Enhancing Web Security with Strider HoneyMonkeys System
90 likes | 204 Vues
Discover the Automated Web Patrol system designed to protect users from browser vulnerabilities. Learn about the Strider HoneyMonkey Exploit Detection System and its effectiveness demonstrated through experiments. Gain insights into exploit detection techniques and potential future developments in web security.

Enhancing Web Security with Strider HoneyMonkeys System
E N D
Presentation Transcript
Automated Web Patrol with Strider HoneyMonkeys:Finding Web Sites That Exploit Browser Vulnerabilities Y.-M. Wang, D. Beck, X. Jiang in Proceedings of the 13th Annual Network and Distributed Systems Security Symposium (NDSS 2006), The Internet Society, 2006. Presenter: Sangyup Lee
Summary • Introduces the concept of Automated Web Patrol • Basic aim is at protecting Internet users • Design and Implementation of the system • Effectiveness of the system is demonstrated through a series of experiments
What is the Strider HoneyMonkey Exploit Detection System? • A pipeline of VM-based honeypots that run monkey programs which patrols the web automatically in an attempt to mimic human web browsing. • Honeypot • A trap to catch malice • Records attacker’s information
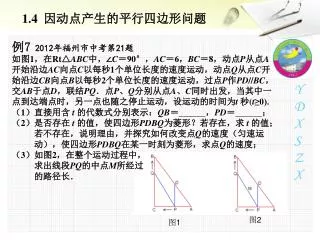
What is the Strider HoneyMonkey Exploit Detection System? (contd.) • Pipeline • Consists of 3 stages Stage 1: Exploit Site Detection on un-patched VMs Stage 2: Recursive Redirection Analysis on un-patched VMs Stage 3: Recursive Redirection Analysis with partially and fully patched VMs • Exploit detection by detecting persistent-state changes
Appreciative Comment • A good way of approaching the solution to the growing problem of browser-based attacks • Concept of prevention • Possible developments in future
Critical Comments #1 • Only one type of web browser used in the experiments – Internet Explorer 6.0 • Should have taken into account other popular browsers such as Firefox
Critical Comments #2 “…to seek out and classify web sites that exploit browser vulnerabilities.” • Ambiguous use of different Windows XP Service Pack versions on the tested machines. • Is it the OS or the browser that’s vulnerable? • Other factors that might affect the vulnerability?
Further Analysis “if I never visit those risky web sites that serve dangerous or questionable content, do I have to worry about vulnerability exploits?” “They don’t buy it because the danger is small and because security is a pain.” – B. Lampson
Discussion • Can you think of any other factors that might affect the vulnerability of your machine against browser-based attacks?