Real-Time Botnet Command and Control Characterization at the Host Level
90 likes | 224 Vues
This paper discusses a real-time method for characterizing botnet command and control (C&C) at the host level. It addresses the challenges posed by both centralized and decentralized botnets and highlights the importance of detecting malicious traffic. The authors present an architecture that leverages common protocols such as IRC and HTTP to identify botnet activity. The effectiveness of the proposed real-time filtering method is evaluated, showcasing its advantages such as immediate bot detection, though it has limitations with decentralized systems.

Real-Time Botnet Command and Control Characterization at the Host Level
E N D
Presentation Transcript
Real-Time Botnet Command and Control Characterization at the Host Level 2013.10.24 JHEN-HUANG Gao
Basic Information 1/7 • Title: • Real-Time Botnet Command and Control Characterization at the Host Level • Author & Institution: • FarhoodFaridEtemad • PayamVahdani • Publication: • 6'th International Symposium on Telecommunications • Year: 2012 • Cited (Google): 0
Outline 2/7 Introduction Architecture Detect bot Real – Time Filtering Conclusion
Introduction 3/7 Botnet 、 other kind of malwares C&C is centralized or decentralized Botnet can cause many problem Normal solution
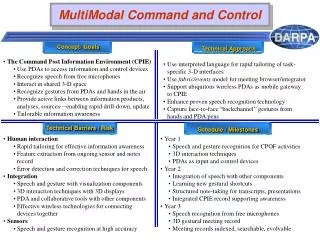
Architecture 4/7 • IRC protocol string • NICK、PASS、USER、JOIN 、 PRVIMSG、OPER、MOTD • ex Get me the file “website.html” Client Sever “Here is the file” followed by the file’s content • HTTPprotocol • GET、POST、HEAD
Detect bot 5/7 • IRCPART • Td>Tdh:normal IRC • Td<Tdh :malicious IRC • HTTP PART
Real – Time Filtering 6/7 Filtering malicious traffic after detection
Conclusion 7/7 • Real-time‘s method : • Advantage • Find bot immediately • Simple to use • Weakness • Can’t be use on decentralized