P 2 KC
P 2 KC. Kazukuni Kobara 1 and Hideki Imai 1,2 1: Research Center for Information Security (RCIS) National Institute of Advanced Industrial Science (AIST) 2: Chuo Univ. P 2 KC ?. Our proposal Personalized-Public-Key Cryptosystem Cryptosystem using personalized-public-keys. Bob ’ s

P 2 KC
E N D
Presentation Transcript
P2KC Kazukuni Kobara1 and Hideki Imai1,2 1: Research Center for Information Security (RCIS) National Institute of Advanced Industrial Science (AIST) 2: Chuo Univ.
P2KC ? • Our proposal • Personalized-Public-Key Cryptosystem • Cryptosystem using personalized-public-keys
Bob’s public-key Bob’s public-key Bob’s public-key Typical Usage of Public-Key Cryptosystem Encrypters Bob (Decrypter)
We propose three usage modes for P2KC • Distribution then Personalization (DP) mode • Personalization then Distribution with Hidden PK (PDH) mode • Personalization then Distribution with Open PK (PDO) mode
Distribution then Personalization (DP) Mode Personalized to Carol Personalized to Dave Personalized to Alice Encrypters Bob’s public-key Personalization Bob (Decrypter) Delivery
Personalization then Distribution with Hidden/Open PK (PDH/PDO) Modes Encrypters Personalized to Dave Personalized to Carol Personalized to Alice Bob’s public-key Personalization Bob (Decrypter) Delivery
Is there any advantage for personalizing PK • Maybe, no for typical (number theoretic) PKCs such as • RSA, ElGamal, ECC, DH, ECDH • But definitely yes for a certain class of combinatorial PKCs • Niederreiter/McEliece PKCs • some of the Hidden Field Equations (HFE) based PKCs and the Lattice based PKCs • as long as ciphertexts are given by the combination of public-key components according to the plaintexts and both the public-key and plaintext sizes are large
Advantages of P2KC • It can reduce the encryption-key size • Decrypter can identify the encrypter with no extra cost such as signing • suited for low computational power applications • Note: in order to prevent the replay attack it should be used in the framework of challenge-response • It can be used with other PK reduction techniques
Pros and Cons of Niederreiter (McEliece) PKC • Pros • Underlying problem (syndrome decoding) is well studied • Can be semantically secure (secure in a strong sense) • Encryption is quite simple • Mainly done with exclusive-or • Suitable for low computational power devices, such as smart cards, sensors, cellular phones, RFIDs and so on • whereas RSA, DH, ECC require multi-precision modular multiplication/exponentiation -> require coprocessors in such devices • Con • Encryption key size is huge -> P2KC gives one solution to this
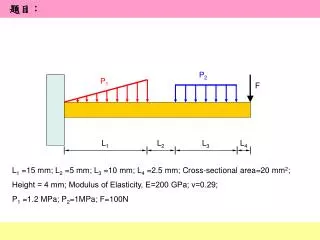
Comparison between PKC and P2KC in Niederreiter scheme PKC: (n,k,t)=(2048,1630,38), i.e. n-k=418 P2KC: (DP,RT,a=0.042), i.e. n1=86 PKC: (n,k,t)=(2048,1795,23), i.e. n-k=253 P2KC: (DP,RT,a=0.044), i.e. n1=90
Attack Cost • n: code length • k: dimension of the code • t: # of correctable errors
Core Idea of P2KC (1/2) Message Space of PKC Assumption: messages are chosen at random so that they can be used to generate session keys Second message Fourth message First message Third message
Core Idea of P2KC (2/2)P2KC limits the space and allocates it to each user Message Space of P2KC Message Space of P2KC for UserA Message Space of P2KC for UserC Message Space of P2KC for UserB Boundary is invisible for adversaries
Hard to distinguish whether the target ciphertexts belong to PKC or P2KC P2KC Indistinguishable PKC Adversary target ciphertexts • as long as the following hold: • (# of target ciphertexts)2 << (message space of P2KC) • (# of PPKs)x(Attack cost after knowing PPK) is huge PPK: Personalized-Public-Key
PKC and P2KC • PKC={KeyGen(), Enc(), Dec()} • P2KC1={KeyGen(), Pers(), PEnc(), PDec(pv,)} • Available when the decrypter knows the personalization vector pv • P2KC2={KeyGen(), Pers(), KEnc(pv,), KDec()} • Available when the encrypter knows the personalization vector pv
KeyGen(): Keys for Niederreiter PKC Random Permutation Matrix • accepts (n,k,t) • generates secret-key sk • generates public-key pk P n S H x x n-k Parity-check matrix of Goppa code which can correct up to t-error bits Random Non-singular Matrix K and t
Enc(): Encryption of Random Session-Key in Niederreiter PKC • accepts pk=(K,t) and msg • outputs cT=K msgT = Plaintext msgT n-dimentional vector of weight t or less Ciphertext cT Syndrome (0,1,0,0,1,0, ... 0,0,1,0) K x
Dec(): Decryption in Niederreiter PKC • accepts c and sk • S-1 cT=H P msgT • By applying the error-correction algorithm to S-1 cT, obtains a t or less bit error pattern (P msgT) • outputs msgT=P-1(P msgT) S-1 H P msgT = x cT P-1 x P msgT
Sketch of Personalization Message Space PPK for B pv for B msg’ PPK for C msg PPK for A pv for C pv for A PK
Pers(): PersonalizationOne Example • accepts pk=(K,t) and pv and then outputs ppk=(c2,K1,t,Sub) Sub=(3, 2, 2, 2) =K =K1 c2 pv=(2, 1, 3, 1, 4, 0, 4, 1, 2, 3) n1 pv: Personalization Vector Sub: weight of each column
Pers(): PersonalizationAnother Example • accepts pk=(K,t) and pv and then outputs ppk=(c2,K1,t,Sub) Sub=(2, 2, 2, 2) =K =K1 c2 pv=(0, 2, 3, 2, 1, 4, 1, 3, 0, 4) n1 pv: Personalization Vector Sub: weight of each column
PKC and P2KC • PKC={KeyGen(), Enc(), Dec()} • P2KC1={KeyGen(), Pers(), PEnc(), PDec(pv,)} • Available when the decrypter knows the personalization vector pv • P2KC2={KeyGen(), Pers(), KEnc(pv,), KDec()} • Available when the encrypter knows the personalization vector pv
Sketch of P2KC1where decrypter knows pv Message Space Decrypter knows msg and pv and hence can reconstruct msg’ Encrypter knows PPK msg’ msg’ PPK PPK msg pv PK PK
Sketch of P2KC2where encrypter knows pv Message Space Encrypter knows msg’ and pv and hence can reconstruct msg Decrypter can know msg msg’ PPK msg msg pv PK PK
PEnc(): Encryption in Niederreiter P2KC1 • accepts ppk and msg’ • outputs cT=c2 (+) K1 msg’T Plaintext msg’T A vector of length n1 whose weight is taken so that the total number of added columns should not exceed t = Ciphertext cT Syndrome x c2 (0,1,0) x Sub=(3, 2, 2, 2)
PDec(): Decryption in Niederreiter P2KC1 • accepts c, sk and the candidates for pv, e.g. • pv1=(2, 1, 3, 1, 4, 0, 4, 1, 2, 3) • pv2=(0, 2, 3, 2, 1, 4, 1, 3, 0, 4) • decrypts c using Dec() and sk and obtains msg, e.g. • msg=(0, 1, 1, 1, 0, 0, 0, 1, 0, 1) • looks for pv being consistent with msg • pv1 is consistent in this case • converts msg to msg' using the found pv • msg’=(0, 1, 0)
KEnc(): Encryption in Niederreiter P2KC2 • accepts ppk and pv • generates msg’ at random • cT=c2 (+) K1 msg’T • outputs both c and ms=h(msg) msgT= = Ciphertext cT Syndrome converts msg’ to msg using pv (1,1,0,1,0,0,0,1,1,0) random msg’T x c2 (1,0,0) Sub=(3, 2, 2, 2) pv=(2, 1, 3, 1, 4, 0, 4, 1, 2, 3)
KDec(): Decryption in Niederreiter P2KC2 • accepts c and sk • decrypts c using Dec() and sk and then obtains msg • outputs ms=h(msg)
It is possible define various P2KCsaccording to pv • One of our recommendations is Random Trimming (RT) [a n] coordinates where 0 < a < 1 =K =K1 Sub=(0, 1, 1, 1) pv=(0, 0, 2, 0, 0, 3, 0, 0, 4, 0)
Security of Niederreiter PKC • Theorem : Breaking OW-CPA and PDOW-CPA is NP-Complete under the assumption that c and K are indistinguishable from random ones. • Breaking OW-CPA: • Given c and pk, find msg • Breaking PDOW-CPA: • Given c and pk, find one (or some) coordinate(s) of msg • If OW-CPA or PDOW-CPA holds, it is possible to construct a PKC meeting the strongest security notion IND-CCA2
Game0: Syndrome Decoding Problem (SDP) (NP-Complete) • Given a syndrome s, a random parity-check matrix R and a small integer w, find its pre-image of hamming weight w or less Random Matrix R = x Syndrome (0,1,0,0,1,0, ... 0,0,1,0)
Game1: Indistinguishability (Assumption) K=SHP Random Matrix R c Syndrome If we assume the indistinguishability of them, it is obvious from the form of the PKC and SDP that breaking OW-CPA of the Niederreiter PKC is equivalent to solving the SDP Remark: the most powerful distinguisher so far is the SSA(Support Splitting Algorithm). Hence the underlying code must be chosen so that it can resist against the SSA.
Security of P2KC • P2KC gives constraints on the message by • fixing some coordinates • duplicating some coordinates • If these constraints are invisible for adversaries, • there is no difference between breaking PKC and breaking P2KC • We show the invisibility by proving that the following problems are as hard as SDP
Game2: Decision One Coordinate Problem (DOCP) • Given c and H, determine the i-th coordinate of msg. (0,1,0,0,1,0, ... 0,0,1,0) K = ? x i-th column c
DOCP is as hard as SDP • since if this is possible one can recover all the bits of msg by changing c and H appropriately (0,1,0,0,1,0, ... 0,0,1,0) K = ? x i-th column c
Game3a: Decision Coordinate Equivalence Problem 1 (DCEP1) • Given two ciphertexts c and c’ and H, determine whether the i-th coordinates of msg for c and c’ are the same or not. ? K K (0,1,0,1,0, ... 1,0,0) (0,1,0,1,0, ... 1,0,0) = = x x i-th column i-th column c c’
DCEP1 is as hard as SDP ? • since if this is possible one can recover all the bits of msg by creating c’ from known pre-image • This implies that it is hard to determine some coordinates in msg are fixed or not K K (0,1,0,1,0, ... 1,0,0) (0,1,0,1,0, ... 1,0,0) = = x x i-th column i-th column c c’
Game3b: Decision Coordinate Equivalence Problem 2 (DCEP2) • Given c and H, determine whether the i-th and the j-th coordinates take the same value or not. ? (0,1,0,0,1,0, ... 0,0,1,0) K = x i-th column j-th column c
DCEP2 is as hard as SDP ? (0,1,0,0,1,0, ... 0,0,1,0) K = x i-th column j-th column c • since if this is possible one can determine all the bits of msg by checking the equivalence for every j • This implies that it is hard to determine whether some coordinates are duplicated or not
Giving constraints on the message does not harm the cryptosystem basically • But the following must be satisfied: • (# of target ciphertexts)2 << message space of the P2KC • Otherwise adversaries can know the fact that message space is limited (though this does not imply the break of PKC) • (# of candidate PPKs)x(Attack cost after knowing the PPK) must be huge • Otherwise adversaries can apply exhaustive search on the personalization mechanism
One may define various P2KCsaccording to pv • One of our recommendations is Random Trimming (RT) [a n] coordinates where 0 < a < 1 =K =K1 Sub=(0, 1, 1, 1) pv=(0, 0, 2, 0, 0, 3, 0, 4, 0, 0)
Comparison between Niederreiter PKC and P2KC PKC: (n,k,t)=(2048,1630,38), i.e. n-k=418 P2KC: (DP,RT,a=0.042), i.e. n1=86 PKC: (n,k,t)=(2048,1795,23), i.e. n-k=253 P2KC: (DP,RT,a=0.044), i.e. n1=90
Conclusion (1/2) • Proposed new concept, P2KC • P2KC1 : when decrypter knows pv • P2KC2 : when encrypter knows pv • Note: they do not need to share pv
Conclusion (2/2) • P2KC can reduce the encryption-key size of a certain class of combinatorial PKCs where • ciphertexts are given by the combination of public-key components according to the plaintexts • both the public-key and plaintext sizes are large • P2KC is suitable for low computational power devices • such as smart cards, sensors, cellular phones, RFIDs and so on