Understanding Tor Network and Hidden Services: A Comprehensive Guide
Explore how Tor works, bridge relays, network growth, exit nodes, timing attacks, Tor Browser, hidden services, and using Tor as a SOCKS5 proxy. Learn about encryption keys, finding hidden services, and communicating securely online. Stay informed on connecting directly to Tor, bypassing restrictions, and enhancing online privacy and security.

Understanding Tor Network and Hidden Services: A Comprehensive Guide
E N D
Presentation Transcript
Tor Bruce Maggs relying on materials from http://www.torproject.org
How Tor Works (directory server)
Encryption Keys in TOR • Each relay has a long-term ``identity’’ public/private key pair used to sign TLS certificates (public keys signed by directory) • Medium-term (one week) public/private ``onion’’ keys are used to decrypt requests to extend circuits – so first node can’t spoof the whole path. These keys are deleted so that if relay is compromised, old traffic can’t be decrypted. • Short-term “connection” or “ephemeral” shared private keys are used to encrypt connections.
Bridge Relays (a.k.a. Bridges) • Some ISPs/governments block all traffic to relays that appear in the Tor directory. • Bridges are relays that don’t appear in the directory. • User has to solve the problem of finding a bridge.
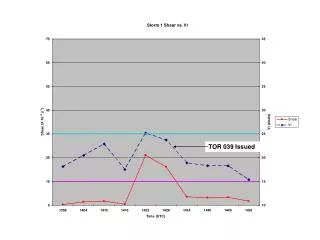
Possible Explanation for Spike • Botnet “Mevade.A” a.k.a. “Sefnit” a.k.a. “SBC” is using Tor for connectivity • http://blog.fox-it.com/2013/09/05/large-botnet-cause-of-recent-tor-network-overload/
Tor Exit Nodes See Plaintext! http://archive.wired.com/politics/security/news/2007/09/embassy_hacks?currentPage=all
Timing Attacks • Attacker controls both an entry node and an exit node (or routers nearby) • Attacker controls inter-packet delays or throughput as traffic enters an entry node • Attacker looks for same pattern at exit node
Tor-Aware Web Servers Connect directly to Tor, do not advertise their network addresses.
Using Tor as a SOCKS5 Proxy • Can tunnel any TCP connection through Tor (and DNS requests) • First run the Tor browser, it will also act as a SOCKS5 proxy and accept connections • Configure your application, e.g., chat, to use 127.0.0.1 as SOCKS5 proxy