Secure Data Encryption Methods in IT Applications
Explore encryption algorithms, public key infrastructure (PKI), and network security protocols to facilitate end-user requirements. Learn about DES, RSA, and PKI components for secure data transfer and online transactions. Dive into the complexities of network management, global naming systems, and DNS protocols. Discover the importance of encryption for multimedia, email, and internet applications.

Secure Data Encryption Methods in IT Applications
E N D
Presentation Transcript
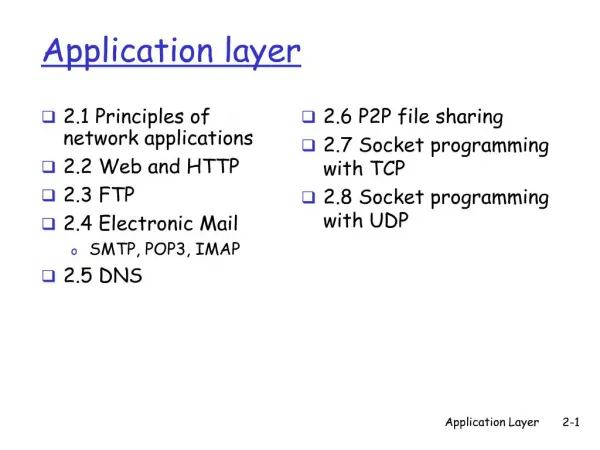
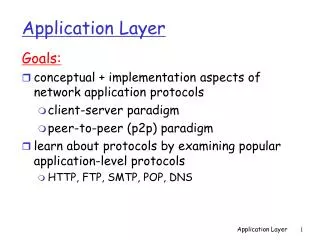
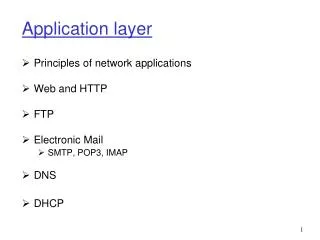
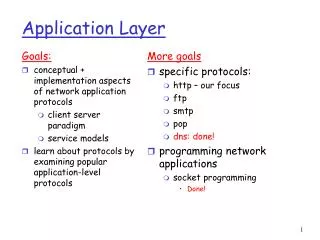
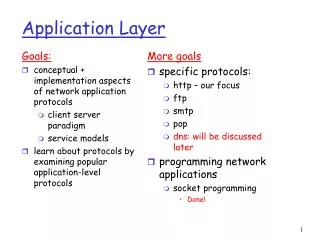
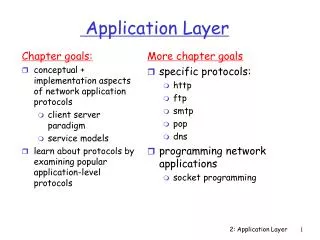
Application Layer • Overall objective • Facilitate end-user requirements • Case Study: Internet • E-mail • WWW • Multimedia • Remote Login • File transfer • Require support protocols to assist applications. Hugh Melvin, Dept. IT, NUI,G
Issues • Security • Network Complexity • Network Mgt. • Global Naming System Hugh Melvin, Dept. IT, NUI,G
Security • Increasingly important Issue • Multi-faceted • Can be built into all layers • Phy : Fibre optic • Network : Firewall • App. Layer: • Cryptography/ Encyyption • Anti-virus protection • Intrusion Detection Products (Anti-hacking) Hugh Melvin, Dept. IT, NUI,G
Cryptography ED • E:Encryption • D: Decryption • C = EK (P) …k = encr. key • P = DK (C) …k = decr. key Plaintext Ciphertext Plaintext Hugh Melvin, Dept. IT, NUI,G
Encryption Methods • Substitution vs Transposition Ciphers Substitution Cipher (SC) • Replace each plaintext entity with another • Eg. abcdef….. repl with qwerty… • Can use statistical properties of language to break • deduce that e t etc.. Hugh Melvin, Dept. IT, NUI,G
Encryption Methods Transposition Cipher (TC) • reorder plaintext entities • use of key • easy to detect a TC by stats. need to guess key length Hugh Melvin, Dept. IT, NUI,G
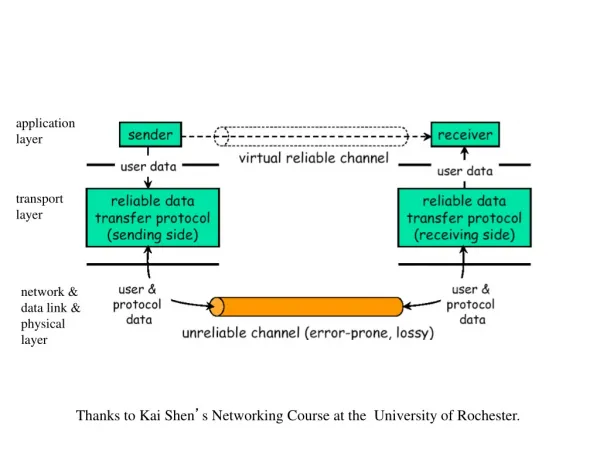
Encryption algorithms • Secret vs Public Key. Secret Key • End users share a secret key • Same key used for encr./decr. • Secure key distribution is main concern • Eg. DES (Data Encryption Standard), IDEA • Use of Product Ciphers (P-box, S-box) Hugh Melvin, Dept. IT, NUI,G
Product Ciphers P-box • Transposition stage • Eg. 11000000 00101000 (reorder) S-box • Substitution using decoder/P-box/encoder • Eg. 111 011 Can be implemented v. quickly Hugh Melvin, Dept. IT, NUI,G
DES • 64 bit blocks • 56 bit key • 16 iterations : each uses a diff section of the key • iteration : (left inputXORfn(right input and key section)) Hugh Melvin, Dept. IT, NUI,G
Successor to DES ? • DES adopted by US in 1977 • Modifications to improve performance (Triple DES) • Inadequate due to computing power • 2001: New Advanced Encryption Standard (AES) standard (Dept. Commerce NIST) • Based on Rijndael algorithm • Rijmen & Daemem • 128,192 & 256 bit keys • Faster than Triple DES • www.nist.gov/aes Hugh Melvin, Dept. IT, NUI,G
Public Key • Different keys used for encr./decr. • encr. key public • decr. key private => no key distribution security concerns • but… difficult to satisfy reqds. • Eg. RSA (Rivest, Shamir and Adleman) Hugh Melvin, Dept. IT, NUI,G
RSA • C = Pe mod n … (e,n) = public key • P = Cd mod n … (d,n) = private key • Based on factoring of large numbers • Computationally intensive => slow to impl. • Used a lot to distribute Secret Keys…Secret Key then used for data transfer. Hugh Melvin, Dept. IT, NUI,G
http:///www.rsasecurity.com Hugh Melvin, Dept. IT, NUI,G
PKI: Public Key Infrastructure • System of components to secure online transactions • Authentication • Encryption • Based on Digital Certificates & Public-key encryption • PKI System Components • Registration Authority • Certificate Authority • Directory Hugh Melvin, Dept. IT, NUI,G
PKI • Digital Certificate • Attachment to Transaction • Authenticate identity of sender • Authenticate Certificate issuer • Provide Public encryption keys Hugh Melvin, Dept. IT, NUI,G
PKI • Registration Authority • Filters certificate requests • If OK passes onto CA • Certificate Authority • Issues certificates from a directory • Directory • Database of certificates and public keys Hugh Melvin, Dept. IT, NUI,G
PKI • Different vendors • Baltimore Technologies/ RSASecurity/ VeriSign • Interoperability issues • Different Standards • X.509 (www.itu.int/itudoc/itu-t/rec/x/x500up/x509.html) • PKIX (www.ietf.org/html.charters/pkix-charter.html) • Security of Private Key critical • Potential Use of Smart Card technology Hugh Melvin, Dept. IT, NUI,G
Global naming system • Internet: ?00 million hosts • Unique IP address..need for IPv6 • Also require unique hostname for user-friendliness =>danger of name conflict/clash on global scale • Require Mgt. of naming system • DNS (Domain Name System) Hugh Melvin, Dept. IT, NUI,G
DNS • Hierarchical domain based sys. • Distributed database • Maps host names, e-mail addresses and URLs to Resource Records which includes IP address • Typically > 1 DNS Server • Windows • Control Panel => Network => Protocols => Properties => DNS • Also ipconfig /all Hugh Melvin, Dept. IT, NUI,G
Hierarchical Domain Sys. Top level: generic or country • .com = commercial • .edu = educational • .org = non-profit organisation • .ie = Ireland Hugh Melvin, Dept. IT, NUI,G
Distributed Database (Directory Info. Base DIB) • Distributed sys. of name servers • Local name servers maintain records for local domain..and redirects queries (using UDP) for remote hosts • Resource records: • IP address • Time-to-live (caching) ..etc Hugh Melvin, Dept. IT, NUI,G
Internet Applications • WWW/HTTP • FTP • Telnet • E-mail • Internet based Multimedia • Webcast • MBone • Protocols: RTP, UDP, SIP,RSVP Hugh Melvin, Dept. IT, NUI,G
WWW (World Wide Web) • Application that runs on the Internet • client-server system • Client Browser : fetches pages, interprets formatting and displays page on screen. Fetches page by establishing a TCP connection to the machine where page is located (web page server). Hugh Melvin, Dept. IT, NUI,G
WWW • Web server: Server process listens to port 80 for incoming TCP connections from clients. • HTTP : Hyper Text Transfer Protocol .. protocol that defines the format of requests and replies in the client/server model.. Hugh Melvin, Dept. IT, NUI,G
URL • Uniform Resource Locator • Each web page must be individually named (worldwide) • Each page assigned an URL • 3 parts • Where page is located…DNS of machine that contains the web page … • What page is locally called … • How to access it… HTTP protocol Hugh Melvin, Dept. IT, NUI,G
URL • Course notes on Geminga HOW WHERE WHAT http://www.it.nuigalway.ie/staff/h_melvin/hm_main.html Hugh Melvin, Dept. IT, NUI,G
Example netstat -r Active Connections Proto Local Address Foreign Address State TCP bibio:1651 geminga.nuigalway.ie:telnet ESTABLISHED TCP bibio:1693 standards.ieee.org:80 ESTABLISHED TCP bibio:1688 bodkin.nuigalway.ie:pop3 TIME_WAIT TCP bibio:1699 geminga.nuigalway.ie:80 ESTABLISHED • Two TCP Geminga connections (Telnet/WWW) • One WWW connection to IEEE (port 80) • TCP email connection to bodkin Hugh Melvin, Dept. IT, NUI,G