Computer Vision Video Surveillance System
Computer Vision Video Surveillance System . Dr. Aree Ali Mohammed Assistant professor 2012-2013 3 rd Stage aree.ali@univsul.net. Presentation Overview. Video surveillance systems. Traffic monitoring issues. Object tracking techniques. Vehicle tracking strategies.

Computer Vision Video Surveillance System
E N D
Presentation Transcript
Computer VisionVideo Surveillance System Dr. Aree Ali Mohammed Assistant professor 2012-2013 3rd Stage aree.ali@univsul.net University of Sulaimani - School of Science - Computer Dept.
Presentation Overview • Video surveillance systems. • Traffic monitoring issues. • Object tracking techniques. • Vehicle tracking strategies. • A real time system Explanation.
Why Video Surveillance? • Improve public safety • Mitigate risks of crime and terrorism • Protect assets • Prevent fraud • Improve efficiency • Automate more processes • Train dispatch • Self-checking counters • Provide better healthcare
what is video surveillance? • Present Implementations? • Human detection systems. • vehicle monitoring systems. • Advantages of video surveillance? • Keep track of information video data for future use. • Helpful in identifying people in the crime scenes etc.. • Disadvantages of the present system? • It’s difficult to maintain heavy amount of raw video data • Human interaction. • Require higher bandwidth for transmitting the visual data.
Video Surveillance Addressable Market • Video surveillance application areas are myriad. Though their true scope remains almost unlimited, a few of the important areas of application are listed below: Monitoring process: traffic monitoring, border control Transport : Railways, airports and ports Government buildings : Museums and military bases Educational institutions: Distance learning, Telemedicine Energy: Oil & Gas, Utilities Public Security: Police/Fire/Ambulance CCTV: Closed Circuit Television Manufacturing: Production line quality management Leisure and entertainment areas: Stadiums Commercial units : Retail outlets, banks and casinos
Video Surveillance Applications: Forbidden Zone Alarm • Forbidden Zone protection • Intruder detection • Object tracing • Object detection of moving trail in open area
Video Surveillance Applications: Behavior Analysis Personal injury detection • Public responsibility • Elderly home care • Instant assistance and prevention Suspicious behavior detection • Loaf and run behavior • Custom behavior detection model
Video Surveillance Applications: Pedestrian and Traffic Flow Analysis Pedestrian flow management Traffic flow management • Allows threshold value to be set • Raises alarms when threshold is exceeded • Detects overcrowding/congestion • Assures public safety • Assures good traffic flow
Video Surveillance Applications: Night Video Night video surveillance assures public safety
Video Surveillance Applications: Others Identification by license plate or face Record by trigger event Extended services to consumers
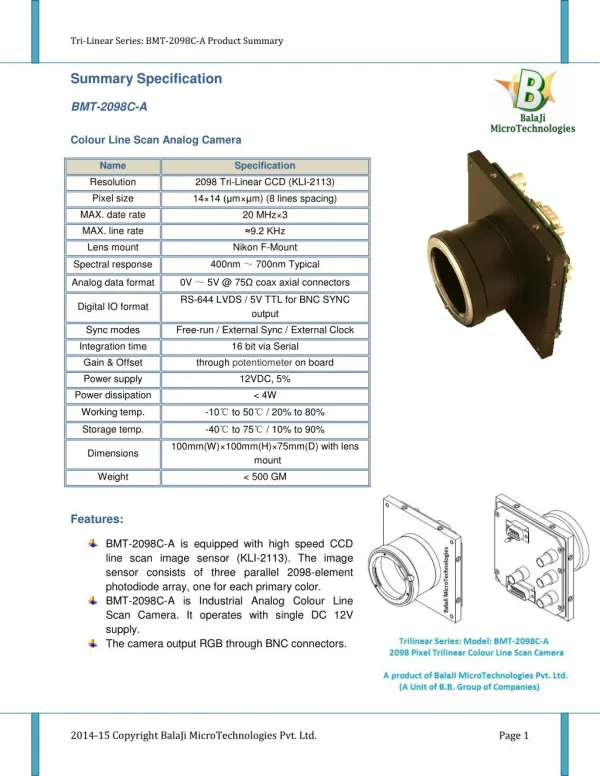
Video Surveillance Basics : System Components • Camera • Analog or IP • Fixed or PTZ (Pan, Tilt, Zoom) • Standard or High definition • Encoder • Typically consists of a modular analog to IP video converter • Supports different encoding formats • MJPEG, MPEG2, MPEG4 (part2), H.264 • DVR/NVR • Digital or Networked Video Recorder • Video Management System • Centralized, Distributed • Control Center • Display Wall • Storage • Network
Integrated Video Surveillance Solution - Network • Wire line • Broadband access: ADSL, VDSL, LAN • Leased line: G.SHDSL • Transmission: SONET,DWDM • Wireless • PTP: Microwave • Point to multi-point: LMDS • Wireless broadband access:WiMAX, WiFi • Switching/Routing • L2/L3, MPLS
Source Core Receiver Aggregation Receiver Access Source Video Surveillance Network • Has to be built for: • Operational flexibility • Scalability • Redundancy Should have: • Standards Compliancy • RAMS • Reliability • Availability • Maintainability • Safety
Video surveillance in the context of Computer Vision • Detection and tracking of moving objects are the important tasks of the computer vision. • The video surveillance systems not only need to track the moving objects but also interpret their patterns of behaviours. This means solving the information and integration the pattern. • Advantages • Minimizes the user interaction. • Less amount of prohibitive bandwidth. • Minimizes the cost and time.
Need for Traffic Monitoring • To reduce the traffic congestion on highways • Reduce the road accidents • Identifying suspicious vehicles. Etc..,
Traffic Monitoring in Computer Vision • The quest for better traffic information, an increasing reliance on traffic surveillance has resulted in a better vehicle detection. • Taking some intelligent actions based on the conditions. • Traffic scene analysis in 3 categories. • A strait forward vehicle detection and counting system . • Congestion monitoring and traffic scene analysis. • Vehicle classification and tracking systems which involve much more detailed scene traffic analysis.
Responsibilities of reliable Traffic Monitoring System • Adaptive to changes in the real world environments • Easy to set up • Capable of operating independently of human operators. • Capable of intelligent decisions. • Capable of monitoring multiple cameras and continuous operation. • Reasons for unsuccessful implementation**
Object Classification • Shape based classification. • Image blob area, blob bounding box • Classification based on above info. • Motion-based classification. • Human motion shows periodic property. • Time frequency analysis applied. • Residual flow taken under consideration.
Object tracking strategies (I)* • Background subtraction • Difference between the current image and the reference background image in a pixel by pixel fashion. • Sensitive to the background changes • Wallflower principles for effective background maintenance.
Object tracking strategies (II) • Temporal differencing • Moving objects changes intensity faster than static ones • Uses consecutive frames to identify the difference. • Adaptive to dynamic scene changes • Problems in extracting all relevant features. • Improved versions uses three frames instead of two
Object tracking strategies (III) • Optical flow • To identify characteristics of flow vectors of moving objects over time. • It’s used to detect independently moving objects in presence of camera. • Requires a specialized hardware to implement. Optical flow of moving objects Meyer et al
Vehicle detection techniques • Model based detection • Region based detection • Active contour based detection • Feature based detection
Vehicle detection technique (I) • Model based Tracking • The emphasis is on recovering trajectories and models with high accuracy for a small number of vehicles. • The most serious weakness of this approach is the reliance on detailed geometric object models. Disadvantage • It is unrealistic to expect detailed models for all vehicles that could be found on the roadway
Vehicle detection technique (II) • Region based tracking • It detects each vehicle blob using a cross correlation function. • Vehicle detection based on back ground subtraction. Disadvantage • Difficult to detect the vehicles under congested traffic, because vehicles partly occlude with one another Potential segmentation problem
Vehicle detection technique (III) • Active contour based detection • Tracking is based on active contour models, or snakes. • Representing object in bounding contour and keep updating it dynamically. • It reduced computational complexity compared to the region based detection. Disadvantage: • The inability to segment vehicles that are partially occluded remains a problem. Bounding counters
Vehicle detection technique (IV) • Feature based detection • Tracks sub-features such as distinguishable points or lines on the object • Effectiveness improved by the addition of common motion constraint. Features are grouped together based on common motion, avoiding segmentation problem due to occlusion
Wallflower Principles & Practice of Background Maintenance. • Foreground capture • Stopped car • Moving car • Shadows • Bootstrapping • Moved objects • Time of day • Light switch • Waving trees • camouflage
Wallflower: Three levels of abstraction • Pixel level • Maintains models of back ground of each individual pixel. • Processing makes the preliminary classification between foreground and background • Dynamic to scene changes. • Region level • Emphasis is on interrelationship between the pixels • Helps to refine raw classification at pixel level • Frame level • It watches for the sudden changes in the large parts of the image and swaps in alternative background models.
A real time traffic monitoring system Feature based tracking algorithm • Camera calibration • Feature detection • Vehicle tracking • Feature grouping Benjamin Coifman, Jitendra Malik, David Beymer
Offline camera definition • Line correspondences for a projective mapping. • A detection region near the image bottom and an exit region at the image top • And multiple fiducialpoints for camera calibration Based on the above information the system computes the homography between the image coordinates(x,y) and the world coordinates(X,Y)
On-line tracking and grouping • Detector • Detecting corners at the bottom of image, where brightness varies in more than one direction. • Detection operationalzed by the points in the image I • Tracker • Uses kalman filters to predict the velocity in the next image. • Normalized correlation is used to search the small region of image. • Group • Grouper uses common motion constraint. • Once all the corner features are identified they are grouped together. • Monitoring the distance between the point d(t)=P1(t)-p2(t)
2 Sample feature tracks from the tracker 1 3 Sample corner features identified by the tracker Sample feature groups from the tracker