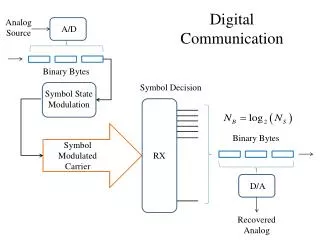
DIGITAL COMMUNICATION
DIGITAL COMMUNICATION. Packet error detection (CRC) November 2011 A.J. Han Vinck. Some books. 8. 16. 16. 8. Beginning. Ending. Header. Body. CRC. sequence. sequence. Cyclic Redundancy Check.

DIGITAL COMMUNICATION
E N D
Presentation Transcript
DIGITAL COMMUNICATION Packet error detection (CRC) November 2011 A.J. Han Vinck
8 16 16 8 Beginning Ending Header Body CRC sequence sequence Cyclic Redundancy Check • Add n-k bits of extra data (the CRC field) to an k-bit message to provide error detection function • For efficiency, want n-k << n • e.g., n-k = 32 for Ethernet and n = 12,000 (1500 bytes)
Automatic Repeat reQuest IDEA: ask for retransmission if error detected channel Pass data if no error ERROR ? If Yes: ask retransmission
Some properties of ARQ • Automatic Repeat-reQuest (ARQ) send ACK: packet OK send NACK: packet in error • Some modes: • Resend the packet if no ACK received before timeout • Use a predetermined maximum # of retransmissions until it is correctly received • Some ARQ protocols are • Stop-and-wait ARQ • Go-Back-N ARQ • Selective Repeat ARQ. • Hybrid ARQ is a combination of ARQ and forward error correction.
A pictorial view of coding Replace k information bitsby a unique n bit code word 2n vectors 2kcode words (code)
Error detection received vector not equal to one of the 2k code words. 2n vectors transmitted word received
Misdetection 2n vectors transmitted word received
Consider the following example transmitted 0 0 0 0 00 1 0 1 11 0 1 0 11 1 1 1 0 received 0 0 0 0 10 1 0 1 01 0 1 0 0 1 1 1 1 1 0 0 0 1 0 0 1 0 0 1 1 0 1 1 1 1 1 1 0 0 0 0 1 0 0 0 1 1 1 1 1 0 0 0 1 1 1 0 1 0 one error 0 1 0 0 0 0 0 0 1 1 1 1 1 0 1 1 0 1 1 0 1 0 0 0 0 1 1 0 1 1 0 0 1 0 1 0 1 1 1 0 0 0 1 1 0 1 1 0 0 1 1 0 0 1 1 0 1 1 0 0 1 1 0 0 0 0 0 1 1 1 0 1 1 0 1 1 0 0 1 0 Property: one error can be corrected two errors can be detected CHECK!
Error detection capability code words differ in at least dmin positions 2kvectors 0xx1x0x0 4 differences 1xx0x1x1 < = 3 errors can be detected up to dmin –1 errors are detectable
Misdetection 2n vectors 2kcode words for a random vector: the probability of false acceptance is (2k-1)/2n = probability of hitting the wrong code word
A polynomial description of the procedure Let a = (a0a1,..., ak-1) be k information bits the information is represented byA(X) = Xn-k(a0+a1X +...+ak-1 Xk-1) the checkpolynomial is F(X) = f0+f1X +...+fn-k Xn-k. The transmitted code polynomial or encoding procedure is C(X) = ( A(X) mod F(X) + A(X) ) Note that C(X) mod F(X) 0, and thus is C(X) a multiple of F(X).
A non-systematic procedure • Transmit C(X) = F(X)(a0+a1X +...+ak-1 Xk-1) then, C(X) modulo F(X) = 0!
Some examples • All coefficient operations are modulo-2 • ( 1+X + X3 ) (X + X2 ) = X+X2 + X4 +X2+X3 + X5 = X +X3 + X4+ X5 • errors change 0 1 and 1 0 • Ex: ( X + X4+ X5 ) modulo-(1 + X2 ) = 1 • Subtract as often as possible ( 1 + X2 ), but keep calculating mod-2
Ex:( X + X4 + X5 ) Modulo- (1 + X2 ) X + X4+ X5 X3 + X5 X3 X + X3 + X4 X2 + X4 X2 X + X2 +X3 X + X3 X X2 1 + X2 1 1
detection procedure Assume that we receive the polynomial R(X) = C(X) + E(X) where E(X) is a binary error polynomial i.e. an error vector ( 0,0,0,1,0) C(X) = X3 the decoder calculates R(X) mod F(X) - if the result = 0 no error detected - if the result ≠ 0,then an error is detected. The polynomial R(X) mod F(X) = 0 if and only if E(X) is a multiple of F(X).
performance ASSUME: the polynomial F(X) has the form F(X) = 1 + ... + Xn-k - degree n-k; - and a nonzero constant term, THEN: any error burst of length n-k has a polynomial representation that looks likeE(X) = Xi(1 +... + Xn-k-1 ) and can thus never be a multiple of F(X). F(X) is capable of detecting any burst of length n-k !
Performance cont‘d A nonzero burst of length (n-k) can never give a zero result. This can also be seen as follows n- k E(X) =0 0 0 0 0 0 ... 0 1 0 ... 1 0 ...1 0 0 0 XiF(X) =0 0 ... 0...1 ... 1 n-k+1 WHY:the binary representation of F(X) has length (n - k + 1) cancellation of the highest degree nonzero component in E(X) always gives a non-zero result.
CRC standard polynomials • CRC-8: x8+x2+x1+1 • CRC-10: x10+x9+x5+x4+x1+1 • CRC-12: x12+x11+x3+x2+1 • CRC-16: x16+x15+x2+1 • CRC-CCITT: x16+x12+x5+1 • CRC-32: x32+x26+x23+x22+ x16+x12+x11+x10+x8 x7+x5+x4+x2+1 • Ethernet uses CRC-32 • HDLC: CRC-CCITT • ATM: CRC-8, CRC-10, and CRC-32
Why these polynomials (CRC-16 and CRC-CCITT) ? • 1st property: Multiples of these polynomials have even weight Hence: error vectors of odd weight cannot be a multiple! • 2nd property: error vectors of the form E(X) = (1 + Xi ) are not divisible by F(X) for i < L, L larger than word length Try to check this property! • Conclusion: 1, 2 and 3 errors are detectable. CHECK!
SUMMARY for ERROR DETECTION Remark: We do all operations modulo 2 (XOR). F(X) = 1 + .... + Xn-k A packet has the form C(X) = A(X) mod F(X) A(X) = Xn-k (a0 + a1X + ... + ak-1 Xk-1 checksum information packet of length k. C = checksum a0 a1 a2 ... ak-1 n-k bits k bits data To calculate A(X) mod F(X), cancel highest nonzero term with F(X) until result has degree less than n-k
Cont‘d invert C at positions where the binary error vector E has ones: R = C E EXAMPLE C = checksum a0 a1 a2 ... ak-10 0 0 1 1 1 1 1 0 1 1 C =c0 c1 c2 ... 0 ... 1 ... 1 ... 0 cn-10 0 0 0 1 0 01 0 1 1 E =e0 e1 e2 ... 1 ... 1 ... 0 ... 0 en-10 1 0 1 1 0 1 1 R =r0 r1 r2 1 ... 0 ... 1 ... 0rn-11 1 1 0 check sum If no errorsC(X) mod F(X) = A(X) mod F(X) A(X) mod F(X) = 0! If errors{C(X) E(X) } mod F(X) = E(X) mod F(X).
Shift-register The following shift register can be used to calculate A(X) modulo (1 + X+ X3 ) a0 a1 a2 ...ak-1 Homework: give a description of the shift control to obtain the result
Cont‘d • Example: calculate ( 1 +X2 +X4 +X5 ) modulo ( 1 +X + X3 ) • In binary: ( 1 0 1 0 1 1 ) modulo ( 1 1 0 1 ) The operations in binary are as follows 1 0 1 0 1 1 1 +X2 +X4 +X5 0 0 1 1 0 1X2 ( 1 +X + X3 ) 1 0 0 1 1 0 0 1 1 0 1 0 X ( 1 +X + X3 ) 1 1 1 1 0 0 1 1 0 1 0 0 ( 1 +X + X3 ) RESULT: 0 0 1 0 0 0 X2 Homework: draw the corresponding shift register
CRC cont‘d • The following „clocked“ shift register can be used to implement CRC16: F(X) = 1 +X2 + X15 + X16 Data in 13 flip-flops Example: X16 modulo F(X) = 1 + X2 + X15 Question: When is the result A(X) mod F(X) equal to 0? What does this mean?
A simple method 0 1 1 0 0 1 1 0 0 1 1 0 0 0 1 1 0 0 1 1 0 0 0 0 0 0 0 0 0 0 0 0 0 Fill row wise Transmit column wise RESULT: any burst of length L can be detected L 0 1 1 0 0 1 1 0 0 0 0 0 0 0 1 1 0 0 1 1 1 1 0 0 0 0 0 0 0 0 0 1 1 row parity
A simple code: the single parity check code • Make the number of ones in a code word even: • Method 1 • Take F(X) = 1 + X, i.e. C(X) = F(X) A(X). • C(X= 1) adds up the number of ones and since X = 1 is a root of F(X), the result is 0. • Method 2. • Use the n-th bit to make the parity of a word even • CONCLUSION: detection of any number of odd errors • Efficiency: R = (n-1)/n
ISBN checksum: checksum for 10-digit ISBN - Given 9 digit product code. Starting at leftmost digit: - multiply corresponding digit by 10, 9, 8, ... down to 2 inclusive - add the resulting numbers: add digit 10 such that the result is divisible by 11 the number 10 is written as X e.g., 0-201-61586-X is valid. The last digit has to be 10 (= X). 10*0 + 9*2 + 8*0 + 7*1 + 6*6 + 5*1 + 4*5 + 3*8 + 6*2 + 1*10 = 122 + 10 = 132 = 12*11 • detects transpositions and single digit errors - an error e at position I gives as result the value eI modulo 11 0 - detection of an transposition error of A and B: A I + B (I-1) BI + A(I-1) = AI + B(I-1) – A + B the value ( – A + B ) 0 modulo 11 for A B
Combining error detection-correction • G1(X) G2(X) generates a code with minimum distance D2 • G1(X) generates a code with minimum distance D1 < D2 • C(X) = I(X) G1(X) G2(X) = I’(X)G1(X) decoding: step 1: correct a maximum of ë( D1 – 1 )/2û errors with G1(X) step 2: detect the remaining errors with G1(X)G2(X) properties: 1. t £ë( D1 – 1 )/2û errors correctable 2. t £ D2 - 1 - ë( D1 – 1 )/2û errors detectable Homework: construct some examples A.J. Han Vinck
Combining error detection-correction • Example: n k dmin generator polynomial (octal) 63 57 3 G1 = 103 (octal) 51 5 G2 x G1 = G1 x (127) 45 7 G3 x G2 x G1= G2 x G1 x (147) A.J. Han Vinck
Example: bluetooth • Three error correction schemes are defined for Bluetooth: • 1/3 rate FEC, a simple repetition • 2/3 rate FEC, a shortened Hamming Code (10,15) • ARQ scheme for data (automatic retransmission request) • FEC schemes reduce the number of retransmissions • A CRC code decides whether a packet/header contains errors, i.e. • transmit C(X) = I(X) g(X) • receive R(X) = C(X) + E(X) • check R(X) modulo g(X) = 0 ? A.J. Han Vinck
Proper codes Linear block codes do not necessarily obey the 2-(n-k) bound. In other words, a code is proper if PU is monotonically increasing in p, for 0.0 p 0.5. Hamming codes and primitive double error-correcting BCH codes are proper. To illustrate the above behavior, we compare the standard CRC-16 for a length 80 packet with a double error correcting BCH code of length 81 and 17 redundant digits. Detection error probability as a function of the channel error probability.
Unidirectional errors detection: Berger codesapplication: memory systems Errors: unidirectional, i.e. In a word only from 0 to 1 (or from 1 to 0) log2 (n+1) check bits indicate the # of zeros in the first part n binary data bits Example: n = 7; log2 (n+1) = 3 1 0 0 0 1 1 10 1 1 Suppose errors from 1 to 0 in the first part only: number of zeros does not match check in the second part only: idem dito in the first and second part: the first part gets more zeros the second part # gets smaller CONCLUSION: any number of errors detectable!
Some practical info INTEL website: http://datasheets.chipdb.org/Intel/x86/Pentium/Embedded%20Pentium%AE%20Processor/ERRORDET.PDF Xilinx website: http://www.xilinx.com/support/documentation/application_notes/xapp645.pdf Altera website: http://www.altera.com/literature/an/an357.pdf