Real-Time Systems: Scheduling and Locks in Resource Access Control
Explore scheduling protocols like RMS, priority inversion, and priority inheritance in real-time systems with task durations and shared resources.

Real-Time Systems: Scheduling and Locks in Resource Access Control
E N D
Presentation Transcript
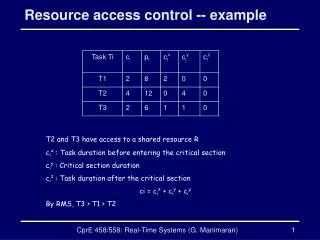
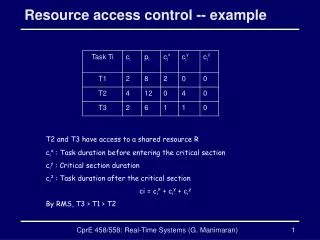
Resource access control -- example T2 and T3 have access to a shared resource R cix : Task duration before entering the critical section ciy : Critical section duration ciz : Task duration after the critical section ci = cix + ciy + ciz By RMS, T3 > T1 > T2 CprE 458/558: Real-Time Systems (G. Manimaran)
Schedules Locks R Preempted by T3 RMS Schedule Direct blocking of T3 by T2 Release R T3 T1 T2 T3 T2 T1 T2 T3 T3 T2 10 11 12 0 2 4 6 7 8 14 16 Priority inversion of T3 by T1 RMS Schedule with Priority Inheritance Protocol Direct blocking of T3 by T2 T3 T1 T2 T3 T2 T3 T1 T3 T2 0 Inheritance blocking of T1 by T2 CprE 458/558: Real-Time Systems (G. Manimaran)