Traffic Management - OpenFlow Switch on the NetFPGA platform
200 likes | 380 Vues
Traffic Management - OpenFlow Switch on the NetFPGA platform. Chun-Jen Chung(1203584897) Sriram Gopinath (1203800749). Outline. Open Flow Switch Applications Open Flow Switch as a Basic Firewall Per Packet Authentication Possible attacks in a VLAN-based network

Traffic Management - OpenFlow Switch on the NetFPGA platform
E N D
Presentation Transcript
Traffic Management - OpenFlow Switch on the NetFPGA platform Chun-Jen Chung(1203584897) SriramGopinath(1203800749)
Outline • Open Flow Switch • Applications • Open Flow Switch as a Basic Firewall • Per Packet Authentication • Possible attacks in a VLAN-based network • Analysis on the possible attacks • Result
OpenFlow • Open Flow is an open standard to deploy new innovative protocols in the real networking environment. • Open Flow is an open interface for remotely controlling the forwarding tables in network switches, routers, and access points. • Open Flow provides an open protocol to program the flow-table in different switches and routers. • An Open Flow Switch consists of at least three parts: (1) A Flow Table, with an action associated with each flow entry, to tell the switch how to process the flow (2) A Secure Channel that connects the switch to a remote control process (called the controller), allowing commands and packets to be sent between a controller and the switch (3) The OpenFlow Protocol, which provides an open and standard way for a controller to communicate with a switch.
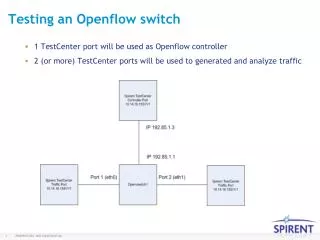
Idealized OpenFlowSwitch • The OpenFlow Switch and Controller communicate via the OpenFlow protocol, which defines messages, such as packet-received, send-packet-out, modify-forwarding-table, and get-stats.
Applications • Traffic Management • To block the malicious traffic • Per Packet Authentication • /*To prevent VLan Hopping Attack (Configuration Issue)*/
To block the malicious traffic Implementation detail: • We a packet in a new flow arrives at the open flow switch, it is sent to Controller to make appropriate decision. • Controller decides whether to block this packet or to deliver it to the destination specified in the packet • Script has been written to generate the list of Blacklisted IPs. • Then this list is used by the Open flow switch – to block any traffic from/to these blacklisted sources. • Code is implemented in the Controller to drop packets which are from the Blacklisted Ips • IP in the packet --match-- IP in the Blacklist IP address-- Drop the packet
Per Packet Authentication This application is to uniquely identify packets from the source. This involves three steps • Generate unique identification code at the source end • Transmit this code along with every packet • Evaluate the code at the destination end(Switch)
Network Set up Simulated Network Xen Configuration
Step 1: Generate unique identification code at the source end Unique identification code is generated by generating hash using the below parameters • Current Timestamp • Source Mac address • Secrete Key Hashing Technique: Hash [ Secrete Key , {TimeStamp Source Mac} ] Task Completed: HMAC SHA2-Algorithm Implemented to generate the hash value.
Step 2: Transmit the identifier in every packet • We have used the Packet generation algorithm to modify the transmitted packets to include the Hash code generated and the time stamp used in step 1. • We have used the QinQ mechanism available in the 802.1Q packet header format to include these additional values into the packet
Step 3: Evaluate the identifier at the Switch • The Hash code is again generated at the switch using the parameters in the packet. • SHA-1 algorithm used in step 1 is used to generate the Hash value • This value is compared with the hash code in the packet. • If both the values are equal then the packets is processed else it is dropped. • This code is implemented in the switch and not in the controller so as to reduce the over load from the controller. • By this implementation packets those are not legitimate can be dropped before processing.
Possible attacks in a VLAN-based network There are several different types of attack in layer 2, and most of attacks exploit the inability of a device to track the attacker. Therefore, the attacker can perform undetected malicious actions on the forwarding path to alter it and then exploit the Change. • MAC Flooding Attack This is not properly a network “attack” but more a limitation of some switches and bridges. Some of these types of devices possess a finite hardware learning table to store the source addresses of all received packets, when this table becomes full, the traffic that is directed to addresses that cannot be learned anymore will be permanently flooded. 802.1Q Tagging Attack Tagging attacks are malicious schemes that allow a user on a VLAN to get unauthorized access to another VLAN. • If a switch port was configured as DTP auto and was to receive a fake DTP packet, it might become a trunk port and it might start accepting traffic destined for any VLAN. • When simply receiving regular packets, a switch port may behave like a full-fledged trunk port.
Possible attacks in a VLAN-based network • ARP Attacks An attacker can claim that his or her MAC address is associated to any IP address within a specific subnet. This is possible because ARP requests or replies carry the information about the L2 identity (MAC address) and the L3 identity (IP address) of a device and there is no verification mechanism of the correctness of these identities. • Double-Encapsulated 802.1Q/Nested VLAN Attack When double-encapsulated 802.1Q packets are injected into the network from a device whose VLAN happens to be the native VLAN of a trunk, the VLAN identification of those packets cannot be preserved from end to end since the 802.1Q trunk would always modify the packets by stripping their outer tag. After the external tag is removed, the internal tag permanently becomes the packet’s only VLAN identifier. Therefore, by double-encapsulating packets with two different tags, traffic can be made to hop across VLANs.
Analysis of Attacks • All these attacks were analyzed in our current network • It was identified that proper configuration would prevent the environment from most of these attacks • Using ARP Inspection the occurrence of few of these attack can be prevented. • Why Per Packet Authentication?
Attack Scenario Normal Scenario When Compromised
Analysis • In the Virtual environment Dom0, which acts as the base platform should be protected. Only by compromising this instance an attacker can possibly launch an attack. • If Dom0 is protected, the possibility of an attack in virtual environment is minimal. • Per Packet Authentication enhances the security of Vlan enabled network by extending the security even when Dom0 instance is compromised. • Even if the ports are configured as Native trunk ports, this mechanism would prevent Vlan Hoping Attack • This mechanism can be extended to Physical Switch to ensure illegal traffic doesn’t pass through even if Dom0 is compromised
Result • Application 1 - basic firewall implementation has been implemented completely and Application 2 – Per packet Authentication which is yet to be completed would help in improving the security of a VLan enabled network.