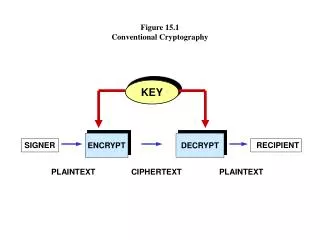
Conventional Cryptography
Conventional Cryptography. Dr. Ron Rymon Efi Arazi School of Computer Science IDC, Herzliya. 2010/11. Pre-Requisites: Simple Math Background. Overview. Symmetric Cryptography Cipher Block Modes Key Management Message Authentication Using Conventional Cryptography.


Conventional Cryptography
E N D
Presentation Transcript
Conventional Cryptography Dr. Ron Rymon Efi Arazi School of Computer Science IDC, Herzliya. 2010/11 Pre-Requisites: Simple Math Background
Overview • Symmetric Cryptography • Cipher Block Modes • Key Management • Message Authentication Using Conventional Cryptography
Symmetric Cryptography Main sources: Network Security Essentials / Stallings Applied Cryptography / Schneier
Symmetric Cryptography Protocol • A typical protocol • Alice and Bob agree on cryptosystem (algorithm) • Alice and Bob agree on a key • Alice encrypts her message with the key • Alice sends the message to Bob • Bob decrypts the messages using same key • A common variation is where a new key is issued for each “session” (set of messages) and is exchanged encrypted using the “master” key
Feistel Networks • Most block encryption algorithms use this general structure, due to Horst Feistel (1973) • Inputs: Plaintext (halved) , Key, Round function F • Uses n rounds, in each (e.g., n=16) • Inputs: Li and Ri ; Ki is derived from K (sub-key) • Li+1=Ri • Ri+1=LiF(Ri,Ki) • F (“round function”) selects certain bits, duplicates some, and permutes them. Ki is derived from K • Final ciphertext is combination of Ln and Rn • At IBM, Feistel built Lucifer, the first such system
Notes on Feistel Cipher Structure • Decryption: The same process is reversible • Ri-1=Li • Li-1=RiF(Ri-1,Ki-1) • Same algorithm can be used but with keys reversed • Security Considerations • Larger block size results in fewer blocks and increased security • Larger key size also increases security (recall Shannon) • More rounds considered to offer better security (?) • Greater complexity of subkey generation may help security • Greater complexity of round function may increase security
Design Goals for Block Ciphers • Highly secure – more of everything… • Fast – fewer rounds that use simpler operations • Low communication overheads • Low battery consumption in hand-helds • Easy to implement in hardware • Simple, ubiquitous operations • Efficient in memory usage • Can run on a smart card • Require less secret material (keys, boxes) • Sometimes put on expensive tamper-proof memory
Design Principles for Feistel Round Function • Feistel is a family of algorithms • Depends on choice of F, and subkey generation algorithm’ • Can be designed to fit needs • Non-Linearity. F is as difficult as possible to approximate with a set of linear equations • Avalanche • Strict Avalanche Criterion (SAC) – with the change of any one input bit, every output bit shall change with probability of exactly ½ • Bit Independence Criterion (BIC) – output bits i,j shall change independently from each other when an input bit is inverted • Guaranteed Avalanche – at least n output bits will change whenever any single input bit is inverted
Data Encryption Standard (DES) • Without a standard, software and hardware cannot interoperate, or at least it is very expensive • In 1973, National Institute for Standards and Technology (NIST) issued RFP for Data Encryption Algorithm (DEA) • provide high level of security • completely specified and easy to understand • the security must reside in the key • available to all users • adaptable to diverse applications • economically implementable in hardware • efficient to use • validated • exportable
Data Encryption Standard (DES) • NIST (NBS) issued a Request For Proposal (RFP) • Only serious proposal came from IBM • Patented and based on Lucifer (Feistel et al) • NIST issued a Request For Comments (RFC) • For first time, a crypto algorithm is reviewed by experts (NSA) • Quite a few were concerned about NSA backdoor • NSA reduced the key size from 112 to 56 bits • Diffie and Helman presented a $20MM 1-day DES cracking machine • NSA had also changed the original “S-boxes” design • There were some claims of linearity in the new design • DES was adopted in 1977, and renewed in 1983 • In 1987, under NSA pressure, DES almost not re-certified • Concerned about the details of the algorithm being open and available to software implementations • Certified only hardware implementations until 1994
Data Encryption Standard (DES) • A Feistel block cipher structure • 64-bit blocks • 56-bit keys • 16 rounds • Adds initial and final permutation of the text (irrelevant to security) • Key shifted circularly for next round, and 48 bits are selected for Ki
One Round of DES • Key Transformation • Each key-half is shifted 1 or 2 bits in each round (per given table) • The 56 key bits are permuted and 48 bits are chosen (per table) • Text transformations • Expansion of Ri from 32 to 48 bits (size of key) • Avalanche effect – some bits are duplicated • 48 bits are XORed with Ki • Substitution, using 8 S-Boxes with 6-bit input and 4-bit output • S-boxes are well chosen to introduce non-linearity • 32 bits are permuted according to specified P-Box • 32 bits are XORed with Li to create Ri+1
Data Encryption Standard (DES) • Confusion • Obtained through permutations, substitutions, and number of rounds • Diffusion • Good avalanche effect – 1 bit difference in plaintext quickly results in a large difference in bits, even after few rounds • Performance • Software implementations were slow • On IBM Mainframe 32,000 blocks / second • Hardware implementations were very fast • VLSI Technology 6868 (“Gatekeeper”) DESes in 8 clock cycles • DEC built GaAs gate array that DESes 16.8 million blocks / second
DES Avalanche Effect • (a) Difference between two plaintexts with 1-bit original difference • (b) Difference between two keys with 1-bit original difference
Data Encryption Standard (DES) • Weak keys • Some keys will result in identical subkeys, e.g., if all 0’s, or all 1’s • Claims that the S-boxes were weakened by the NSA • Notable DES Attacks • In 1990, Eli Biham and Adi Shamir presented differential cryptanalysis • A chosen-plaintext attack that uses two plaintexts with specific difference. Then, based on the difference in the ciphertext (and also internal rounds), one can update the a priori probability of keys • Similar to the “T-attack” that was originally developed at IBM and was classified by NSA • In 1993, Mitsuru Matsui showed linear cryptanalysis attack • Certain XORs of plaintext and ciphertext bits will result in a certain XOR of key bits with some probability p1/2
EFF’s DES Cracker • In 1996, a public debate about security of DES. • US Agencies (FBI, NSA) claiming that they cannot practically break DES (takes weeks on many computers) • Offer companies software export license in return for establishing a “key recovery” system • Electronic Frontier Foundation DES Cracker project • DES is slow in software but fast in hardware • Used easily available Field Programmable Gate Arrays • Total budget is $200,000 • Used hardware to winnow false positives (plaintext recognizer) then software to test the remaining • A 1996 paper by top cryptographers suggests a minimum key size of 75 bits, and 90 bits needed to hold for 20 years
RC5 • Also a block cipher, invented by Ron Rivest (1994) • Similar in structure to Feistel • Operations: XORs, Additions (mod bitsize), and Rotations • Word-oriented, Low-cycle operations – Fast in software • Variable length blocks, keys, and number of rounds (r) • Each block is made of 2 w-bits blocks (A, B) (w=16,/32/64) • Each key is made of bx8 bits (0<b<255; can be larger than a block) • Round keys (S2i , S2i+1), each with w bits, are derived from the key • Encryption and decryption consist of r rounds • With 16+ rounds, RC5 resists differential attack • 12 round RC5 shown susceptible with 244 chosen plaintexts • Data-dependent shifts is one of the innovations of RC5
RC5 Encryption and Decryption A B • S2i ,S2i+1 are round sub-keys • Start: A=A+S0 ; B=B+S1 • In each encryption round (i=1..r) • A=((A B)<<<B) + S2i • B=((A B)<<<A) + S2i+1 • In each decryption round (i=r…1) • B=((B-S2i+1)>>>A) A • A=((A-S2i)>>>B) B • Finish: A=A-S0 ; B=B-S1 S2i S2i+1 A B
RC5: Subkey Generation • Sub-keys are a mix of original key with two words • P=Odd((e-2)2w) – e is the natural log ≈ 2.71 • Q=Odd((Phi-1)2w) – Phi is golden ratio (1+sqrt(5))/2 ≈ 1.61 • Initialize a c-word sub-key array • S0=P • For i=1…2r+1 • Si=(Si-1+Q) • Mix with key bits • L is a c-word array filled with 0-padded concatenation of key bits • c rounds the key bytes into words • i=j=0; A=B=0; • Do 3n times (n=max{2(r+1),c}) • A= Si=(Si +A+B)<<<3 • B= Lj=(Lj +A+B)<<<(A+B) • i=(i+1) mod 2(r+1) • j=(j+1) mod c
Variants in Other Block Ciphers • Blowfish (Schneier) • Simple: additions, XORs, and table lookups • Table lookups may require large memory • Variable key length • CAST • The round function differs from one round to next • Int’l Data Encryption Alg (IDEA), Lai and Masey • Plaintext, key, and ciphertext are divided to 4 parts • Uses XORs, additions, and multiplications in 8 rounds • 128-bit key, 52 16-bit subkeys (can be independent) • Resists differential cryptanalysis • Used in PGP
Triple DES (3DES) • In 1999, DES becomes too weak • NIST replaces DES with 3DES • 3DES (EDE) uses three 56-bit keys • C=Ek3(Dk2(Ek1(P))) • P=Dk1(Ek2(Dk3(C))) • Note: if K1=K2 then 3DES=DES • Double encryption doesn’t work well • Merkle-Hellman chosen plaintext man-in-the-middle attack requires only 2n+1 trials (instead of 22n) • Quintuple encryption also ok • C=Ek1(Dk2(Ek3(Dk2(Ek1(P)))
Stream Ciphers Keystream Generator Ki • A pseudorandom keystream generator • Keystream depends only on generating key • Keystream bits are XORed with the plaintext to produce the ciphertext, and vice-versa • Similar to one-time pads, except that not strictly random • Keystream period should be as long as possible • Other options • Keystream may change according also to previous encryptions, block index, etc. • In synchronous stream ciphers, keystream does not depend on text, otherwise, it is called self-synchronizing Pi Ci
RC4 • Byte-based stream cipher, with variable key size • Uses an S-box, with all possible 8-bit key-entries • Initialized so that S[i]=i, i=0…255 • S[i]’s are initially permuted, based on the key • j=0 • for i=0 to 255 • j=(j+S[i]+K[i]) mod 256; // K[i] is original key • Swap S[i] and S[j] • In each iteration • Indices i,j are updated • i=i+1 mod 256; j=(j+S[i]) mod 256 • S[i] and S[j] are swapped for current i,j • K=S[(S[i]+S[j] mod 256] • The keystream K is then XORed with the plaintext • RC4 with up to 40-bit keys was approved by NSA, and is used in Lotus Notes, CDPD, WEP, and original SSL
Summary of Cryptography Algs • Block by block • Rounds structure • Key generation • Mixing key bits for confusion and diffusion • Use of state matrix for session key • Encryption • Mix round key with plaintext for confusion/diffusion • Bit permutation • Substitution with S-boxes for non-linearity • Data dependent operations (e.g., shifts) to add complexity • Use of processor-friendly operations for software speed • Key size, block size, many rounds add to security • Multi-application of encryption with more key bits • Block ciphers vs. Stream Ciphers
Advanced Encryption Standard (AES) • NIST put out the RFP in 1997 • In meantime, 3DES replaces DES in 1999 • Main criteria for evaluation • Security • Cost and performance of implementation • General evaluation of design features • Five finalists (out of 21): • In October 2000, NIST recommended Rijndael • Approved 2002
Rijndael Block Cipher • By Belgians Joan Daemen, and Vincent Rijmen • Variables block size and key size • Number of rounds determined by block and key size • Does not use Feistel structure • Instead, each round uses a state and 4 operations • Non-linear layer, uses optimized S-boxes, for confusion • 16x16 S-box with all byte values, and a separate inverse S-box • Linear mixing layer for diffusion • Row shifts on the state matrix • Column mixes on the state matrix • Key addition layer, using a simple XOR • AES set to use Rijndael with 128bit blocks, key size of 128-192-256 bits, and 10-12-14 rounds
Cipher BlockModes of Operation Main sources: Network Security Essential / Stallings Applied Cryptography / Schneier
Cipher Block Modes of Operation • FIPS 81 defines four “modes” of operation for block ciphers: • Electronic Codebook (ECB) • Cipher Block Chaining (CBC) • Cipher Feedback (CFB) • Output Feedback (OFB) • Other modes also developed, e.g., Counter Mode (CTR) • Can work with any symmetric block cipher as the underlying encryption algorithm • Many standard protocols, e.g., IPSec, allow the parties to select which block cipher to use
Cipher Block Modes Requirements • Efficiency – not much overhead over the block encryption • Robustness to chosen plaintext attacks where blocks can be set by attacker to reveal the key • Robustness to ciphertext attacks, to protect against selective modifications • Fault Tolerant to potential bit errors, not crashing or smashing the entire ciphertext/plaintext
Electronic CodeBook (ECB) Mode • Simplest form • Each block (e.g., 64 bits) encrypted separately • As if there is a codebook of 264 entries (per key) • Fast, easy to parallelize • Relatively fault tolerant • Easier target to known-plaintext attack • cryptanalyst can rebuild the code book • Susceptible to stereotypical parts of messages, statistical attacks • Also easier target to modification attack • E.g., replacing the target-account block in a bank money wiring communication
Cipher Block Chaining (CBC) Mode • Encryption • Ci=Ek(PiCi-1) • C0=IV • Decryption • Pi=Dk(Ci)Ci-1 • Initialization vector modifies encryption of identical block sequences • Can be chosen by source and sent in the clear (e.g. as C0) • Or, encrypt random data in the first block • Errors • A bit of error in the plaintext will not extend the error • A bit of error in the ciphertext will garble that block, and will alter same bit in the next block, but then CBC self-recovers completely • Security • A man-in-the-middle can easily append blocks in the end • Can change a bit, knowing which bit will be affected in 2nd block
Cipher Feedback Mode (CFB) IV E E E K K K K1 K2 Kn P1 P2 Pn … C1 C2 Cn • Errors • A bit of error in the plaintext affects all subsequent blocks but does not extend the error when decrypted • A bit of error in the ciphertext affects same bit and next block, after which CFB self synchronizes
Output Feedback Mode (OFB) • Repeatedly encrypt IV IV E E E K K K K1 K2 … Kn P1 P2 Pn C1 C2 Cn
Counter Mode (CTR) Counter+n-1 Counter Counter+1 • Advantages: • Parallelism • Random access to specific block • Requires only the encryption algorithm (advantageous when E and D have different algorithms, e.g. AES) E E E K K K K1 K2 Kn P1 P2 Pn … C1 C2 Cn
Summary • Application of block ciphers to arbitrary-sized messages • Encrypt one-block at a time • Prevent same encryption to same text through feed-forward mechanisms • Conceptually similar to avalanche • Fault tolerance to communication errors (flipped bits in ciphertext/plaintext)
Key Management Main sources: Network Security Essential / Stallings Applied Cryptography / Schneier
Key Generation, Distribution and Management • The security of any cryptographic system depends on safe and effective key distribution and management • frequent changes • low computational and communication overhead • Key Distribution Center (KDC) is a third-party that enables easier and more secure key management • KDC is single most critical point of failure • if KDC fails, many communication threads may fail • KDC is a good place to attack • Attacks on key generation algorithm • Attacks on key distribution through impersonation or communication hijacking • Attacks on KDC store or on human managers • Most common implementation is Kerberos
Key Generation • Key space should be large enough • Selection from key space shall be random • Humans select poor keys - prone to dictionary attack • Some algorithms have weak keys that should be avoided (DES has 16 such weak keys) • Example: ANSI X9.17 • Financial Institutions Key Generation Standard • Pseudo random key Ri generated from previous key, time stamp • Ri=3DESK(3DESK(Ti) Ri-1) • Ti is time stamp bits • It is recommended that seeds are generated from low-order bits of time stamps, or from time between keystrokes of administrator, etc.
Key Distribution Alternatives • Physical Delivery • Alice can select the key and deliver to Bob • Charles, a trusted third-party, can select the key and deliver to both Alice and Bob • Direct Delivery (encrypted) • From Alice to Bob, encrypted with a previous key, or using a master key • Encrypted communication with trusted third-party • From Charles to both Alice and Bob, and encrypted with host-KDC keys (master keys) that themselves may have been delivered physically
Key Distribution (cont.) • Choice of key distribution method depends also on network encryption needs • Link encryption • End-to-end encryption • Link encryption • Typically can use physical delivery, at least for master keys • End-to-end encryption • Physical delivery can be hard to implement • Peer-to-peer encryption of keys is dangerous (catch one, catch all) • Can use pre-set key, or a key generated concurrently by a token • Can also use keys delivered by third party (data keys) • Later we’ll see use of public key schemes
Session Key Distribution by KDC • It is safer if KDC-host connection uses physically delivered key • KDC-host communication shall also be mutually authenticated
Example: Ansi X9.17 • Financial Institution Key Management Standard • Defines protocol to be used by banks to transfer encryption keys • Defines a 3-level hierarchy of keys • Master key (KKM), distributed manually • Key-encrypting-keys (KKs), distributed online • Data Keys (KD), also online, encrypted using KKs • Encryption uses 3DES with one or two keys • Each pair of banks must share a master key • A new protocol, ANSI X9.28, was developed to cluster several banks around same master key • Standard has been augmented to use DH key distribution (public key)
Example: Kerberos • Common client/server access control protocol • Unix, Windows • Serves also as Key Distribution Center (KDC) • Uses “tickets” to allow access to servers • Ticket provides a “session” key T(c,s)=EKs(authinfo,Kc,s) Ticket Granting Server Grant Server Req Server Ticket Req Service Grant TGS Client Server Req TGS Ticket Kerberos Authentication Server (AS)
Review: Key Management Principles • To reduce the risk of eavesdropping • use different keys for different purposes • generate new keys from old ones using hash function • To reduce the risk of impersonation • use mutual authentication when exchanging keys • To reduce the risk of computer/physical break-in • store most keys encrypted using master key • save master keys in human memory, smart card, token, etc. • use tamper-proof hardware to store keys • destroy media on which keys were stored, even if were encrypted • Other principles: • Replace keys frequently • Report compromised keys to KDC with timestamp • Backup keys shall be broken and spread
Message Authentication Using Conventional Cryptography Main sources: Network Security Essential / Stallings Applied Cryptography / Schneier