Security and Lawful Intercept - Summary
10 likes | 228 Vues
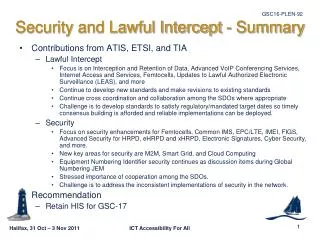
Security and Lawful Intercept - Summary. Contributions from ATIS, ETSI, and TIA Lawful Intercept Focus is on Interception and Retention of Data, Advanced VoIP Conferencing Services, Internet Access and Services, Femtocells, Updates to Lawful Authorized Electronic Surveillance (LEAS), and more

Security and Lawful Intercept - Summary
E N D
Presentation Transcript
Security and Lawful Intercept - Summary • Contributions from ATIS, ETSI, and TIA • Lawful Intercept • Focus is on Interception and Retention of Data, Advanced VoIP Conferencing Services, Internet Access and Services, Femtocells, Updates to Lawful Authorized Electronic Surveillance (LEAS), and more • Continue to develop new standards and make revisions to existing standards • Continue cross coordination and collaboration among the SDOs where appropriate • Challenge is to develop standards to satisfy regulatory/mandated target dates so timely consensus building is afforded and reliable implementations can be deployed. • Security • Focus on security enhancements for Femtocells, Common IMS, EPC/LTE, IMEI, FIGS, Advanced Security for HRPD, eHRPD and xHRPD, Electronic Signatures, Cyber Security, and more. • New key areas for security are M2M, Smart Grid, and Cloud Computing • Equipment Numbering Identifier security continues as discussion items during Global Numbering JEM • Stressed importance of cooperation among the SDOs. • Challenge is to address the inconsistent implementations of security in the network. • Recommendation • Retain HIS for GSC-17