Application Layer
Goals: conceptual + implementation aspects of network application protocols client-server paradigm peer-to-peer (p2p) paradigm learn about protocols by examining popular application-level protocols HTTP, FTP, SMTP, POP, DNS. Application Layer.


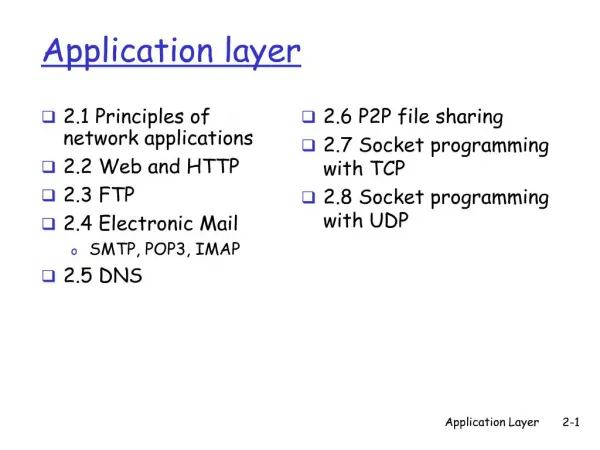
Application Layer
E N D
Presentation Transcript
Goals: conceptual + implementation aspects of network application protocols client-server paradigm peer-to-peer (p2p) paradigm learn about protocols by examining popular application-level protocols HTTP, FTP, SMTP, POP, DNS Application Layer Application Layer
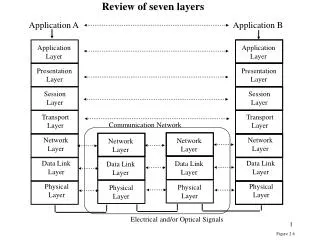
Application: communicating, distributed processes running in network hosts in “user space” exchange messages to implement app e.g., email, file transfer, p2p file share, the Web Application-layer protocols define messages exchanged by apps and actions taken uses services provided by lower layer protocols application transport network data link physical application transport network data link physical application transport network data link physical Applications and application-layer protocols Application Layer
request reply application transport network data link physical application transport network data link physical Client-server paradigm Typical network app has two pieces: client and server Client: • initiates contact with server • typically requests service from server (e.g., request WWW page, send email) Server: • provides requested service to client • e.g., sends requested WWW page, receives/stores received email Application Layer
Data Delivery some apps (e.g., audio, video) can tolerate some loss other apps (e.g., file transfer, telnet) require 100% reliable data transfer Bandwidth some apps (e.g., multimedia) require minimum amount of bandwidth to be “effective” other apps (“elastic apps”) make use of whatever bandwidth they can get Timing some apps (e.g., Internet telephony, interactive games) require low delay to be “effective” Transport service requirements of apps Application Layer
Transport service requirements of common apps Time Sensitive no no no yes, 100’s msec yes, few secs yes, 100’s msec yes and no Application file transfer e-mail Web documents real-time audio/video stored audio/video interactive games financial apps Data loss no loss no loss no loss loss-tolerant loss-tolerant loss-tolerant no loss Bandwidth elastic elastic elastic audio: 5Kb-1Mb video:10Kb-5Mb same as above few Kbps up elastic Application Layer
TCP service: connection-oriented: setup required between client, server reliable transport between sending and receiving process flow control: sender won’t overwhelm receiver congestion control: throttle sender when network overloaded does not provide: timing, minimum bandwidth guarantees UDP service: unreliable data transfer between sending and receiving process does not provide: connection setup, reliability, flow control, congestion control, timing, or bandwidth guarantee Services provided by Internet transport protocols Application Layer
Internet apps: application & transport protocols Application layer protocol SMTP [RFC 821] Telnet [RFC 854] HTTP [RFC 2068] FTP [RFC 959] proprietary (e.g. Windows Media) NFS proprietary (e.g., Vocaltec) Underlying transport protocol TCP TCP TCP TCP TCP or UDP TCP or UDP typically UDP Application e-mail remote terminal access Web file transfer streaming multimedia remote file server Internet telephony Application Layer
HTTP: HyperText Transfer Protocol WWW’s application layer protocol client/server model client: browser that requests, receives, “displays” WWW objects server: WWW server sends objects in response to requests HTTP/1.0: RFC 1945 HTTP/1.1: RFC 2068 http request PC running Explorer http response http request Server running Apache Web server http response Mac running Navigator WWW: the HTTP protocol Application Layer
TCP transport service: client initiates a TCP connection to server, port 80 server accepts TCP connection from client http messages (application-layer protocol messages) exchanged between browser and WWW server TCP connection closed http is “stateless” server maintains no information about past client requests aside Protocols that maintain “state” are complex! • past history (state) must be maintained • if server/client crashes, their views of “state” may be inconsistent, must be recovered HTTP Application Layer
Suppose user enters URL www.someUniv.ac.kr/someDepartment/index.html 1a. HTTP client initiates TCP connection to HTTP server (process) at www.someUniv.ac.kr. Port 80 is default for HTTP server. time HTTP example (contains text, references to 10 jpeg images) 1b.HTTP server at host www.someUniv.ac.kr waiting for TCP connection at port 80. “accepts” connection, notifying client 2.HTTP client sends HTTP request message (containing URL) into TCP connection socket 3.HTTP server receives request message, forms response message containing requested object (someDepartment/index.html), sends message into socket Application Layer
non-persistent connection: one object in each TCP connection some browsers create multiple TCP connections simultaneously - one per object (HTTP/1.0) persistent connection: multiple objects transferred within one TCP connection (HTTP/1.1) 5.HTTP client receives response message containing HTML file, displays HTML. Parsing HTML file, finds 10 referenced jpeg objects HTTP example (cont.) 4.HTTP server closes TCP connection. 6.Steps 1-5 repeated for each of 10 jpeg objects time Application Layer
request line (GET, POST, HEAD commands) GET /somedir/page.html HTTP/1.1 Connection: close User-agent: Mozilla/4.0 Accept: text/html, image/gif,image/jpeg Accept-language:fr (extra carriage return, line feed) header lines Carriage return, line feed indicates end of message HTTP message format: Request • two types of HTTP messages: request, response • HTTP request message: • ASCII (human-readable format) Application Layer
HTTP request message: general format Application Layer
HTTP message format: Reply status line (protocol status code status phrase) HTTP/1.1 200 OK Connection: close Date: Fri, 12 May 2000 12:30:00 GMT Server: Apache/1.3.0 (Unix) Last-Modified: Mon, 22 Jun 1998 …... Content-Length: 6821 Content-Type: text/html data goes here ... header lines data, e.g., requested html file Application Layer
In the first line of response message. Sample codes: 200 OK request succeeded, requested object later in this message 301 Moved Permanently requested object moved, new location specified later in this message (Location:) 400 Bad Request request message not understood by server 404 Not Found requested document not found on this server 304 Not Modified requested document has not been modified (Conditional GET) 505 HTTP Version Not Supported HTTP reply status codes Application Layer
Goal: don’t send object if client has up-to-date stored (cached) version client: specify date of cached copy in HTTP request If-modified-since: <date> server: response contains no object if cached copy up-to-date: HTTP/1.0 304 Not Modified client server http request msg If-modified-since: <date> object not modified http response HTTP/1.0 304 Not Modified http request msg If-modified-since: <date> object modified http response HTTP/1.1 200 OK … <data> User-server interaction: conditional GET Application Layer
Goal: control access to server documents stateless: client must present authorization in each request authorization: typically name, password authorization: header line in request if no authorization presented, server refuses access, sends WWW authenticate: header line in response server client usual http request msg 401: authorization req. WWW authenticate: usual http request msg + Authorization:line usual http request msg + Authorization:line usual http response msg usual http response msg time User-server interaction: Authentication Application Layer
Cookies is a way of remembering things for you (e.g., authentication, user preferences, previous choices) server sends “cookie” to client in response Set-cookie: # client present cookie in later requests cookie: # server matches presented-cookie with server-stored cookies server client usual http request msg usual http response + Set-cookie: # cookie- specific action usual http request msg cookie: # usual http request msg cookie: # usual http response msg usual http response msg cookie- specific action User-server interaction: Cookies Application Layer
user sets browser: WWW accesses via web cache client sends all HTTP requests to web cache if object at web cache, web cache immediately returns object in HTTP response else requests the object from origin server, saves it in the cache, then returns object in HTTP response origin server Cache server http request http request client http response http response http request http request http response http response client origin server Web Caching Goal: satisfy client request without involving origin server Application Layer
Assume: cache is “close” to client (e.g., in the same network) faster response time: cache “closer” to client decrease traffic to distant servers link out of enterprise network often bottleneck Cache server farm could be deployed to distribute load thus to increase performance origin servers public Internet T1 Internet link enterprise cache server enterprise network 100 Mbps LAN Why Web Caching? Application Layer
transfer file to/from remote host client/server model client: side that initiates transfer (either to/from remote) server: remote host FTP: RFC 959 FTP server: port 21 file transfer FTP user interface FTP client FTP server user at host remote file system local file system FTP: the file transfer protocol Application Layer
FTP client contacts FTP server at port 21, specifying TCP as transport protocol two parallel TCP connections opened: control: exchange commands, responses between client, server. “out of band control” data: file data to/from server using port 20 ftp server maintains “state”: current directory, earlier authentication TCP control connection port 21 TCP data connection port 20 FTP client FTP server FTP: separate control, data connections Application Layer
Active Mode vs. Passive Mode FTP client FTP Server client FTP Server connect connect 21 21 2834 2834 accept accept • Passive Mode FTP • when client is located inside a firewall. • Use dynamically generated port number instead of 20 • Cannot detect the FTP data transfer by the packet header only • Visit http://slacksite.com/other/ftp.html for detailed explanation passive mode request active mode 2835 passive mode 3848 connect connect 3848 20 2835 2835 data transfer data transfer 3848 20 2835 2835 disconnect disconnect 21 21 2834 2834 accept accept Passive Mode Active Mode Application Layer
Analysis of Passive FTP traffic • Use the same mechanism as the multimedia traffic analysis • Examination of FTP control packet payload • The payload data from a FTP server to a FTP client IP, TCP Header FTP Payload 227 Entering Passive Mode (141,223,82,141,128,40) • The IP address of the FTP server • = 141.223.82.141 • The port number of the FTP server for data transfer • = 128 * 256 + 40 = 32808 Application Layer
Three major components: user agents mail servers simple mail transfer protocol (SMTP) is used between mail servers User Agent a.k.a. “mail reader” composing, editing, reading mail messages e.g., Outlook, elm, mutt also uses SMTP between agent and server user agent user agent user agent user agent user agent user agent SMTP SMTP SMTP mail server mail server mail server outgoing message queue user mailbox Electronic Mail Application Layer
Mail Servers mailbox contains incoming messages (yet to be read) for users message queue of outgoing (to be sent) mail messages smtp protocol between mail servers to send email messages client: sending mail server “server”: receiving mail server user agent user agent user agent user agent user agent user agent SMTP SMTP SMTP mail server mail server mail server Electronic Mail: mail servers Application Layer
uses TCP to reliably transfer email msg from client to server, port 25 direct transfer: sending server to receiving server three phases of transfer handshaking (greeting) transfer closure command/response interaction commands: ASCII text response: status code and phrase Electronic Mail: SMTP [RFC 821] Application Layer
RFC 822: standard for text message format: header lines To: From: Subject: body the “message”, ASCII characters only line containing only `.’ Mail message format header blank line body . Application Layer
MIME: Multipurpose Internet Mail Extension, RFC 2045, 2056 MIME content type declared in msg header MIME version From: alice@crepes.fr To: bob@hamburger.edu Subject: Picture of yummy crepe. MIME-Version: 1.0 Content-Transfer-Encoding: base64 Content-Type: image/jpeg base64 encoded data ..... ......................... ......base64 encoded data . method used to encode data multimedia data type, subtype, parameter declaration encoded data Message format: multimedia extensions Application Layer
Text example subtypes: plain, html Image example subtypes: jpeg, gif Audio example subtypes: basic (8-bit mu-law encoded), 32kadpcm (32 kbps coding) Video example subtypes: mpeg, quicktime Application other data that must be processed by reader before “viewable” example subtypes: msword, octet-stream MIME types Application Layer
SMTP: delivery/storage to receiver’s server Mail Access Protocol: retrieval from server POP: Post Office Protocol [RFC 1939] authorization (agent <-->server) and download IMAP: Internet Mail Access Protocol [RFC 1730] more features (more complex) manipulation of stored msgs on server user agent user agent SMTP POP3 or IMAP sender’s mail server receiver’s mail server SMTP Mail access protocols Application Layer
authorization phase client commands: user: username pass: password server responses +OK -ERR S: +OK POP3 server ready C: user alice S: +OK C: pass hungry S: +OK user successfully logged on C: list S: 1 498 S: 2 912 S: . C: retr 1 S: <message 1 contents> S: . C: dele 1 C: retr 2 S: <message 1 contents> S: . C: dele 2 C: quit S: +OK POP3 server signing off POP3 protocol transaction phase, client: • list: list message numbers • retr: retrieve message by number • dele: delete • quit Application Layer
More functionalities than POP users can manipulate messages on server, e.g., to create hierarchy of folders folders organization accessed from all user’s machines (office, @home, mobile) users can retrieve only part(s) of a multipart message, e.g., downloading in a small portable terminal only header or text part of a multimedia message. More complex server maintains state, e.g., hierarchy of folders for each user IMAP Application Layer
Convenient for the user on the go (Internet Café, WebTV, …) User can organize their hierarchy of folders on servers May be slow: server typically far from client interaction with server through CGI scripts user agent ordinary Web browser user agent ordinary Web browser SMTP HTTP sender’s mail server receiver’s mail server HTTP Web Mail Application Layer
People: many identifiers: SSN, name, Passport # Internet hosts, routers: IP address (32 bit) - used for addressing datagrams “name”, e.g., www.postech.ac.kr - used by humans Q: map between IP addresses and name ? Domain Name System: distributed database implemented in hierarchy of many name servers application-layer protocol host, routers, name servers to communicate to resolvenames (address/name translation) note: core Internet function implemented as application-layer protocol complexity at network’s “edge” DNS: Domain Name System Application Layer
no server has all name-to-IP address mappings local name servers: each ISP, company has local (default) name server host DNS query first goes to local name server authoritative name server: for a host: stores that host’s IP address, name can perform name/address translation for that host’s name Why not centralize DNS? single point of failure traffic volume distant centralized database maintenance Just doesn’t scale! DNS name servers Application Layer
contacted by local name server that can not resolve name root name server: contacts authoritative name server if name mapping not known gets mapping returns mapping to local name server 13 root name servers worldwide DNS: Root name servers Application Layer
host surf.eurecom.fr wants IP address of gaia.cs.umass.edu 1. Contacts its local DNS server, dns.eurecom.fr 2.dns.eurecom.fr contacts root name server, if necessary 3. root name server contacts authoritative name server, dns.umass.edu, if necessary root name server 2 4 3 5 local name server dns.eurecom.fr authorititive name server dns.umass.edu 1 6 requesting host surf.eurecom.fr gaia.cs.umass.edu Simple DNS example Application Layer
Root name server: may not know authoritative name server may know intermediate name server: who to contact to find authoritative name server local name server dns.eurecom.fr intermediate name server dns.umass.edu DNS example root name server 6 2 3 7 5 4 1 8 authoritative name server dns.cs.umass.edu requesting host surf.eurecom.fr gaia.cs.umass.edu Application Layer
recursive query: puts burden of name resolution on contacted name server heavy load? iterated query: contacted server replies with name of server to contact “I don’t know this name, but ask this server” root name server iterated query 2 3 4 7 local name server dns.eurecom.fr intermediate name server dns.umass.edu 5 6 1 8 authoritative name server dns.cs.umass.edu requesting host surf.eurecom.fr gaia.cs.umass.edu DNS: iterated queries Application Layer
once (any) name server learns mapping, it caches mapping cache entries timeout (disappear) after some time DNS Related RFCs - http://www.zoneedit.com/doc/rfc/ DNS: caching and updating records Application Layer
DNS: distributed db storing resource records (RR) Type=NS name is domain (e.g. foo.com) value is IP address of authoritative name server for this domain RR format: (name, value, type,ttl) DNS records • Type=CNAME • name is an alias name for some “cannonical” (the real) name • value is cannonical name • Type=A • name is hostname • value is IP address • Type=MX • value is hostname of mailserver associated with name Application Layer
DNS protocol :queryand repy messages, both with the same message format DNS protocol, messages msg header • identification: 16 bit # for query, repy to query uses same # • flags: • query or reply • recursion desired • recursion available • reply is authoritative Application Layer
DNS protocol, messages Name, type fields for a query RRs in reponse to query records for authoritative servers additional “helpful” info that may be used Application Layer
Peer has the functionality of both client and server Client-Server Architecture P2P Architecture Peer Peer Client Client Server Peer Peer Client Peer Client Peer-to-peer (P2P) paradigm Application Layer
The information creation, distribution and consummation are ideally a decentralizedanddistributed process The relationship between consumer and producer of information normally is peer to peer Popular P2P applications Instant Messaging – MSN/Yahoo Messengers, ICQ, etc. File Sharing – WinMX, Kazaa, Morpheus, e-donkey, V-share, BitTorrent, etc. P2P apps use proprietary, Freenet, Gnutella, FastTrack, BitTorrent protocols Why peer-to-peer (P2P)? Application Layer
Web Hard Temporary Back Up Super Computing Local Search Engine Internet Infrastructure SI Hard Disk공유 Collaboration Component Video Conference CPU공유 File Sharing Contents Distribution By Product Company’s Infrastructure Providing DRM Infrastructure KMS GroupWare Application Service Model Profit Model Commerce EDMS SCM Intermediary Commerce Collaboration Contents Distribution B2B,B2C Infra제공 광고 Payment 광고 가입비/수수료 Messenger File Sharing Video Conference P2P결재 수수료 컨텐츠 유통 수수료 CP 가입비 B2B 복덕방 B2C C2C 벼룩시장 P2P광고 중고 매매 P2P Profit Model Many businesses are attempting to utilize P2P for commercial purposes Application Layer
Summary • Learned the conceptual + implementation aspects of network application protocols • client-server paradigm • peer-to-peer (p2p) paradigm • Learned about protocols by examining popular application-level protocols • HTTP, FTP, SMTP, POP, DNS Application Layer