Understanding and Combating Cyberbullying: Insights from the ASU STEM Conference
Cyberbullying represents a modern form of bullying that utilizes technology to inflict harm, often targeting individuals through social media platforms like Facebook and MySpace. At the ASU STEM Conference, Mark Crouch, Ed.D., explored the dynamics of cyberbullying, highlighting its prevalence and impact on youth. Participants learned about the importance of safeguarding personal information online, the significance of strong passwords, and ways to support anti-bullying initiatives. It is crucial for students to understand the risks of online interactions and to seek guidance from trusted adults when faced with cyberbullying.

Understanding and Combating Cyberbullying: Insights from the ASU STEM Conference
E N D
Presentation Transcript
Cyberbullying Expanding Your Horizons ASU - STEM Conference February 23, 2013 Mark Crouch, Ed. D.
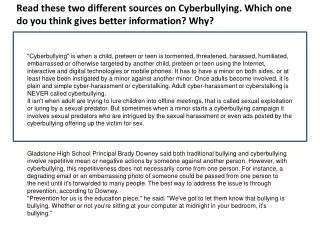
Traditionally - A bully is primarily a person responsible for bullying Bullying is a form of abuse. It involves repeated acts over time attempting to create or enforce one person's (or group's) power over another person (or group).
Today - Cyber-bullying is "the use of information and communication technologies to support deliberate, repeated, and hostile behavior by an individual or group, that is intended to harm others". - Wikipedia
What that means is: Bullies in the schoolyard now have a new place to wield their punches – cyberspace.
What that means is: “Cyberbullying,” as it’s now called, is like regular bullying except it’s done online through sites like Facebook and MySpace and the use of cell phones
Broken Friendship What are some of the things that we use passwords for? • E-mail • Instant Messenger • Web sites • Bank accounts • ????
Broken Friendship Why do you think the girl in the story gave her password to her best friend? • Was it a good reason?
Broken Friendship • What types of things can happen to her now that her password is out? • What should the girl do right away?
Passwords Do not use common words or names • Do not use your birthday • Do not use your pet’s name • Do not use your SSN
Passwords Do use random passwords • Do use letters AND numbers • Do mix lower case and upper case • Do use symbols such as $ @ #
Password Example m h a l li f w w a s maryhad alittle lamb its fleece was white as snow
Better Password Example M h a L l i f w W a s Even Better - M h a L1i f w W a $
You can’t take it back How do you think the victims felt? Have you ever been ridiculed before? How did it feel?
You can’t take it back Why did the boy rate the girls? Do you think that girls ever rate boys like this?
You can’t take it back What would you do if you heard that a friend was going to rate some other students on the Internet?
What can YOU do? Never post or share your (or your friends’) personal information online. Examples: full name address telephone number school name parents’ names credit card number Social Security number
What can YOU do? Never share your Internet passwords with anyone (except your parents).
What can YOU do? Never meet anyone face-to-face whom you only know online.
What can YOU do? Talk to your parents about what you do online.
What can YOU do? Be “anti-bully”