1 / 0
The Hierarchy of Knowledge
0 likes | 156 Vues
Wisdom. Intelligence. Knowledge. Information. Data. The Hierarchy of Knowledge. Wisdom. Intelligence. Knowledge. Information. Data. The Hierarchy of Knowledge. Knowledge : assimilated information, where people understand the relationships between pieces of information
Télécharger la présentation 

The Hierarchy of Knowledge
An Image/Link below is provided (as is) to download presentation
Download Policy: Content on the Website is provided to you AS IS for your information and personal use and may not be sold / licensed / shared on other websites without getting consent from its author.
Content is provided to you AS IS for your information and personal use only.
Download presentation by click this link.
While downloading, if for some reason you are not able to download a presentation, the publisher may have deleted the file from their server.
During download, if you can't get a presentation, the file might be deleted by the publisher.
E N D
Presentation Transcript
- Wisdom Intelligence Knowledge Information Data The Hierarchy of Knowledge
- Wisdom Intelligence Knowledge Information Data The Hierarchy of Knowledge Knowledge: assimilated information, where people understand the relationships between pieces of information Information: data that is organized and has value, where data has been processed into a meaningful form Data: raw facts (assumed to be true), unformatted
- Wisdom Intelligence Knowledge Information Data The Hierarchy of Knowledge Wisdom: Vision and depth of understanding acquired through extensive knowledge and experience Intelligence: knowledge that is skillfully applied to solve problems; in people, intelligence is synonymous with experience; in computers, intelligence is artificial, imitating experience in people
- Knowledge as a Business Resource Knowledge Worker A well-educated professional who creates, modifies, or synthesizes knowledge in one’s profession Knowledge Society Also called digital society, new economy Working with brains instead of hands The importance of education Digital divide
- Systems Defined Combinations of components or elements that are formed or interact to accomplish a goal or purpose Contain inputs that are processed into outputs Have a boundary Receive input from both inside and outside the boundary Adjust through feedback
- Diagram of a System System Boundary Monitoring and Feedback Input Output Processing Internal Environment External Environment
- Elements: Lungs, heart, arteries, blood, airways, etc. Interaction: Air from external environment introduced into internal system Purpose: Provide oxygen to the human body, discharge carbon dioxide Systems: Respiratory
- Federal Income Tax System Elements: US Congress, Office of Internal Revenue, US Courts and Law Enforcement, Employers and employees Interaction: Income earned by individuals and reported by employers is processed by IRS, enforced by US Government Purpose: Collect income tax from individuals who work in the US to provide funds for the US Government
- Combinations of components or elements that are formed or interact to accomplish an information-relatedgoal or purpose A special type of system: an information system Information Systems Defined Systems Information Systems
- Diagram of an Information System System Boundary Monitoring and Feedback Information, Knowledge, Intelligence, or Wisdom Processing / Transformation Output Input Data, Information, Knowledge, or Intelligence Internal Environment External Environment
- The Hierarchy of Data(Perspective: database design) Database A collection of integrated and related files DB table (or file) A collection of related records Record A collection of related fields Field A group of characters Character Basic building block of information, represented by a byte
- Example of Relationships Among Rows
- The Hierarchy of Data, with Examples DB tables
- The Traditional Approach Separate files are created and stored for each application program.
- The Database Approach A pool of related data is shared by multiple application programs. Rather than having separate data files, each application uses a collection of data that is either joined or related in the database.
- The Database Approach Foundational Concepts Database – Highly organized information (Tables, Indexes) DBMS – Database Management Systems (Database, Interface, Tools) Use a DBMS software to create, store, organize, and retrieve data from a single database or several databases Example: Microsoft Access
- Levels of a Database Management System (DBMS) Level Term Term Definitions Highest A collection of related files or entities containing information to support a given system or a particular topic area Database A collection of records or instances for a given entity. These are also called tables depending on the DBMS File A group of fields or attributes to describe a single instance of an entity. These are also called rows depending on the DBMS Record Individual characteristics about an entity. Fields are also called attributes or columns depending on the type of DBMS Field Lowest
- Strategy: Competitive Advantage
- Value Chain Analysis
- IS Roles in the Value Chain: Business Process Re-engineering
- Value Chain Analysis: The larger Picture Supply Chain Management Enterprise Resource Planning Customer Relationship Management
- Porter’s Five Forces Figure 3-2
- Example of Five Forces Figure 3-3
- New Technologies Hype Curve
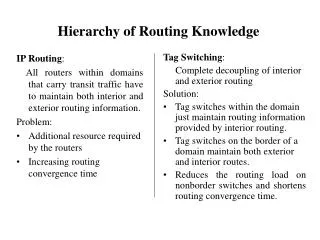
- How the Internet Works – Packet Switching Packet Switching Allows millions of users to send large and small chunksof data across the Internet concurrently Based on the concept of turn taking, packets from each user are alternated in the shared network (below) Networks connected to the Internet use this concept
- LANs with no Internet, no Browser Ethernet (IEEE 802.3) Ethernet (IEEE 802.3) Ethernet (IEEE 802.3) Ethernet (IEEE 802.3)
- Intranet Architecture
- LANs with Intranet, Browser TCP/IP Intranet Ethernet (IEEE 802.3) LAN Ethernet (IEEE 802.3) LAN TCP/IP Intranet TCP/IP Intranet Ethernet (IEEE 802.3) LAN Ethernet (IEEE 802.3) LAN TCP/IP Intranet
- LANs with Internet Connectivity TCP/IP Intranet Ethernet (IEEE 802.3) LAN Ethernet (IEEE 802.3) LAN TCP/IP Intranet Internet (TCP/IP) TCP/IP Intranet Ethernet (IEEE 802.3) LAN Ethernet (IEEE 802.3) LAN TCP/IP Intranet
- World Wide Web - Architecture
- Extranet System Architecture Virtual Private Network (VPN) is a secure network technique to protect extranet communications Uses a technique called tunneling to encapsulate, encrypt, and transmit data over the Internet Requires server authentication (verify user with password) to allow operation
- How the Internet Works – Shows the Internet Backbone
- Levels of the Organization and Traditional Systems Executive Information Systems Unstructured Decisions Decision Support Systems (both levels) Management Information Systems Semi-structured Decisions Transaction Processing Systems Structured Decisions Structured Decisions Functional Area Information Systems (Across all levels within a function) Expert Systems
- Systems That Span Organizational Boundaries
- Systems Development Processes Methodologies: Systems development life cycle (SDLC) Rapid application development (RAD) Object-oriented systems development (OOD) Extreme programming (XP) No single process works in all situations Different requirements Some systems wholly automated, others not Use augmentation system to fill gaps
- SDLC Classical process with five phases: Systems definition Management’s statement defines new system Requirements analysis Identify features and functions Component design Based on approved user requirements Implementation Implement, test, and install new system System maintenance Repair, add new features, maintain
- Phases in SDLC Figure 10-2
- System Implementation – System Conversion part
- System Maintenance - Maintenance Types
- Problems With SDLC SDLC waterfall Phases are not supposed to be repeated Often teams have need to repeat requirements and/or design phases Difficulty in documenting requirements Analysis paralysis or uncertain requirements Scheduling and budget difficulties Multiyear projects difficult to properly schedule Estimations on labor often produce insufficient budgets
- Computer Ethics Concerns
- Computer Crime Definition: The act of using a computer to commit an illegal act Authorized and unauthorized computer access Examples Stealing time on company computers Breaking into government Web sites Stealing credit card information
- Executive Roles in IT CEO Chief Executive Officer COO Chief Operations Officer CFO Chief Financial Officer CIO Chief Information Officer Manages IT Organization and Operations Forecasts IT Needs from Business Strategy Sets Direction for IT Architecture and Organization Plans, Designs and Delivers IT throughout the firm
More Related