Incident Analysis
Incident Analysis. Why Incident Analysis?. Bad Guys! Threats growing Vulnerabilities Increasing Internet now part of the social fabric Impact of major cyber-attack would be significant Cascading effects a major concern Reactive response must give way to Proactive preparation.


Incident Analysis
E N D
Presentation Transcript
Why Incident Analysis? • Bad Guys! • Threats growing • Vulnerabilities Increasing • Internet now part of the social fabric • Impact of major cyber-attack would be significant • Cascading effects a major concern • Reactive response must give way to Proactive preparation
Analytic Approach • The systematic and broad-scale accumulation of understanding for current and prospective behaviors on the Internet. • Technical, Political, Economic, and Social triggers • Attacks and defenses • Vulnerabilities and corrections • Victims and perpetrators • Physical-world impacts
One Effort – Looking Inside the Noise Network Activity Example Overall Activity Several Gbytes/day Noise - Below the Radar
A taxonomy of Attributes • Backscatter: Few sources, scattered evenly across enterprise network, generally contains RST or ACK flags. • Scans: Single source, usually strikes the same port on many machines, or different ports on the same machine • DoS: Multiple sources, single target, usually homogenous (but no requirement). May be oddly sized • Worms: Scanning from a steadily increasing number of hosts • Major servers: Identifiable by IP addresses.
Slammer: Precursor Detection 160000 140000 120000 100000 Flows 80000 Series1 60000 40000 20000 0 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 0 1 2 3 4 Hour 1/24:00 1/25:04
Fusion Efforts • Small Packet Probes analyzed • Patterns emerged • Identified potential threat • Analysis of CERT/CC Incident Data • Identified possible link between state and hacker groups • Hacker communications assessment • Working on profiles, country studies, event analysis
Results of Fused Analysis • What was determined? • Data collected showed definite network indicators • Methodology can be developed to provide possible warning indicators • Based on limited dataset, network indicators suggest possible malicious probes by China • Network Indicators suggest number of motivations • Exploitation • Site mapping • Intelligence gathering for further activity
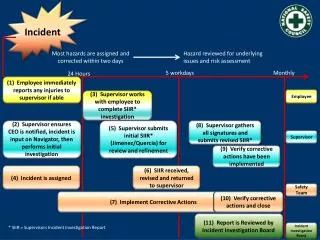
Incident data flow Pr ior i t I zed At tacks Organization 1 Repor ted Incidents Observed Event s Context Filter Organization 2 Organization 3 Prioritize Context Organization n
Why Share Incident Information? • Help in dealing with current attack • Improve future software • Better baseline for next attacks • Support non-technical solutions • Prosecution • Diplomacy • Legislation
Why not share Incident Information? • Fear of publicity • Fear of stimulating attacks • Fear of educating attackers • Forcing action ahead of decision-makers • Fear of offending suppliers/customers
How well does current response work? • For some incidents – great! • Viruses / slow worms • Narrow attacks • For others – not so great • Very fast worms • Covert compromises (Rootkits) • Broad attacks • Mass attacks
Role-based Incident Severity Tier Assignment Fusion Framework Incidents I1 I2 … In Clustering and Extrapolation System Mission Criticality Databases: DoD/MAC, Project Matrix, Key Asset Initiative Extrapolated Incidents (X-Incidents) X1 X2 … Xm Incidents Excluded Correlation and Abduction X-Incident Chains C1 C2 … Cm Other factors: Political, Social, Economic … System Admin T1 T2 T3 T4 T5 Law Enfrcmnt T1 T2 T3 T4 T5 Coord. CSIRT T1 T2 T3 T4 T5
Clustering and Extrapolation • Clustering groups reports into meaningful classes • Similarity metric applied to common features • Cohesion function calculates degree of similarity • Clustering generates overlapping clusters (clumps) • Minimizes cohesion function betweens incident sets • Extrapolation fills in the reporting gaps • Extrapolation criterion establishes when and how • Generates extrapolated incidents (x-incidents)
Correlation and Abduction • Identifies sequences that constitute staged attack • Generates x-incident chains • Starting context establishes understanding of initial system/network configuration • Causal relationships through pre-/post-condition chaining • Precondition of first incident must satisfy starting context • Postcondition of each incident must satisfy precondition of the subsequent incident • Techniques available (abduction) for filling in gaps • Strings together x-incident chains using attack patterns • Abduction criterion establishes when and how
SubSeven Trojan horse Enables Leaves worm building “Bot Network” Launches Denial-of-service attack Ongoing uses of “Bot Network” Example 1. Clustering and extrapolation based on intruder tool signature 3. Correlation based on Leaves’ scan for SubSeven signature 2. Clustering based target of attack and flooding approach 4. Abduction using distributed denial of service pattern
Challenges to Analysis Research • Gathering sufficient datasets to make statistically valid judgments • Developing automated technical analysis tools • Developing a reliable methodology for cyber-analysis • Overcoming organizational bias against sharing information
Limits of Analysis • Inherently partial data • Baseline in dynamic environment • Correlation vs. Causation • Implications • Need to be cautious in kinds of conclusions • Consider strategies for dealing with analysis gone wrong