Chapter 7 Worms
Chapter 7 Worms. Worms. We’ve previously discussed worms Here, consider 2 in slightly more depth Xerox PARC (1982) Morris Worm (1988) Recall also discussion of Slammer…. History. “Worm” mentioned in fiction in 1975 The Shockwave Rider by John Brunner Next slide…. History.

Chapter 7 Worms
E N D
Presentation Transcript
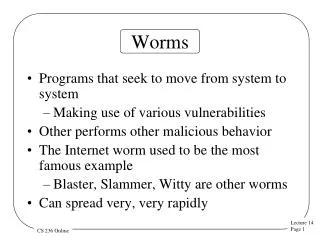
Worms • We’ve previously discussed worms • Here, consider 2 in slightly more depth • Xerox PARC (1982) • Morris Worm (1988) • Recall also discussion of Slammer…
History • “Worm” mentioned in fiction in 1975 • The Shockwave Rider by John Brunner • Next slide…
History I guess you all know about tapeworms... ? Good. Well, what I turned loose in the net yesterday was the.., father and mother of all tapeworms....My newest----my masterpiece---breeds by itself.... By now I don't know exactly what there is in the worm. More bits are being added automatically as it works its way to places I never dared guess existed....And---no, it can't be killed. It's indefinitely self-perpetuating so long as the net exists. Even if one segment of it is inactivated, a counterpart of the missing portion will remain in store at some other station and the worm will automatically subdivide and send a duplicate head to collect the spare groups and restore them to their proper place.
History • Xerox Palo Alto Research Center • Xerox PARC • Established 1970 • To create “the office of the future” • Helped create laser printers, Ethernet, modern PC, GUI, VLSI • Original Apple Macintosh heavily influenced by the “Alto”
Xerox PARC • Developed a program so unused CPU cycles could be put to use • Use your machine for parallel processing when not busy with your work • “Worm” to manage the machines • Composed of “segments” which is why they called it a worm • One segment per machine • Segments communicated with each other
Xerox PARC • “Worm” had many safety features • For example, no disk access • Also, could be shut down • Key insights • Managing growth is difficult • Stability is difficult maintain
Morris Worm • “Internet Worm” of 1988 • Major wake up call… • Three stages • Stage 1: Get access • Sendmail --- debug command • Finger --- read input using “gets” (no bounds checking…) • rexec and pwd guessing (or rsh)
Morris Worm • Stage 2: Grappling hook • Once a remote shell was obtained, send, compile, and run small C program • Code sent as source, so immune to damage by communication channel • Only passed seven bits out of eight • Would have destroyed exe file • Retrieve several exes until it found one that worked
Morris Worm • Stage 3: Propagate • Used some stealth --- named itself “sh” • Cleaned up (removed source code, etc.) • Prevented “core dump” • Propagate by looking at network routing tables and other local resources • Had no destructive payload
Propagation • Humans slow compared to networks • “Fast burners” • Warhol worms • Flash worms • Surreptitious (or slow) worms --- later • How can worm propagate faster? • Can’t use too much bandwidth…
Propagation • How to propagate faster • Shorten initial startup time • Minimize contention between instances of the worm • Increase rate that targets are probed • Use low-overhead protocols (UDP vs TCP) • Recall that Slammer used UDP
Propagation • Surreptitious worm • That is, slow worm • Slow infection rate • Hide in normal traffic • Hard to detect • Create a zombie army • What good is that? • A lot like modern Botnets
Initial Seeding • How to start the worm • A single instance? • Slow initial growth • Easier to trace • Multiple instances? • Faster initial growth • Use wireless networks, spam, Botnets • Other?
Finding Targets • IP numbers • IPv4, that is • Worms “scan” for targets • Search for vulnerable IP addresses • How to scan?
Finding Targets • How to scan? • Random • Used in Code Red and Slammer • Localized • Favor machines on same network • Why? • Hit list • Avoids contention, speeds initial spread
Finding Targets • Permutation scanning • Treat IP address space as sequence • Each worm select random starting point • Each time previously-infected machine found, select new starting point • Can be used to detect (near) saturation
Finding Targets • Topological scanning • Actual network topology • Topology of a social network • “Topology” of users’ email • IM worm • Morris Worm used topological scan • Was this a good idea for Morris Worm?
Finding Targets • Passive scanning • Wait for useful info to come to you • Sniff network traffic for… • Valid IP addresses • Operating system and services • Network traffic pattern • Other scanning strategies? • Santy worm used Google
Worms: The Bottom Line • A well-designed worm… • Virus-like concealment • Exploit technical/human weaknesses • Hijacking legitimate transactions • Rapid (or slow) spreading • Worms are potent type of malware • Equally potent defensives needed • Next chapter