Radware AppWall Web Application Firewall February 2009
Radware AppWall Web Application Firewall February 2009. Page 1. Agenda. Web Application Security Challenges Introducing Radware AppWall Key Features, Business Benefits and Differentiation AppWall Management Model Offering and Technical Specifications Summary. Slide 2.


Radware AppWall Web Application Firewall February 2009
E N D
Presentation Transcript
Radware AppWall Web Application FirewallFebruary 2009 Page 1
Agenda • Web Application Security Challenges • Introducing Radware AppWall • Key Features, Business Benefits and Differentiation • AppWall Management • Model Offering and Technical Specifications • Summary Slide 2
What is the Cost of being Attacked? January 19, 2008 Hackers hit Scientology with online attack The Church of Scientology has been hit by online attackers calling themselves "Anonymous." March 24th, 2008 Microsoft confirms Word attacks March 22, 2008 Supermarket Breach Calls PCI Compliance Into Question Hannaford Bros. exposed millions of credit and debit card numbers. April 1, 2008 Advance Auto Parts store spills data to hackers 56,000 credit card records stolen Hackers Disable Tahoma Site Posted on: Sunday, 27 January 2008, 12:00 CST 10 March 2008 Pentagon cyber attack more serious than previously assumed The cyber attack on parts of the Pentagon network last June may have had more serious consequences for network security than previously publicized. Slide 5
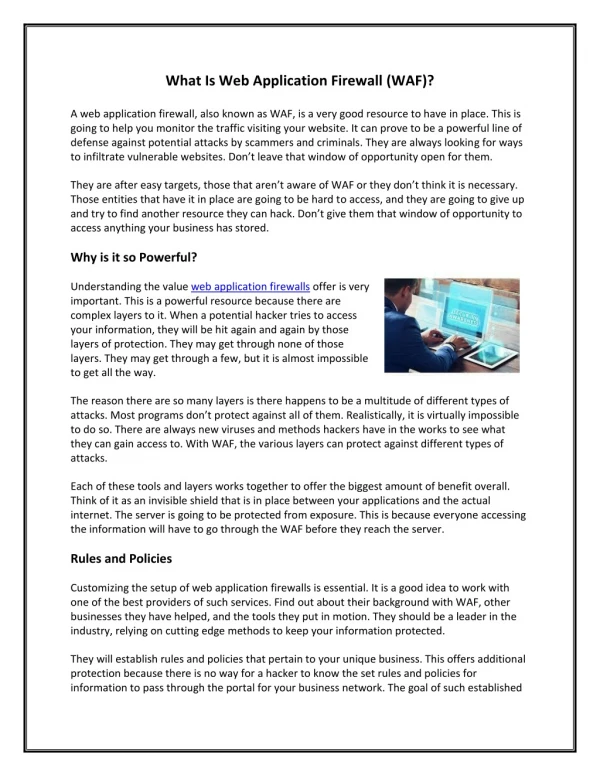
Web Attack Statistics Research shows that 70% of cyber attacks are performed at the Web application level Gartner 125 million records have been compromised in 2007 Identity Theft Center 90% of public Web sites are vulnerable to attack WhiteHat Security 70% of Web sites are vulnerable to cross-site scripting Acunetix Slide 6
Reported Web Application Vulnerabilities Source: The National Vulnerability Database - http://nvd.nist.gov/statistics.cfm Slide 7
Web Application Risks • Potential damage: • Defacement • Client attacks • DoS/DDoS • Data manipulation / retrieval / deletion • Attack techniques: • SQL / Command injection • Cross-site scripting (XSS) • Cookie poisoning • Session hijacking • More…. Slide 8
OWASP Top Ten List OWASP (Open Web Application Security Project) is a worldwide free and open organization focused on improving the security of application software. More information: http://www.owasp.org/images/8/85/OWASP_Top_Ten.ppt Slide 9
Web Applications Security Threats Statistics (http://www.webappsec.org/projects/statistics/) Most prevalent vulnerabilities Vulnerability frequency by Types Slide 10
Scoping the Problem Web applications are: Exposed to virtually everyone Easy to exploit: all you need is a Web browser The entire system is open to attack Minimal attention to security during development Can target different layers, components & software modules Traditional protection techniques are inadequate Advanced hacking tools such as HTTP Proxies are available online Thousands of Web security vulnerabilities Slide 11
Payment Card Industry (PCI) • Payment Card Industry (PCI) Data Security Standard (DSS) is a standard developed by the major credit card companies as a guideline to help organizations that process card payments prevent credit card fraud, hacking and various other security issues • Ensure that all Web-facing applications are protected against known attacks by applying either or both of the following methods: • Installing an application-layer firewall in front of Web-facing applications – Radware AppWall • Having all custom application code reviewed for common vulnerabilities by an organization that specializes in Application security and then fixing code • - from PCI DSS 1.1, section 6.6 Starting June 30, 2008 PCI DSS 1.1 section 6.6 is a major requirement in many countries across the globe Slide 12
Introducing Radware AppWall Page 13
Radware AppWall AppWall is a Web Application Firewall (WAF) securing Web Applications and enabling PCI compliance AppWall detects threats, blocks attacks and generates events AppWall intercepts and monitors all incoming and outgoing application-layer traffic An integral part of Radware ADC solution Helps organizations meet regulatory requirements Slide 14
Radware Application Delivery Solution • XML message acceleration • XML data admission control • XML service privacy & integrity • Web Services interoperability Data Center Message Queuing System AppXML Partners • High Availability with Real-time Failure Bypassing • Superior Global Load Balancing • Smart Health Monitoring and Failure Detection • QoS Bandwidth Management and Traffic-shaping • Scalability & Investment Protection • SSL offloading • HTTP compression • Caching • HTTP and TCP optimization & acceleration Mainframe ESB AppDirector Customers Web & Portal Servers Database servers AppWall Employees • Out-of-the-box security policies • Auto-configuration with learning mode • Alerting, forensics and reporting • Supporting WAF cluster deployment • Integration to 3rd party Enterprise Management Systems & Users Application Servers Slide 15
AppWall Differentiators Integral part of Radware ADC solution Standardized on the OnDemand Switch hardware platform Unique, “pay-as-you-grow” scalability by device Minimal time to protection through out-of-the-box security policies Precise security coverage through fine grain policy control while optimizing resource usage Automatic protection level escalation When AppWall cluster is deployed When several AppWall devices are deployed is different locations in the organization Slide 16
AppWall Advantages Easy to configure through Learning Mode with Auto Configuration Complete alerting, forensics, and reporting capabilities Integration to leading Enterprise Management Systems Syslog, ODBC, SMTP, OPSEC Highly performing – sub millisecond latency Comprehensive, simplified management Enabling to centrally synchronize the configuration and learned data to all devices Slide 17
Highly Performing WAF • No limit on the number of AppWall Cluster members • Performance scalability based on the requirement of the application • Introducing more inspection power with time, controlling costs • Fine grain security enforcement based on Application Paths configuration • Define optimized Security Policy Per Application Path • Dynamically adapt to the needs of the application, resulting in: • Inspection of exactly what is required • Optimized application performance • Optimized system Slide 18
AppWall Events Dashboard Slide 19
Events Statistics Slide 21
Comprehensive Security Filters Coverage • Vulnerabilities Security Filter • Validates HTTP requests using rule-based validations that detect a variety of application layer security threats (Signatures based). • Brute Force Security Filter • Protects against Brute Force attacks by creating action rules and blocking IP addresses of potential attackers • Database Security Filter • Validates HTTP requests parameters by detecting harmful SQL command injections • HTTP Methods Security Filter • Validates the HTTP request methods are approved • Files Upload Security Filter • Validates file uploads and uploaded file access methods are approved • Safe Reply Security Filter • Detects disclosure and unauthorized content in outbound reply messages, such as credit-card and Social Security numbers • Session Security Filter • Prevent remote users from manipulating sessions state information and submitting it to the Web Application Slide 23
Comprehensive Security Filters Coverage • Allow List Security Filter • Validates that HTTP requests are approved • Path-Blocking Security Filter • Validates in an HTTP request is forbidden, such as unauthorized attempts to access common files and folders • Global Parameters Security Filter • Validates HTTP requests parameters values are acceptable according to listed global definitions • Parameters Security Filter • Validates HTTP requests parameters values are acceptable according to listed definitions • Web Services Security Filter • Validates that services and operations are approved • XML Security Security Filter • Validates post request body XML and parses XML-encapsulated values into parameters for distribution to subsequent Security filters for validation • Logging Security Filter • Logs HTTP headers and bodies for tracking Slide 24
AppWall Technical Specifications Slide 26 Slide 26
AppWall on OnDemand Switch 1 XL Models Slide 27 Slide 27
Summary Any questions? Page 28
Summary Highly Performing WAF Slide 29
Summary “Pay-as-you-Grow” Scalability through Cluster Support Highly Performing WAF Slide 30
Summary Highly Performing WAF Simple Deployment, Fully Automatic Configuration Slide 31
Summary Comprehensive Web Applications security coverage Highly Performing WAF Simple Deployment, Fully Automatic Configuration Slide 32
Summary Radware AppWall is a Web Application Firewall (WAF) securing Web Applications and enabling PCI compliance offering: Comprehensive Web Applications security coverage Simple deployment and configuration Easy to install – out-of-the-box security deployment Easy to configure – learning mode with auto configuration Integrated with Radware ADC Solution “Pay-as-you-Grow” scalability through cluster support Highly performing WAF Complete alerting, forensics, and reporting Slide 33