Key Establishment
This text discusses key establishment methods in cryptography, focusing on symmetric key agreement through trusted Key Distribution Centers (KDC) and public key verification using Certification Authorities (CA). It details the Diffie-Hellman key exchange process as an example, illustrating how two parties can securely compute a shared secret key without prior shared information. The KDC's role is emphasized, explaining how it facilitates key-sharing between users while addressing potential vulnerabilities inherent in both KDC and Diffie-Hellman methods.

Key Establishment
E N D
Presentation Transcript
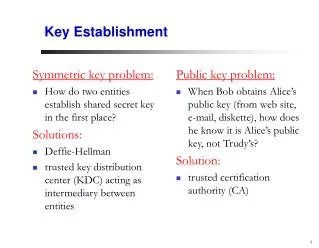
Symmetric key problem: How do two entities establish shared secret key in the first place? Solutions: Deffie-Hellman trusted key distribution center (KDC) acting as intermediary between entities Public key problem: When Bob obtains Alice’s public key (from web site, e-mail, diskette), how does he know it is Alice’s public key, not Trudy’s? Solution: trusted certification authority (CA) Key Establishment
Deffie-Hellman Key Exchange prime number p, base g secret integer a secret integer b ga mod p gb mod p (ga mod p)b mod p (gb mod p)a mod p Key: (gb mod p)a mod p= (ga mod p)b mod p
Deffie-Hellman Key Exchange: Example • Prime number p=23, base g=5. • Alice: a=6 • Send Bob: g^a mod 23 = 8. • Bob: b=15 • Send Alice: g^b mod 23 = 19. • Alice compute: 19^6 mod 23 = 2 • Bob computer: 8^15 mod 23 = 2
KB-KDC KX-KDC KY-KDC KZ-KDC KP-KDC KB-KDC KA-KDC KA-KDC KP-KDC Key Distribution Center (KDC) • KDC: server shares different secret key with each registered user (many users) • Alice shares a key with KDC: KA-KDC • Bob shares a key with KDC: KB-KDC KDC
Key Distribution Center (KDC) Q: How does KDC allow Bob, Alice to determine shared symmetric secret key to communicate with each other? KDC generates R1 KA-KDC(A,B) KA-KDC(R1, KB-KDC(A,R1) ) Alice knows R1 Bob knows to use R1 to communicate with Alice KB-KDC(A,R1) Alice and Bob communicate: using R1 as session key for shared symmetric encryption
Deffie-Hellman v.s. KDC • Deffie-Hellman • +: no infrastructure support • -: computation load on users • KDC • -: need infrastructure support • -: single bottleneck, single point of failure • +: computation load centered at KDC
+ + digital signature (encrypt) K K B B K CA Certification Authorities • Certification authority (CA): binds public key to particular entity, E. • E registers its public key with CA. • E provides “proof of identity” to CA. • CA creates certificate binding E to its public key. • certificate containing E’s public key digitally signed by CA – CA says “this is E’s public key” Bob’s public key certificate for Bob’s public key, signed by CA - Bob’s identifying information CA private key
+ + digital signature (decrypt) K K B B K CA Certification Authorities • When Alice wants Bob’s public key: • gets Bob’s certificate (Bob or elsewhere). • apply CA’s public key to Bob’s certificate, get Bob’s public key Bob’s public key CA public key +
A Certificate Contains: • Serial number (unique to issuer) • info about certificate owner, including algorithm and key value itself (not shown) • info about certificate issuer • valid dates • digital signature by issuer