Application Layer
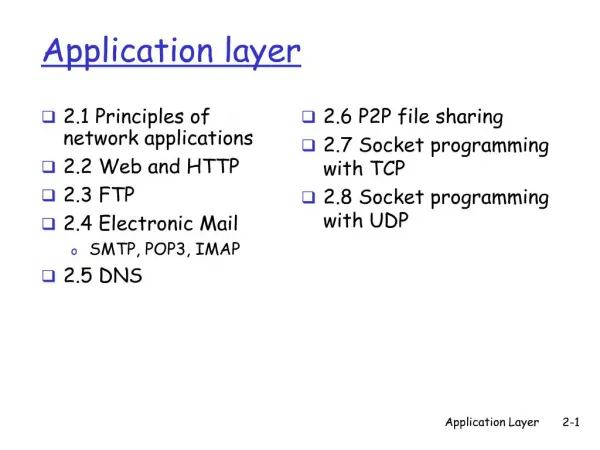
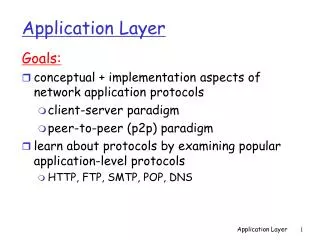
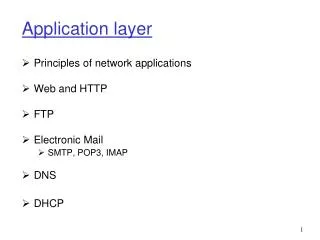
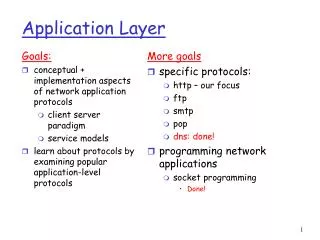
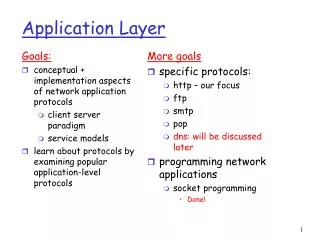
Application Layer. CE-143 CNE-0802. Application: communicating, distributed processes e.g., e-mail, Web, P2P file sharing, instant messaging running in end systems (hosts) exchange messages to implement application Application-layer protocols one “piece” of an app


Application Layer
E N D
Presentation Transcript
Application Layer CE-143 CNE-0802
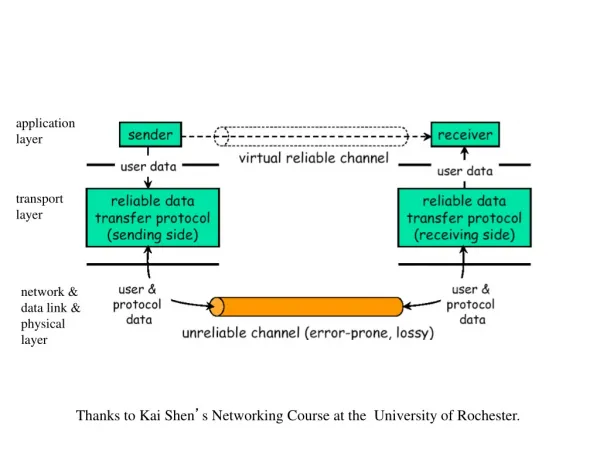
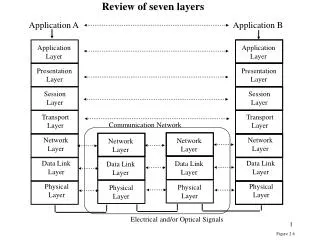
Application: communicating, distributed processes e.g., e-mail, Web, P2P file sharing, instant messaging running in end systems (hosts) exchange messages to implement application Application-layer protocols one “piece” of an app define messages exchanged by apps and actions taken use communication services provided by lower layer protocols (TCP, UDP) application transport network data link physical application transport network data link physical application transport network data link physical Applications and application-layer protocols
Types of messages exchanged, eg, request & response messages Syntax of message types: what fields in messages & how fields are delineated Semantics of the fields, ie, meaning of information in fields Rules for when and how processes send & respond to messages Public-domain protocols: defined in RFCs allows for interoperability eg, HTTP, SMTP Proprietary protocols: eg, KaZaA App-layer protocol defines
Typical network app has two pieces: client and server request reply application transport network data link physical application transport network data link physical Client-server paradigm Client: • initiates contact with server (“speaks first”) • typically requests service from server, • Web: client implemented in browser; e-mail: in mail reader Server: • provides requested service to client • e.g., Web server sends requested Web page, mail server delivers e-mail
Data loss some apps (e.g., audio) can tolerate some loss other apps (e.g., file transfer, telnet) require 100% reliable data transfer Timing some apps (e.g., Internet telephony, interactive games) require low delay to be “effective” What transport service does an app need? Bandwidth • some apps (e.g., multimedia) require minimum amount of bandwidth to be “effective” • other apps (“elastic apps”) make use of whatever bandwidth they get
DNS: Domain Name System Internet hosts: • IP address (32 bit) - used for addressing datagrams • “name”, e.g., ww.yahoo.com - used by humans DNS: provides translation between host name and IP address • distributed database implemented in hierarchy of many name servers • Distributed for scalability & reliability
DNS Services • Hostname to IP address translation • Host aliasing • Canonical and alias names • Mail server aliasing • Load distribution • Replicated Web servers: set of IP addresses for one canonical name
Host at cis.poly.edu wants IP address for gaia.cs.umass.edu Infrastructure: Client resolver Local DNS server Authoritative DNS Server Root DNS Server Top-Level Domain DNS Server local DNS server dns.poltek.ac.id DNS Infrastructure root DNS server 2 3 TLD DNS server 4 5 6 7 1 8 authoritative DNS server Ns1.google.com requesting host Ce1.poltek.ac.id www.google.com
Root DNS Servers TLD Servers ca DNS servers id DNS servers com DNS servers usask.ca DNS servers co.id DNS servers ucalgary.ca DNS servers amazon.com DNS servers ac.id DNS servers yahoo.com DNS servers Distributed, Hierarchical Database • Root servers and TLD servers typically do not contain hostname to IP mappings; they contain mappings for locating authoritative servers.
root DNS server 2 3 6 7 TLD DNS server 4 local DNS server Ns1.poltek.ac.id 5 1 8 authoritative DNS server Ns1.google.com requesting host Ce1.poltek.ac.id www.google.com Recursive queries recursive query: • puts burden of name resolution on contacted name server • heavy load? iterated query: • contacted server replies with name of server to contact • “I don’t know this name, but ask this server”
DNS: distributed db storing resource records (RR) Type=NS name is domain (e.g. foo.com) value is IP address of authoritative name server for this domain RR format: (name, value, type, ttl) DNS records • Type=A • name is hostname • value is IP address • Type=CNAME • name is alias name for some “cannonical” (the real) name www.ibm.com is really servereast.backup2.ibm.com • value is cannonical name • Type=MX • value is name of mailserver associated with name
DNS protocol :queryand reply messages, both with same message format DNS protocol, messages msg header • identification: 16 bit # for query, reply to query uses same # • flags: • query or reply • recursion desired • recursion available • reply is authoritative
DNS protocol, messages Name, type fields for a query RRs in reponse to query records for authoritative servers additional “helpful” info that may be used
DNS Server Configuration (Sample) ; zone file for example.com $TTL 2d ; 172800 secs default TTL for zone @ IN SOA ns1.example.com. hostmaster.example.com. ( 2003080800 ; se = serial number 12h ; ref = refresh 15m ; ret = update retry 3w ; ex = expiry 3h ; min = minimum ) IN NS ns1.example.com. IN MX 10 mail.example.net. joe IN A 192.168.254.3 www IN CNAME joe
Security Issue on DNS • DNS is plain text easy to capture • No security mechanism to secure request • Even easy to do Name Server Hijacking • It is vulnerable for Buffer Overflow Attack
WWW Background • 1989-1990 – Tim Berners-Lee invents the World Wide Web at CERN • Means for transferring text and graphics simultaneously • Client/Server data transfer protocol • Communication via application level protocol • System ran on top of standard networking infrastructure • Text mark up language • Not invented by Bernes-Lee • Simple and easy to use • Requires a client application to render text/graphics
WWW Components • Structural Components • Clients/browsers – to dominant implementations • Servers – run on sophisticated hardware • Caches – many interesting implementations • Internet – the global infrastructure which facilitates data transfer • Semantic Components • Hyper Text Transfer Protocol (HTTP) • Hyper Text Markup Language (HTML) • eXtensible Markup Language (XML) • Uniform Resource Identifiers (URI) • Uniform Resource Locator (URL)
Uniform Resource Identifiers • Web resources need names/identifiers – Uniform Resource Identifiers (URIs) • Resource can reside anywhere on the Internet • URIs are a somewhat abstract notion • A pointer to a resource to which request methods can be applied to generate potentially different responses • A request method is eg. fetching or changing the object • Instance: http://www.foo.com/index.html • Protocol, server, resource • Most popular form of a URI is the Uniform Resource Locator (URL) • FIND THE DIFFERENCE BETWEEN URL AND URI!!!
HTTP Basics • Protocol for client/server communication • The heart of the Web • Very simple request/response protocol • Client sends request message, server replies with response message • Stateless • Relies on URI naming mechanism • Three versions have been used • 09/1.0 – very close to Berners-Lee’s original • RFC 1945 (original RFC is now expired) • 1.1 – developed to enhance performance, caching, compression • RFC 2068 • 1.0 dominates today but 1.1 is catching up
HTTP Request Messages • GET – retrieve document specified by URL • PUT – store specified document under given URL • HEAD – retrieve info. about document specified by URL • OPTIONS – retrieve information about available options • POST – give information (eg. annotation) to the server • DELETE – remove document specified by URL • TRACE – loopback request message • CONNECT – for use by caches
HTTP Request Format • First type of HTTP message: requests • Client browsers construct and send message • Typical HTTP request: • GET http://www.cs.wisc.edu/index.html HTTP/1.0 request-line ( request request-URI HTTP-version) headers (0 or more) <blank line> body (only for POST request)
HTTP Response Format • Second type of HTTP message: response • Web servers construct and send response messages • Typical HTTP response: • HTTP/1.0 301 Moved Permanently Location: http://www.wisc.edu/cs/index.html status-line (HTTP-version response-code response-phrase) headers (0 or more) <blank line> body
HTTP Response Codes • 1xx – Informational – request received, processing • 2xx – Success – action received, understood, accepted • 3xx – Redirection – further action necessary • 4xx – Client Error – bad syntax or cannot be fulfilled • 5xx – Server Error – server failed
HTTP Headers • Both requests and responses can contain a variable number of header fields • Consists of field name, colon, space, field value • 17 possible header types divided into three categories • Request • Response • Body • Example: Date: Friday, 27-Apr-01 13:30:01 GMT • Example: Content-length: 3001
HTTP/1.0 Network Interaction • Clients make requests to port 80 on servers • Uses DNS to resolve server name • Clients make separate TCP connection for each URL • Some browsers open multiple TCP connections • Netscape default = 4, WATCH OUT ON PIPELINING • Server returns HTML page • Many types of servers with a variety of implementations • Apache is the most widely used • Freely available in source form • Client parses page • Requests embedded objects
HTTP/1.1 Performance Enhancements • HTTP/1.0 is a “stop and wait” protocol • Separate TCP connection for each file • Connect setup and tear down is incurred for each file • Inefficient use of packets • Server must maintain many connections in TIME_WAIT • ISSUE on HTTP/1.0 • Resulted in HTTP/1.1 specification focused on performance enhancements • Persistent connections • Pipelining • Enhanced caching options • Support for compression
Persistent Connections and Pipelining • Persistent connections • Use the same TCP connection(s) for transfer of multiple files • Reduces packet traffic significantly • May or may not increase performance from client perspective • Load on server increases • Pipelining • Pack as much data into a packet as possible • Requires length field(s) within header • May or may not reduce packet traffic or increase performance • Page structure is critical
HTML Basics • Hyper-Text Markup Language • A subset of Standardized General Markup Language (SGML) • Facilitates a hyper-media environment • Embedded links to other documents and applications • Documents use elements to “mark up” or identify sections of text for different purposes or display characteristics • Mark up elements are not seen by the user when page is displayed • Documents are rendered by browsers • NOTE: Not all documents in the Web are HTML! • Most people use WYSIWYG editors (MS Word) to generate HTML
HTML Example <HTML> <HEAD> <TITLE> PB’s HomePage </TITLE> </HEAD> <BODY> <CENTER><IMG SRC = “bad_picture.gif” ALT = “ “><BR></CENTER> <P><CENTER><H1>UW Computer Science Department</H1></CENTER> Welcome to my goofy HomePage! … <A HREF = http://www.cs.wisc.edu/~pb/mydogs_page.html> Spot’s Page </A> </BODY> </HTML>
Security Issue on Web • By User • Defacing • SQL or Shell Inject • DoS • By Owner • Phissing (try this: http://www.kilkbca.com) • Malware (Nice app to be downloded, contain malware) • Trojan/Virus/Worm (via sec’ hole in the Browser)
SMTP: delivery/storage to receiver’s server Mail access protocol: retrieval from server POP: Post Office Protocol [RFC 1939] authorization (agent <-->server) and download IMAP: Internet Mail Access Protocol [RFC 1730] more features (secure, database intragration, broad authentication, etc HTTP: Hotmail , Yahoo! Mail, etc. user agent user agent sender’s mail server SMTP EMail protocols SMTP POP3/ IMAP/ WebMail receiver’s mail server
Three major components: user agents mail servers simple mail transfer protocol: SMTP User Agent (mail reader) composing, editing, reading mail messages e.g., Eudora, Outlook, elm, Netscape Messenger outgoing, incoming messages stored on server user agent user agent user agent user agent user agent user agent SMTP SMTP SMTP mail server mail server mail server outgoing message queue user mailbox Electronic Mail
Mail Servers mailbox contains incoming messages for user messagequeue of outgoing (to be sent) mail messages SMTP protocol between mail servers to send email messages client: sending mail server “server”: receiving mail server user agent user agent user agent user agent user agent user agent SMTP SMTP SMTP mail server mail server mail server Electronic Mail: mail servers
uses TCP to reliably transfer email message from client to server, port 25 direct transfer: sending server to receiving server three phases of transfer handshaking (greeting) transfer of messages closure command/response interaction commands: ASCII text response: status code and phrase messages must be in 7-bit ASCII Electronic Mail: SMTP [RFC 2821]
1) Alice uses UA to compose message and “to” bob@someschool.edu 2) Alice’s UA sends message to her mail server; message placed in message queue 3) Client side of SMTP opens TCP connection with Bob’s mail server 4) SMTP client sends Alice’s message over the TCP connection 5) Bob’s mail server places the message in Bob’s mailbox 6) Bob invokes his user agent to read message user agent user agent mail server mail server Scenario: Alice sends message to Bob 1 2 6 3 4 5
Sample SMTP interaction S: 220 hamburger.edu C: HELO crepes.fr S: 250 Hello crepes.fr, pleased to meet you C: MAIL FROM: <alice@crepes.fr> S: 250 alice@crepes.fr... Sender ok C: RCPT TO: <bob@hamburger.edu> S: 250 bob@hamburger.edu ... Recipient ok C: DATA S: 354 Enter mail, end with "." on a line by itself C: Do you like ketchup? C: How about pickles? C: . S: 250 Message accepted for delivery C: QUIT S: 221 hamburger.edu closing connection
Try SMTP interaction for yourself: • telnet servername 25 • see 220 reply from server • enter HELO, MAIL FROM, RCPT TO, DATA, QUIT commands above lets you send email without using email client (reader)
SMTP uses persistent connections SMTP requires message (header & body) to be in 7-bit ASCII SMTP server uses CRLF.CRLF to determine end of message Comparison with HTTP: HTTP: pull SMTP: push both have ASCII command/response interaction, status codes HTTP: each object encapsulated in its own response msg SMTP: multiple objects sent in multipart msg SMTP: final words
SMTP: protocol for exchanging email msgs RFC 822: standard for text message format: header lines, e.g., To: From: Subject: differentfrom SMTP commands! body the “message”, ASCII characters only Mail message format header blank line body
MIME: multimedia mail extension, RFC 2045, 2056 additional lines in msg header declare MIME content type From: alice@crepes.fr To: bob@hamburger.edu Subject: Picture of yummy crepe. MIME-Version: 1.0 Content-Transfer-Encoding: base64 Content-Type: image/jpeg base64 encoded data ..... ......................... ......base64 encoded data Message format: multimedia extensions MIME version method used to encode data multimedia data type, subtype, parameter declaration encoded data
Text example subtypes: plain, html Image example subtypes: jpeg, gif Audio exampe subtypes: basic (8-bit mu-law encoded), 32kadpcm (32 kbps coding) Video example subtypes: mpeg, quicktime Application other data that must be processed by reader before “viewable” example subtypes: msword, octet-stream MIME typesContent-Type: type/subtype; parameters
Multipart Type From: alice@crepes.fr To: bob@hamburger.edu Subject: Picture of yummy crepe. MIME-Version: 1.0 Content-Type: multipart/mixed; boundary=StartOfNextPart --StartOfNextPart Dear Bob, Please find a picture of a crepe. --StartOfNextPart Content-Transfer-Encoding: base64 Content-Type: image/jpeg base64 encoded data ..... ......................... ......base64 encoded data --StartOfNextPart Do you want the reciple?
authorization phase client commands: user: declare username pass: password server responses +OK -ERR transaction phase, client: list: list message numbers retr: retrieve message by number dele: delete quit POP3 protocol S: +OK POP3 server ready C: user bob S: +OK C: pass hungry S: +OK user successfully logged on C: list S: 1 498 S: 2 912 S: . C: retr 1 S: <message 1 contents> S: . C: dele 1 C: retr 2 S: <message 1 contents> S: . C: dele 2 C: quit S: +OK POP3 server signing off
More about POP3 Previous example uses “download and delete” mode. Bob cannot re-read e-mail if he changes client “Download-and-keep”: copies of messages on different clients POP3 is stateless across sessions IMAP Keep all messages in one place: the server Allows user to organize messages in folders IMAP keeps user state across sessions: names of folders and mappings between message IDs and folder name POP3 (more) and IMAP