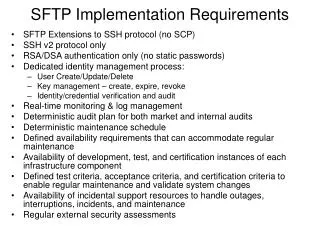
SFTP Implementation Requirements
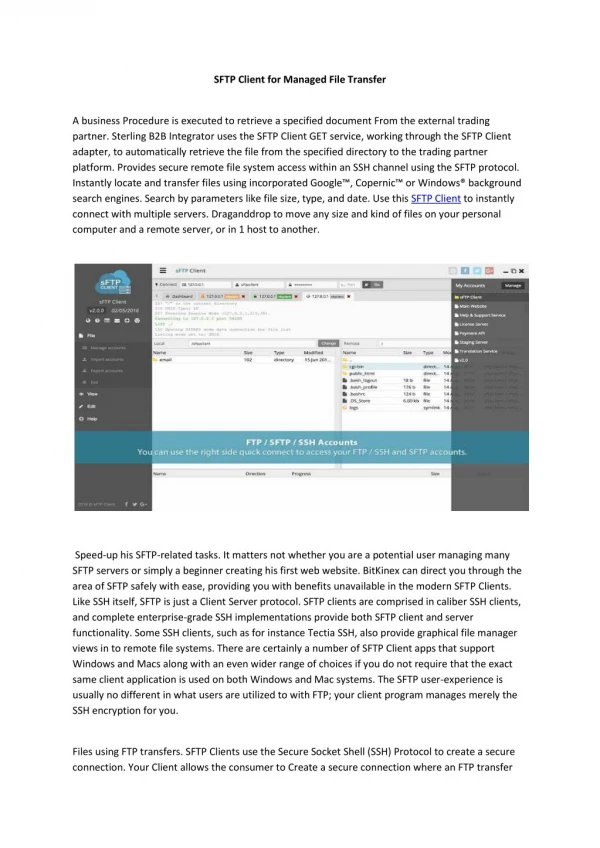
This document outlines the key requirements for implementing SFTP over SSH protocol, emphasizing the use of SSH v2 only and RSA/DSA authentication methods, with no static passwords. It includes a dedicated identity management process for user lifecycle activities such as creation, updating, and deletion, as well as comprehensive key management. Additionally, it details the need for real-time monitoring, log management, deterministic audit plans, and a well-defined maintenance schedule. Regular security assessments and the availability of development and certification environments are also specified.

SFTP Implementation Requirements
E N D
Presentation Transcript
SFTP Implementation Requirements • SFTP Extensions to SSH protocol (no SCP) • SSH v2 protocol only • RSA/DSA authentication only (no static passwords) • Dedicated identity management process: • User Create/Update/Delete • Key management – create, expire, revoke • Identity/credential verification and audit • Real-time monitoring & log management • Deterministic audit plan for both market and internal audits • Deterministic maintenance schedule • Defined availability requirements that can accommodate regular maintenance • Availability of development, test, and certification instances of each infrastructure component • Defined test criteria, acceptance criteria, and certification criteria to enable regular maintenance and validate system changes • Availability of incidental support resources to handle outages, interruptions, incidents, and maintenance • Regular external security assessments