Secure Ranging Function Requirement for 802.11az Protocol Enhancement
90 likes | 110 Vues
Proposal for adding secure range measurement functionality in 802.11az protocol to address security limitations of current FTM protocol and prevent fraudulent ranging.

Secure Ranging Function Requirement for 802.11az Protocol Enhancement
E N D
Presentation Transcript
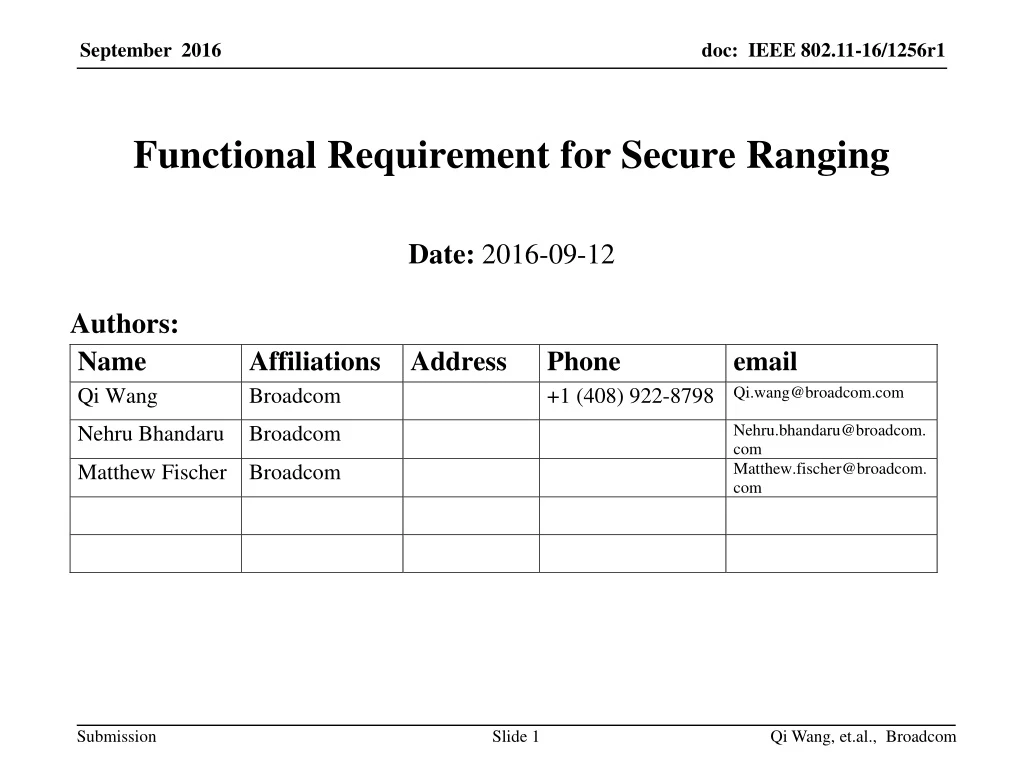
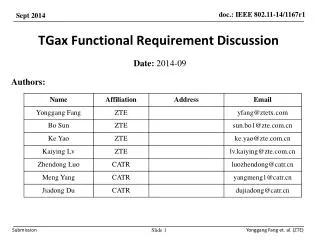
Functional Requirement for Secure Ranging Date:2016-09-12 Authors: Qi Wang, et.al., Broadcom
Abstract • This document proposes an additional function requirement for 802.11az. Qi Wang, et.al., Broadcom
Security Limitation of Current FTM Ranging Protocol • Some uses cases require security for ranging • Proximity detection to point of sale (e.g.,Starbucks) • Unlock assistance to personal laptop or tablet • Unlock your car • Unlock a locker at sports facility • Serve as entry ticket, e.g., concert, sports event • Alternative access for building, e.g., in lieu of ID cards • The current FTM ranging protocol, as defined in IEEE 802.11REVmc D8.0 [1], lacks security protection of the RTT measurements and may be easily compromised. Qi Wang, et.al., Broadcom
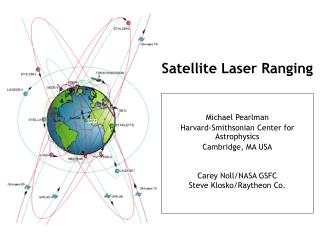
Security Issue of FTM STA1 (Responding STA) STA2 (Initiating STA) FTM Request Ack FTM_m payload contains [t1_(m-1), t4_(m-1)] t1_m t2_m Fake Ack t4_m’ t3_m Authentic Ack t4_m FTM_(m+1) payload contains [t1_m, t4_m’] t1_(m+1) t2_(m+1) Fake Ack t4_(m+1)’ t3_(m+1) Authentic Ack t4_(m+1) Fig. 1 Illustration of an FTM ranging security issue • According to [1], the FTM frames and Ack frames are not protected. • A malicious device can transmit fake Ack frames, which pretend to be the Ack frames from the Initiating STA, to the Responding STA. • Because an Ack is transmitted within an SIFS, the authentic Ack arrives in the middle of the fake Ack reception at the Responding STA. An implementation uses implementation specific criteria to decide whether to declare a collision (and abandon the t4_m capturing) or to decode either the Fake Ack or the Authentic Ack. • Using the implementation specific criteria, when the fake Ack is decoded successfully, the Responding STA obtains the wrong t4_m and includes it in the payload of the subsequent FTM frame, which causes the Initiating STA to derive the wrong RTT. Qi Wang, et.al., Broadcom
Feasibility of Secure Ranging • The methods proposed in IEEE 802.11az 2016/1020 [2] demonstrate the feasibility of improving ranging security in an associated mode. Qi Wang, et.al., Broadcom
Proposed Functional Requirement • We propose to add the following requirement to the 802.11az Functional Requirement document [3] under the section of 2.1.1 “Range measurement and coverage” “TGaz Rx: The 802.11az protocol shall describe one or more mechanisms to provide secure range measurement in an associated mode.” Qi Wang, et.al., Broadcom
Straw Poll • Do you support to add the following requirement to the 802.11az Functional Requirement document [3] under the section of 2.1.1 “Range measurement and coverage” “TGaz Rx: The 802.11az protocol shall describe one or more mechanisms to provide secure range measurement in an associated mode.” Result: Yes: No: Abstain: Qi Wang, et.al., Broadcom
References • [1] IEEE Std 802.11 REVmc_D8.0, IEEE Standard for Information Technology – Telecommunications and information exchange between systems, local and metropolitan area networks – Specific requirements, Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications • [2] “Security enhancement to FTM”, IEEE 802.11-16/1020 • [3] “Proposed 802.11az Functional Requirements”, IEEE 802.11-16/424r3 Qi Wang, et.al., Broadcom