Security Policies
This document outlines essential security policies focusing on access control mechanisms such as Role-Based Access Control (RBAC), Usage Control (UCON), and Risk-Based Data Sharing. It explores the nuances of "Need to Know" vs. "Need to Share," emphasizing the importance of trust management and credentialing. The paper discusses dissemination policies, obligations in access permissions, and the complex interplay of roles in coalition environments. Additionally, it addresses the integration of risk modeling with access control frameworks, ensuring safe and efficient data sharing in various organizational contexts.

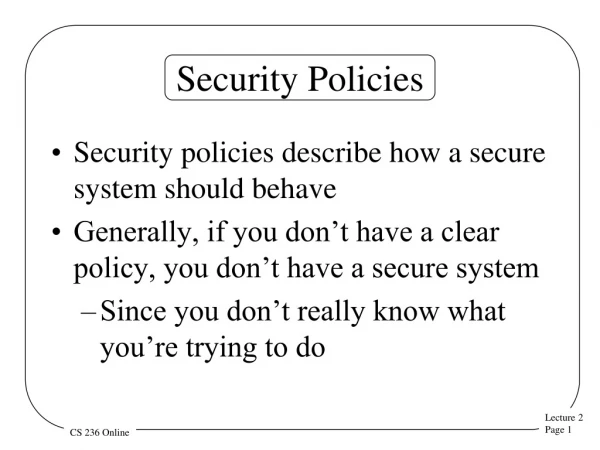
Security Policies
E N D
Presentation Transcript
Security Policies Dr. Bhavani Thuraisingham The University of Texas at Dallas Policies January 27, 2012
Outline of the Unit • Need to Know to Need to Share • RBAC • UCON • RBUC • Dissemination • Rick based access control • Trust Management/Credential/Disclosure • Directions • Major conferences for Policy and Access Control: • IEEE Policy Workshop • ACM SACMAT
Need to Know to Need to Share • Need to know policies during the cold war; even if the user has access, does the user have a need to know? • Pose 9/11 the emphasis is on need to share • User may not have access, but needs the data • Do we give the data to the user and then analyze the consequences • Do we analyze the consequences and then determine the actions to take • Do we simply not give the data to the user • What are risks involved?
RBAC • Access to information sources including structured and unstructured data both within the organization and external to the organization • Access based on roles • Hierarchy of roles: handling conflicts • Controlled dissemination and sharing of the data
UCON • RBAC model is incorporated into UCON and useful for various applications • Authorization component • Obligations • Obligations are actions required to be performed before an access is permitted • Obligations can be used to determine whether an expensive knowledge search is required • Attribute Mutability • Used to control the scope of the knowledge search • Condition • Can be used for resource usage policies to be relaxed or tightened
Role-based Usage Control (RBUC) RBAC with UCON extension
RBUC in Coalition Environment • The coalition partners maybe trustworthy), semi-trustworthy) or untrustworthy), so we can assign different roles on the users (professor) from different infospheres, e.g. • professor role, • trustworthy professor role, • semi-trustworthy professor role, • untrustworthy professor role. • We can enforce usage control on data by set up object attributes to different roles during permission-role-assignment, • e.g. professor role: 4 times a day, trustworthy role: 3 times a day semi-trustworthy professor role: 2 times a day, untrustworthy professor role: 1 time a day
Dissemination Policies • Release policies will determine to whom to release the data • What is the connection to access control • Is access control sufficient • Once the data is retrieved from the information source (e.g., database) should it be released to the user • Once the data is released, dissemination policies will determine who the data can be given to • Electronic music, etc.
Risk Based Data Sharing/Access Control • What are the risks involved in releasing/disseminating the data • Risk modeling should be integrated with the access control model • Simple method: assign risk values • Higher the risk, lower the sharing • What is the cost of releasing the data? • Cost/Risk/Security closely related
Trust Management • Trust Services • Identify services, authorization services, reputation services • Trust negotiation (TN) • Digital credentials, Disclosure policies • TN Requirements • Language requirements • Semantics, constraints, policies • System requirements • Credential ownership, validity, alternative negotiation strategies, privacy • Example TN systems • KeyNote and Trust-X (U of Milan), TrustBuilder (UIUC)
The problem: establishing trust in open systems • Mutual authentication - Assumption on the counterpart honesty no longer holds - Both participants need to authenticate each other • Interactions between strangers - In conventional systems user identity is known in advance and can be used for performing access control - In open systems partecipants may have no pre-existing relationship and may not share a common security domain ?
Trust Negotiationmodel • A promising approach for open systems where most of the interactions occur between strangers • The goal: establish trust between parties in order to exchange sensitive information and services • The approach: establish trust by verifying properties of the other party
Trust negotiation: the approach Interactions between strangers in open systems are different from traditional access control models Policies and mechanisms developed in conventional systems need to be revised ACCESS CONTROL POLICIES VS. DISCLOSURE POLICIES USER ID’s VS. SUBJECT PROPERTIES
CA CA CA Subject properties: digital credentials • Assertion about the credential owner issued and certified by a Certification Authority. • Each entity has an associated set of credentials, describing propertiesand attributes of the owner. CA
Use of Credentials Digital Credentials Credential Issuer • Julie • 3 kids • Married • American Alice Check Check -Julie - Married -Julie - American Company B Want to know marital status Company A Referenced from http://www.credentica.com/technology/overview.pdf Want to know citizenship
Credentials • Credentials can be expressed through the Security Assertion Mark-up Language (SAML) • SAML allows a party to express security statements about a given subject • Authentication statements • Attribute statements • Authorization decision statements
Disclosure policies Disclosure policies • Disclosure policies govern: • Access to protected resources • Access to sensitive information • Disclosure of sensitive credentials • Disclosure policies express trust requirements by means of credential combinations that must be disclosed to obtain authorization
Disclosure policies - Example • Suppose NBG Bank offers loans to students • To check the eligibility of the requester, the Bank asks the student to present the following credentials • The student card • The ID card • Social Security Card • Financial information – either a copy of the Federal Income Tax Return or a bank statement
Disclosure policies - Example p1= ({}, Student_Loan Student_Card()); p2= ({p1}), Student_Loan Social_Security_Card()); p3= ({p2}, Student_Loan Federal_Income_Tax_Return()); p4= ({p2}, Student_Loan Bank_Statement()); P5=({p3,p4}, Student_Loan DELIV); These policies result in two distinct “policy chains” that lead to disclosure [p1, p2, p3, p5] [p1, p2, p4, p5]
Trust Negotiation - definition The gradual disclosure of credentials and requests for credentials between two strangers, with the goal of establishing sufficient trust so that the parties can exchange sensitive information and/or resources
Trust-X system: Joint Research with University of Milan • A comprehensive XML based framework for trust negotiations: • Trust negotiation language (X-TNL) • System architecture • Algorithms and strategies to carry out the negotiation process
Trust-X language: X-TNL • Able to handle mutliple and heterogeneus certificate specifications: • Credentials • Declarations • Able to help the user in customizing the management of his/her own certificates • X-Profile • Data Set • Able to define a wide range of protection requirements by means of disclosure policies
X-TNL: Credential type system X-TNL simplifies the task of credential specification by using a set of templates called credential types Uniqueness is ensured by use of XML Namespaces Credential types are defined by using Document Type Definition <!DOCTYPE library_badge[ <!ELEMENT library_badge (name, address, phone_number*, email?, release_date, profession,Issuer)> <!ELEMENT name (fname, lname)> <!ELEMENT address (#PCDATA)> <!ELEMENT phone_number (#PCDATA)> <!ELEMENT email (#PCDATA)> <!ELEMENT release_date (#PCDATA)> <!ELEMENT profession (#PCDATA)> <!ELEMENT fname (#PCDATA)> <!ELEMENT lname (#PCDATA)> <!ELEMENT Issuer ANY> <!ATTLIST Issuer XML:LINK CDATA #FIXED “SIMPLE” HREF CDATA #REQUIRED TITLE CDATA #IMPLIED> <!ATTLIST library_badge CredID ID #REQUIRED> <!ATTLIST library_badge SENS CDATA #REQUIRED> ]>
Trust-X negotiation phases- basic model • Introduction • Send a request for a resource/service • Introductory policy exchanges • Policy evaluation phase • Disclosure policy exchange • Evaluation of the exchanged policies in order to determine secure solutions for both the parties. • Certificate exchange phase • Exchange of the sequence of certificates determined at step n. 2.
Trust-X Architecture Trust-X has been specifically designed for a peer-to-peer environment in that each party is equipped with the same functional modules and thus it can alternatively act as a requester or resource controller during different negotiations.
How a policy is processed Upon receiving a disclosure policy the compliance checker determines if it can be satisfied by any certificate of the local X-profile. Then, the module checks in the policy base the protection needs associated with the certificates, if any. The state of the negotiation is anyway updated by the tree manager, which records whether new policies and credentials have been involved or not. COMPLIANCE CHECKER TREE MANAGER Disclosure Policies Policy Base Policy Reply X-Profile
Directions • Policies are of much interest to many organizations and applications • Financial, Medical, Retail, Manufacturing etc • Roles and responsibilities • Flexible policies • RBAC, UCON, RBUC, Trust Negotiation, Dissemination Policies • Need to Know to Need to Share • IEEE POLICY and ACM SACMAT