Enhancing Communication Privacy: Point-to-Point and Network Security with UCLA OCDMA**
In an era where privacy is paramount, ensuring secure communication between Alice and Bob while thwarting eavesdropper Eve is essential. This can be achieved through encryption standards like AES, safeguarding point-to-point privacy. Additionally, protecting the network itself from Eve's traffic analysis by obscuring communication patterns is crucial. UCLA's OCDMA technology enhances privacy by concealing the source of messages based on wavelength or timeslot, providing a robust cryptographic barrier. Together, these strategies fortify both point-to-point and network privacy.

Enhancing Communication Privacy: Point-to-Point and Network Security with UCLA OCDMA**
E N D
Presentation Transcript
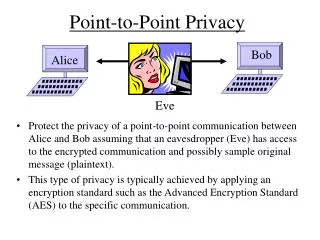
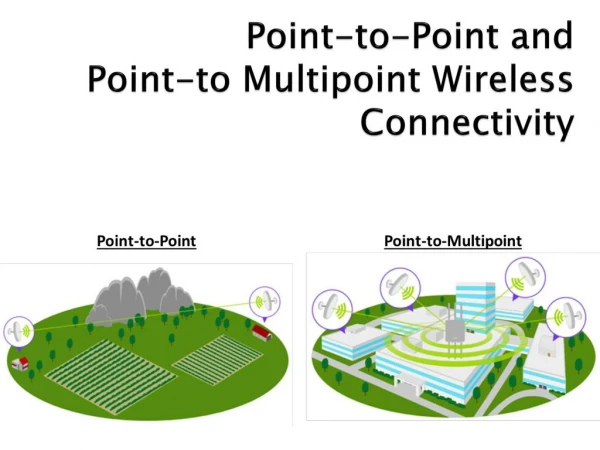
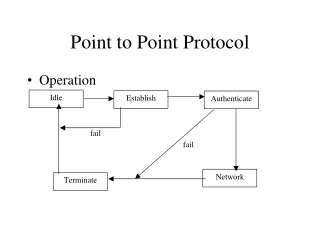
Point-to-Point Privacy Bob Alice Eve • Protect the privacy of a point-to-point communication between Alice and Bob assuming that an eavesdropper (Eve) has access to the encrypted communication and possibly sample original message (plaintext). • This type of privacy is typically achieved by applying an encryption standard such as the Advanced Encryption Standard (AES) to the specific communication.
Network Privacy Eve • Protect the privacy a network from an eavesdropper (Eve) who can see the signals transmitted on the network. Prevent Eve from • Figuring out who is talking to whom. • Isolating a particular communication to begin a cryptographic attack on a particular conversation • Performing traffic analysis (who is talking to whom on a regular basis, etc)
Security Benefit of UCLA OCDMA • UCLA OCDMA can provide point-to-point privacy as an added feature, but this can also be accomplished by well-known traditional techniques. • UCLA OCDMA provides network privacy by preventing an eavesdropper from knowing the source of a message from its wavelength or timeslot. • Network privacy enhances point-to-point privacy by providing a cryptographic obstacle to the isolation of a conversation that must be overcome before the eavesdropper can mount a cryptographic attack on the point-to-point communication.