Eap STate machinE dEsign teaM (ESTEEM)
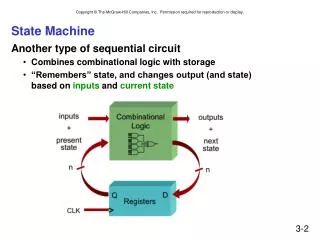
The ESTEEM team is focused on refining the EAP state machine to ensure compatibility with IEEE 802.1aa and RFC 2869 Bis. The goals include correctly managing optional identity exchanges, method sequences, re-authentication, and retransmission. Key contributions from team members address issues such as identity requests, duplicate detection, and the handling of various states within the protocol. Weekly conferences facilitate progress and discussion on position papers and state machine drafts, aiming for a comprehensive and efficient EAP state machine design.


Eap STate machinE dEsign teaM (ESTEEM)
E N D
Presentation Transcript
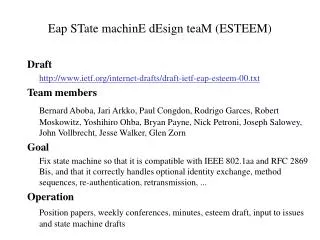
Eap STate machinE dEsign teaM (ESTEEM) Draft http://www.ietf.org/internet-drafts/draft-ietf-eap-esteem-00.txt Team members Bernard Aboba, Jari Arkko, Paul Congdon, Rodrigo Garces, Robert Moskowitz, Yoshihiro Ohba, Bryan Payne, Nick Petroni, Joseph Salowey, John Vollbrecht, Jesse Walker, Glen Zorn Goal Fix state machine so that it is compatible with IEEE 802.1aa and RFC 2869 Bis, and that it correctly handles optional identity exchange, method sequences, re-authentication, retransmission, ... Operation Position papers, weekly conferences, minutes, esteem draft, input to issues and state machine drafts
ESTEEM Position Papers • Issues with the EAP State MachineYoshihiro Ohba • Comparison of EAP state machines with RFC 2284bisBryan Payne, Nick Petroni • EAP State Machine CompletenessJari Arkko • When can notif/nack/... be sent?Bernard Aboba • Communication between the Method and EAP layerBernard Aboba • EAP switch and multiple methodsJohn Vollbrecht
ESTEEM Decisions Basic issues • Allow notification in any state; can’t be Nakked • EAP layer (not method) handles duplicate detection and id numbers (#25) • Follow IEEE 802.1aa format in state machine definition Identity requests • Identity request/response can only appear between methods • Our preference is that identity requests be optional. • Leaning towards making Nak disallowed for Identity Request Success and failure indications • If an authenticated indication exists, should not believe alternative indications • Link-layer indications provided to EAP MUST be processed (#2) • Unprotected success indications are only accepted after method is complete (#2) • Peers should be able to accept Failure in unauthenticated state • Authenticated indications require support for sequences or tunnels (#10) Sequences • Methods can’t be executed in parallel; Nak if received • No pre-negotiation of method sequencing capability, just Nak afterwards (#7)