ® www.uscs institute .org
Wonder what makes Gartner say “ Quantum Computing will render traditional Cryptography UNSAFE by 2029 ” WHY POST-QUANTUM CRYPTOGRAPHY TRANSITION AN URGENT PRIORITY? 2022 2023 2024 2025 2026 2027 2028 2029 2030 Current Transition Ongoing Build cryptographic metadata database Build crypto policies for next phase Lifeboat exercise for data (L/M/S term use) Plan transition phase plan Implement transition plan Purge useless/expired data with weak crypto Implement transitional crypto policies Implement crypto- agile application development & move to production End of life nonagile applications Enforce strong crypto polices for data Vet and test new PQ crypto policies algorithms Full transition to CCOE Start crypto-agile dev strategy (e.g., CCOE) Source: Gartner Quantum Cryptography Timeline; as explained by Gartner; stresses the urgent need to switch to the next generation of data protection with post-quantum cryptography in the spotlight. Asymmetric encryption is in almost all software, billions of devices worldwide, and most of the communications over the internet. Yet by 2029, advances in quantum computing will make asymmetric cryptography unsafe and by 2034 fully breakable. "Harvest-now, decrypt-later" attacks may already exist. To resist attacks from both classical and quantum computers, organizations must transition to post-quantum cryptography. © Copyright 2024. United States Cybersecurity Institute (USCSI ). All Rights Reserved. ® www.uscs institute .org
CHALLENGES IN POST-QUANTUM CRYPTOGRAPHY ADOPTION However, the road ahead is quite challenging. While; many organizations have not yet planned or budgeted for this shift. Many governments are already issuing mandates and legal frameworks for organizations to put in place a post-quantum cryptography strategy. you need to address the following listed hurdles that may retard your growth with time. Difficulty Finding Replacements: No drop-in alternatives exist for current cryptographic algorithms. This creates the need for discovery, categorization, and reimplementation Organizational Incompetence: Few organizations know how their cryptography works, where keys and algorithms are used, or how secrets are stored and managed. Diverse Performance Requisites: New algorithms have different performance characteristics than asymmetric ones. Key and ciphertext sizes are larger, for example, and encryption and decryption times are longer. This may impact performance and require restating or rewriting of current applications. Vendors Lack Preparedness: Do not assume that your vendors are equipped to handle post- quantum cryptography. Most are unprepared to upgrade and may not recognize that they need to unless you push them. © Copyright 2024. United States Cybersecurity Institute (USCSI ). All Rights Reserved. ® www.uscs institute .org
WAY TO QUANTUM RESISTANCE IMPLEMENTATION PLAN MIGRATION TO QUANTUM-RESISTANT CRYPTOGRAPHY Continuously monitor developments Create a migration strategy Assess and prioritize Stay updated on quantum computing advancements Modify cryptographic systems accordingly Adapt to evolving technologies and threats Develop a detailed plan with timelines Evaluate current cryptographic systems Identify critical data and infrastructure Prioritize high-risk components for migration Allocate necessary resources Employ phased approach for implementation 5 2 3 4 1 Research and choose appropriate algorithms Investigate quantum-resistant algorithms Test and validate Conduct exhaustive testing Evaluate efficacy, efficiency. and compatibility Select algorithms endorsed by reputable organizations like NIST Identify and address any limitations or weaknesses Select algorithms endorsed by reputable organizations like NIST Digging deep into the Post-Quantum Cryptography holds immense stature in maintaining data confidentiality and information security. Generating and deciphering codes that permit access to the data solely by approved entities. Fast-forwarding to the present day, there have been considerable advancements in computing technology, and quantum computers are anticipated to become a reality within the next ten years. Aim at nailing the top cybersecurity certification programs that can ramp up your credibility as a cybersecurity specialist. The world awaits you to reveal the futuristic cybersecurity trends as a seasoned cybersec player worldwide! © Copyright 2024. United States Cybersecurity Institute (USCSI ). All Rights Reserved. ® www.uscs institute .org
ENROLL IN The United States Cybersecurity Institute ® (USCSI )is a world-renowned cybersecurity certification body offering the best-in-the-world certifications for students and professionals around the globe across industries. Whether a beginner looking to step on cybersecurity career path or a seasoned expert, it validates their cybersecurity expertise to ace this domain. CERTIFICATION NOW © Copyright 2024. United States Cybersecurity Institute (USCSI ). All Rights Reserved. ®