Flow control and Error control
Flow control and Error control. ECS 152A Xin Liu. Based on Kurose and Ross. Our goals: understand principles behind data link layer services: Flow control error detection, correction reliable data transfer. The Data Link Layer. Some terminology: hosts and routers are nodes


Flow control and Error control
E N D
Presentation Transcript
Flow control and Error control ECS 152A Xin Liu Based on Kurose and Ross
Our goals: understand principles behind data link layer services: Flow control error detection, correction reliable data transfer The Data Link Layer
Some terminology: hosts and routers are nodes communication channels that connect adjacent nodes along communication path are links wired links wireless links LANs layer-2 packet is a frame,encapsulates datagram “link” Link Layer: Introduction data-link layer has responsibility of transferring datagram from one node to adjacent node over a link
Datagram transferred by different link protocols over different links: e.g., Ethernet on first link, frame relay on intermediate links, 802.11 on last link Each link protocol provides different services e.g., may or may not provide rdt over link transportation analogy trip from Princeton to Lausanne limo: Princeton to JFK plane: JFK to Geneva train: Geneva to Lausanne tourist = datagram transport segment = communication link transportation mode = link layer protocol travel agent = routing algorithm Link layer: context
Link Layer Services • Framing, link access: • encapsulate datagram into frame, adding header, trailer • channel access if shared medium • “MAC” addresses used in frame headers to identify source, dest • different from IP address! • Reliable delivery between adjacent nodes • we learned how to do this already (chapter 3)! • seldom used on low bit error link (fiber, some twisted pair) • wireless links: high error rates • Q: why both link-level and end-end reliability?
Link Layer Services (more) • Flow Control: • pacing between adjacent sending and receiving nodes • Error Detection: • errors caused by signal attenuation, noise. • receiver detects presence of errors: • signals sender for retransmission or drops frame • Error Correction: • receiver identifies and corrects bit error(s) without resorting to retransmission • Half-duplex and full-duplex • with half duplex, nodes at both ends of link can transmit, but not at same time
link layer implemented in “adaptor” (aka NIC) Ethernet card, PCMCI card, 802.11 card sending side: encapsulates datagram in a frame adds error checking bits, rdt, flow control, etc. receiving side looks for errors, rdt, flow control, etc extracts datagram, passes to rcving node adapter is semi-autonomous link & physical layers frame frame Adaptors Communicating datagram rcving node link layer protocol sending node adapter adapter
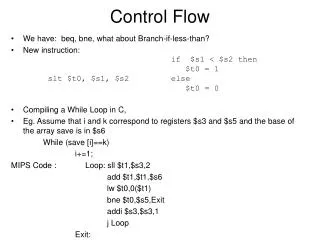
Flow Control • Ensuring the sending entity does not overwhelm the receiving entity • Preventing buffer overflow • Transmission time • Time taken to emit all bits into medium • Propagation time • Time for a bit to traverse the link
Stop and Wait • Source transmits frame • Destination receives frame and replies with acknowledgement • Source waits for ACK before sending next frame • Destination can stop flow by not send ACK • Works well for a few large frames
Fragmentation • Large block of data may be split into small frames • Limited buffer size • Errors detected sooner (when whole frame received) • On error, retransmission of smaller frames is needed • Prevents one station occupying medium for long periods • Stop and wait becomes inadequate
Sliding Windows Flow Control • Allow multiple frames to be in transit • Receiver has buffer W long • Transmitter can send up to W frames without ACK • Each frame is numbered • ACK includes number of next frame expected • Sequence number bounded by size of field (k) • Frames are numbered modulo 2k
Sliding Window Enhancements • Receiver can acknowledge frames without permitting further transmission (Receive Not Ready) • Must send a normal acknowledge to resume • If duplex, use piggybacking • If no data to send, use acknowledgement frame • If data but no acknowledgement to send, send last acknowledgement number again, or have ACK valid flag (TCP) Q: if the size of field is k, what is the maximum window size? A: 2^k -1. Assuming 0,1,…2^k-1 (2^k window size) sent out, need to ack the last 2^k-1.
Error Detection • EDC= Error Detection and Correction bits (redundancy) • D = Data protected by error checking, may include header fields • Error detection not 100% reliable! • protocol may miss some errors, but rarely • larger EDC field yields better detection and correction
Parity Checking Two Dimensional Bit Parity: Detect and correct single bit errors Single Bit Parity: Detect single bit errors 0 0
Sender: treat segment contents as sequence of 16-bit integers checksum: addition (1’s complement sum) of segment contents sender puts checksum value into UDP checksum field Receiver: compute checksum of received segment check if computed checksum equals checksum field value: NO - error detected YES - no error detected. But maybe errors nonetheless? More later …. UDP checksum Goal: detect “errors” (e.g., flipped bits) in transmitted segment
Internet Checksum Example • Note • When adding numbers, a carryout from the most significant bit needs to be added to the result • Example: add two 16-bit integers 1 1 1 1 0 0 1 1 0 0 1 1 0 0 1 1 0 1 1 1 0 1 0 1 0 1 0 1 0 1 0 1 0 1 1 1 0 1 1 1 0 1 1 1 0 1 1 1 0 1 1 1 1 0 1 1 1 0 1 1 1 0 1 1 1 1 0 0 1 0 1 0 0 0 1 0 0 0 1 0 0 0 0 1 1 wraparound sum checksum
Cyclic Redundancy Check • view data bits, D, as a binary number • choose r+1 bit pattern (generator), G • goal: choose r CRC bits, R, such that • <D,R> exactly divisible by G (modulo 2) • receiver knows G, divides <D,R> by G. If non-zero remainder: error detected! • can detect all burst errors less than r+1 bits • widely used in practice (ATM, HDCL)
CRC Example Want: D.2r XOR R = nG equivalently: D.2r = nG XOR R equivalently: if we divide D.2r by G, want remainder R D.2r G R = remainder[ ]
Cyclic Redundancy Check • For a block of k bits transmitter generates n bit sequence • Transmit k+n bits which is exactly divisible by some number • Receive divides frame by that number • If no remainder, assume no error
Addition: Multiplication: = q(x) quotient x3 + x2 + x Division: x3 + x+ 1 ) x6 + x5 x6 + x4 + x3 dividend divisor x5 + x4 + x3 x5 + x3 + x2 3 35 ) 122 x4 + x2 105 x4 + x2 + x 17 x = r(x) remainder Cyclic Redunancy check Figure 3.55
Steps: 1) Multiply i(x) by xn-k(puts zeros in (n-k) low order positions) 2) Divide xn-k i(x) by g(x) 3) Add remainder r(x) to xn-k i(x) (puts check bits in the n-k low order positions): Cyclic Redundancy Check quotient remainder xn-ki(x) = g(x) q(x) + r(x) transmitted codeword b(x) = xn-ki(x) + r(x)
Generator polynomial: g(x)= x3 + x + 1 Information: (1,1,0,0) i(x) = x3 + x2 Encoding: x3i(x) = x6 + x5 x3 + x2 + x 1110 x3 + x+ 1 ) x6 + x5 1011 ) 1100000 x6 + x4 + x3 1011 x5 + x4 + x3 1110 1011 x5 + x3 + x2 1010 x4 + x2 1011 x4 + x2 + x x 010 • Transmitted codeword: • b(x) = x6 + x5 + x • b= (1,1,0,0,0,1,0) Cyclic Redundancy Check
Capability of CRC • An error E(X) is undetectable if it is divisible by P(x). The following can be detected. • All single-bit errors if P(x) has more than one nonzero term • All double-bit errors if P(x) has a factor with three terms • Any odd number of errors, if P(x) contain a factor x+1 • Any burst with length less or equal to n-k • A fraction of error burst of length n-k+1; the fraction is 1-2^(-(-n-k-1)). • A fraction of error burst of length greater than n-k+1; the fraction is 1-2^(-(n-k)). • Powerful error detection; more computation complexity compared to Internet checksum
Error Correction • Correction of detected errors usually requires data block to be retransmitted Not appropriate for wireless applications • Bit error rate is high • Lots of retransmissions • Propagation delay can be long (satellite) compared with frame transmission time • Would result in retransmission of frame in error plus many subsequent frames • Need to correct errors on basis of bits received • Basic idea: redundancy
Error Correction • Hamming distance: d(v1,v2) between two n-bit binary sequences v1 and v2 is the # of bits in which v1 and v2 disagree. • (n,k) block code: map each k-bit sequence into a unique n-bit codeword (n>k). • K=2,n=5 Consider one bit of error, say 00000->00001. d(00000,00001)=1; d(00111,00001)=2; d(11001,00001)=2; d(11110,00001)=4;
Error Control • Detection and correction of errors • Lost frames • Damaged frames • Automatic repeat request • Error detection • Positive acknowledgement • Retransmission after timeout • Negative acknowledgement
Automatic Repeat Request (ARQ) • Stop and wait • Go back N • Selective reject (selective retransmission)
Stop and Wait • Source transmits single frame • Wait for ACK • If received frame damaged, discard it • Transmitter has timeout • If no ACK within timeout, retransmit • If ACK damaged,transmitter will not recognize it • Transmitter will retransmit • Receive gets two copies of frame • Use ACK0 and ACK1
Stop and Wait - Pros and Cons • Simple • Inefficient
Go Back N (1) • Based on sliding window • If no error, ACK as usual with next frame expected • Use window to control number of outstanding frames • If error, reply with rejection • Discard that frame and all future frames until error frame received correctly • Transmitter must go back and retransmit that frame and all subsequent frames
Go Back N - Damaged Frame • Receiver detects error in frame i • Receiver sends rejection-i • Transmitter gets rejection-i • Transmitter retransmits frame i and all subsequent
Go Back N - Lost Frame (1) • Frame i lost • Transmitter sends i+1 • Receiver gets frame i+1 out of sequence • Receiver send reject i • Transmitter goes back to frame i and retransmits
Go Back N - Lost Frame (2) • Frame i lost and no additional frame sent • Receiver gets nothing and returns neither acknowledgement nor rejection • Transmitter times out and sends acknowledgement frame with P bit set to 1 • Receiver interprets this as command which it acknowledges with the number of the next frame it expects (frame i ) • Transmitter then retransmits frame i
Go Back N - Damaged Acknowledgement • Receiver gets frame i and send acknowledgement (i+1) which is lost • Acknowledgements are cumulative, so next acknowledgement (i+n) may arrive before transmitter times out on frame i • If transmitter times out, it sends acknowledgement with P bit set as before • This can be repeated a number of times before a reset procedure is initiated
Go Back N - Damaged Rejection • As for lost frame (2)
receiver individually acknowledges all correctly received pkts buffers pkts, as needed, for eventual in-order delivery to upper layer sender only resends pkts for which ACK not received sender timer for each unACKed pkt sender window N consecutive seq #’s again limits seq #s of sent, unACKed pkts Selective Repeat
data from above : if next available seq # in window, send pkt timeout(n): resend pkt n, restart timer ACK(n) in [sendbase,sendbase+N]: mark pkt n as received if n smallest unACKed pkt, advance window base to next unACKed seq # receiver sender Selective repeat pkt n in [rcvbase, rcvbase+N-1] • send ACK(n) • out-of-order: buffer • in-order: deliver (also deliver buffered, in-order pkts), advance window to next not-yet-received pkt pkt n in [rcvbase-N,rcvbase-1] • ACK(n) otherwise: • ignore
Example: seq #’s: 0, 1, 2, 3 window size=3 receiver sees no difference in two scenarios! incorrectly passes duplicate data as new in (a) Q: what relationship between seq # size and window size? Selective repeat: dilemma