Comprehensive Guide to Access Control Strategies and Models for Network Security
Explore access control basics, authorization approaches, object subject audit, authentication, and more. Learn about various models like rule-based, multi-level, and mixed authorization. Discover user-based, role-based, policy-based, and content-dependent access control strategies with real-world examples. Gain insights into Windows, Unix, Oracle, ATM, and Firewall access control methods. Perfect for understanding network security concepts and implementations.

Comprehensive Guide to Access Control Strategies and Models for Network Security
E N D
Presentation Transcript
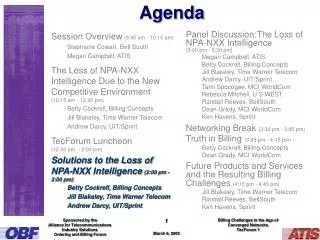
CS G513 / SS G513 Network Security Agenda Access Control Basic Model. Different Strategies and Approaches
Authorization Access Control Objects Subjects Auditing Authentication Generic Security Model for (Resource) Access Determination of safety/security of access based on policies; authentication is a pre-requisite Administrate Recording of access events for analysis – may identify security violations Identity establishment Fig. from Essmayr, Probst & Weippl
Categorization of Access Control Mechanisms • Authorization can be • Rule-based, • Rules of the form (s, t, o, c, m): subject s has access of type t to object o under condition c; m is additional information (e.g. grantor of authorization) • Multi-level, • Subjects and objects are assigned security levels and flow (of information) regulated between levels. OR • Mixed • Administration can be • Centralized, • Decentralized, or • Mixed Sundar B.
Approaches to Access Control • Discretionary Access Control • Rule-based, Decentralized (e.g. per object) • Commonly used • Mandatory Access Control • Multilevel, Centralized • Used in the military • Bell – LaPadula Model • Mixed, Decentralized • Proposed for U.S. DoD • Focused on confidentiality – • A.k.a “No read up, No write down” Sundar B.
Approaches to Access Control • User-Based Access Control (UBAC) • Rule-based • Rules per identity • Role-Based Access Control (RBAC) • A user may have many roles – • Could be more dynamic than UBAC • Roles may be defined through groups (static?) – e.g Unix • Policy-Based Access Control (PBAC) • Access Control Lists mix policy with mechanism (i.e. enforcement) – • PBAC separates policy from enforcement (mechanism) Sundar B.
Approaches to Access Control • Content Dependent Access Control (CDAC) • Rule-based • Rules are dependent on the (info.) content of the object • Useful for logical control of (access to) typed data • Context-Based Access Control (RBAC) • Access control is based on sequence of events leading to access. – used in firewalls. • View-Based Access Control (PBAC) • Useful for databases Sundar B.
Access Control Approaches • Windows • ??? • Unix • ??? • Oracle • ??? • ATM • ??? • Firewalls • ??? • Exercises Sundar B.