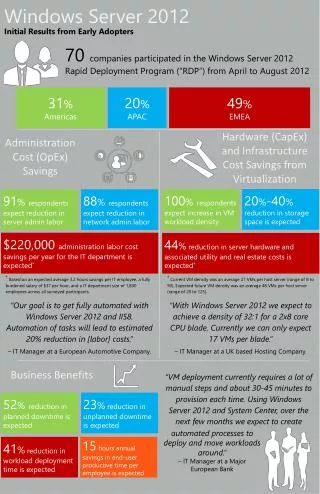
70-410 Installing & Configuring Windows Server 2012 R2
940 likes | 1.89k Vues
Windows Server 2012 installation options and configuration steps performed during installation and after deployment, in addition to using Windows PowerShell to perform common administrative tasks in Windows Server 2012.http://www.pass4sureexam.co/70-410.html

70-410 Installing & Configuring Windows Server 2012 R2
E N D
Presentation Transcript
Exam Prep70-411 Administering Windows Server 2012 Brian Svidergol http://www.pass4sureexam.co/70-410.html
What we’ll cover today Microsoft Certification Overview Study for Success http://www.pass4sureexam.co/70-410.html
Microsoft Certification Overview http://www.pass4sureexam.co/70-410.html
Microsoft Certifications Solution/cloud focus Microsoft Certified Solutions Master (MCSM) Microsoft Certified Solutions Expert (MCSE) Master Microsoft Certified Solutions Associate (MCSA) Expert Associate http://www.pass4sureexam.co/70-410.html
MCSE and MCSD certifications Desktop Infrastructure Private Cloud Server Infrastructure Web Applications SharePoint Data Platform SharePoint
MCSA: Windows Server 2012 411 412 410 EXAM EXAM EXAM Installing and Configuring Windows Server 2012 Administering Windows Server 2012 Configuring Advanced Windows Server 2012 Services MCSA: Windows Server 2012 + = + http://www.pass4sureexam.co/70-410.html
Upgrade paths Upgrading Your Skills to MCSA Windows Server 2012 • Any of the following certifications qualify: • MCSA: Windows Server 2008 • MCITP: Virtualization Administrator on Windows Server 2008 R2 • MCITP: Enterprise Messaging Administrator 2010 • MCITP: Lync Server Administrator 2010 • MCITP: SharePoint Administrator 2010 • MCITP: Enterprise Desktop Administrator on Windows 7 + + 70-417 http://www.pass4sureexam.co/70-410.html * Individuals that have earned the MCITP: Enterprise Administrator or MCITP: Server Administrator have also earned the MCSA: Windows Server 2008
Study for Success http://www.pass4sureexam.co/70-410.html
Topics covered on the exam Replace the Ns with your exam number to find your prep guide: http://www.microsoft.com/learning/en/us/exam.aspx?ID=70-NNN List of available languages Second tab shows Skills Measured. Third tab shows Preparation Materials, including a link to the Learning Plan for the exam.
Know What to Expect http://www.pass4sureexam.co/70-410.html
How to interpret the questions Business Problem All questions have a consistent anatomy Goal Statement One or Multiple Correct Answers Questions are not intended to trick you Multiple Distracters
Question types go beyond multiple choice Two Part Analysis Extending Matching items Extending Matching items Code Review Code Review Case Studies Case Studies Choose All That Apply Choose All That Apply Graphics Interpretation Best Answer Best Answer Active Screen Active Screen Drag & Drop Drag & Drop Multi-source Reasoning Build Lists Build Lists Be sure to view the exam item type demo before you take your first exam!
Deploy and Manage Server Images (1/2) Install the Windows Deployment Services (WDS) role Prerequisites: AD DS/DHCP/DNS/NTFS, member of Administrators Install-WindowsFeature –Name WDS -ComputerName Server01 –IncludeManagementTools (Servermanagercmd.exe deprecated) Boot, capture, install, discover images Boot image is Windows PE + client (boot.wim on media) Capture image is used to capture a reference computer to use for your install image Install image is what you deploy (install.wim on media) Discover image when computer can’t use PXE (boot to discover image media) Update images - patches/hotfixes/drivers/features DISM (ImageX, Package Manager, OCSetup- deprecated), 22 DISM cmdlets dism /online /enable-feature /FeatureName:TelnetClient
Deploy and Manage Server Images (2/2) Update images - patches/hotfixes/drivers/features Mount the offline image: DISM /Mount-Image /ImageFile:<path> /Name:<name> /MountDir:<temppath> Add package or driver to image: DISM /Image:<temppath> /Add-Package /PackagePath:<path> DISM /Image:<temppath> /Add-Driver /Driver:<path-to-INF> Commit the changes and unmount: DISM /Unmount-Image /MountDir:<temppath> /Commit http://www.pass4sureexam.co/70-410.html
Example question You have an existing image that you use to deploy to servers. You need to add a package to the image. What should you do first? A. Run the DISM /Image:<temppath> /Add-Package /PackagePath:<path> B. Run the DISM /Image:<temppath> /Add-Driver /Driver:<path-to-INF> C. Run the DISM /Mount-Image /ImageFile:<path> /Name:<name> /MountDir:<temppath> D. Run the DISM /Unmount-Image /MountDir<temppath> /Commit http://www.pass4sureexam.co/70-410.html
Implement Patch Management Install WSUS role DISM /Online /Enable-Feature /FeatureName: (dism /online /get-features) Install-WindowsFeature -Name UpdateServices -IncludeManagementTools GPOs, client side targeting Server-side targeting (default) – best in smaller deployments, make changes on the fly Client-side targeting (typically GPO) – best in large deployments, automated membership Watch for non-domain joined clients or the manual step of creating groups in WSUS Synchronization and WSUS groups Synchronization is where WSUS downloads updates from upstream server or Microsoft Update Watch for proxy server issue (configure in WSUS), firewall issue, or BITS issue WSUS groups – used for targeting updates to groups of computers Watch for client computers not showing up in the computer list (configure them for WSUS first)
Monitor Servers (1/2) Configure Data Collector Sets (DCS) 3 types of collectors – performance counters (system performance), event trace data (activities and system events), system configuration information (registry) Built in templates – Active Directory Diagnostics, Basic, System Diagnostics, System Performance, WDAC Diagnostics Alerts / Monitor Real-Time Performance Monitor performance counter then alert when threshold is exceeded Start a DCS, log event in Event Log, run a task (such as email or script) Monitor VMs Prerequisites: Windows Server 2012 Failover Cluster, Windows Server 2012 VMs, FW rule for VM Monitoring, enabled for monitoring Monitor services, restart service upon failure, reboot and/or move VM thereafter, automate, manual, or integrate with System Center
Monitor Servers (2/2) Monitor Events Centralize event log data to a single collector server (default protocol HTTP over port 5985) Use winrmquickconfig on source and wecutil qc on collector Works in non-domain environment but need to set TrustedHosts for WinRM Configure Event Subscriptions Use Event Viewer to create a subscription, default location is ForwardedEvents log Can use existing custom view (useful when trying to minimize administrative overhead) Configure Network Monitoring System Center Operations Manager + OS mgmt. packs + network device discovery Performance Monitor – DCS + performance monitor data + alert or log http://www.pass4sureexam.co/70-410.html
Example question You have a standalone Hyper-V host server running Windows Server 2012. You need to monitor the VMs that run Windows Server 2012. What should you do first? • Migrate the VMs to a Windows Server 2012 Failover Cluster. • Install Windows Server 2012 SP1 on the host server. • Install Windows Server 2012 SP1 on the VMs. • Join the host server to an Active Directory domain. http://www.pass4sureexam.co/70-410.html
Configure DFS(1/2) Overview DFS Replication and DFS Namespaces are role services (rolling up to File and Storage Services role) Know what’s new: PowerShell module, WMI mgmt., site awareness for DirectAccess, dedupe Know what’s deprecated: dfscmd, FRS Install and configure DFS Namespaces Domain-based namespace (can use multiple namespace servers, not Failover Clustering) For ABE and increased scalability – DFS Windows Server 2008 mode required: • The forest functional level must be Windows Server 2003 or higher • The domain functional level must be Windows Server 2008 or higher • All namespace servers must be running Windows Server 2008 or newer Stand-alone namespace (can be combined with Failover Clustering) Useful for non-AD DS environment Can scale to 50,000 folders (higher than Windows 2000 Server Mode which is ~5,000)
Configure DFS (2/2) Configure DFS Replication Targets Keep folders in sync, use the Replicate Folder wizard to configure Config changes must replicate via AD DS and then each namespace server must poll a DC for the config change (speed it up by forcing AD DS replication and then running the dfsrdiag.exe PollAD /Member:Contoso\Server01command) Configure Replication Scheduling Create replication group: • Multipurpose or data collection • Hub and spoke, full mesh, or no topology • Replicate continuously (select bandwidth limits if desired) • Replicate during specific days/times (can set bandwidth to use per time slot) Watch for staging folder size issues (if too small, high CPU or slow replication will result) Use a different physical disk for staging folder for improved I/O
Configure FSRM (1/2) Install FSRM Add-WindowsFeature FS-Resource-Manager -IncludeManagementTools Configure Quotas Configure quotas on specific folder or on a path (which handles newly created folders) Hard (users cannot exceed) or soft (users can exceed, used for monitoring) Built-in templates which can be used to create a quota or to create a new customized template When quota threshold met, option to send email, log event, run command, or generate report Be wary of deprecated tools such as dirquota.exe (instead use Set-FsrmQuota or similar) http://www.pass4sureexam.co/70-410.html
Configure FSRM (2/2) Configure File Screens Active screening (cannot save unauthorized files) Passive screening (can save unauthorized files, used for monitoring) Built-in templates (block audio/video files, e-mail files, executable files, images, monitor exe/system) Be wary of deprecated filescrn.exe Set-FsrmFileScreen, Set-FsrmFileScreenException, Set-FsrmFileScreenTemplate Configure Reports Run reports on demand – DHTML, HTML, XML, CSV, or text Built-in reports – duplicate files, file screen audit, files by file group, files by owner, files by property, folders by property, large files, least recently accessed files, most recently accessed files, quota usage Set scheduled reports and have reports emailed to admin(s)
Configure file and disk encryption (1/3) New Features BitLocker provisioning (can enable BitLocker prior to deploying Windows 8 via WinPE) Encrypt only used disk space (faster overall and takes only seconds for Windows 8 deployments) Change PIN and password by standard users (no longer require admin rights) Support for encrypted hard drives (encryption offloaded to the hard drive) Configure BitLocker encryption TPM version 1.2 or higher (required for provisioning prior to operating system deployment) TPM owner authorization – separate object new for Windows 8 – requires AD schema update Add BitLocker Drive Encryption feature, Enable-BitLocker (need volume/encryption method/key protector) http://www.pass4sureexam.co/70-410.html
Configure file and disk encryption (2/3) Configure the Network Unlock feature (new) Install the BitLocker Network Unlock feature, WDS on Windows Server 2012, separate DHCP, UEFI DHCP drivers, PKI for issuing certificate (or self-signed certificate), Group Policy configured For TPM+PIN systems, Network Unlock allows a form of two-factor authentication without user intervention when booting (on untrusted networks, TPM+PIN is used) Configure BitLocker policies (Win8 or Win2012) Choose drive encryption method and cipher strength Configure use of hardware-based encryption for *** drives (fixed/operating/removable) Enforce drive encryption type on *** drives – Full/Used only Allow network unlock at startup http://www.pass4sureexam.co/70-410.html
Configure file and disk encryption (3/3) Configure the EFS recovery agent Obtain a certificate for File Recovery for a data recovery agent user account Add data recovery agent (DRA) by editing GPO: Add from AD DS if certificated are published in AD DS (default not published) Add from .cer files if not published in AD DS Manage EFS and BitLocker certificates including backup and restore For certificates, can enable archiving on the certificate templates to allow recovery DRA can have a self-signed certificate which is backed up with standard backup methods Windows 7 requires permissions update to ms-TPM-OwnerInformationfor TPM owner info backup Back up BitLocker recovery info to AD DS GPO setting (Pre-2008 requires schema extension)
Example question You are the system administrator for Contoso, Ltd. You manage an Active Directory Domain Services (AD DS) domain. All servers run Windows Server 2008 R2. The forest functional level is set to Windows Server 2003. The domain functional level is set to Windows Server 2008. You are preparing to deploy DFS. The deployment must meet the following requirements. • Users must not be able to see folders that they do not have access to • Users must be able to create 3,000 total folders • Minimize changes to the environment You need to deploy DFS to meet the requirements. What should you do? • Update the forest functional level to Windows Server 2008 R2 and then deploy a standalone DFS namespace. • Update the forest functional level to Windows Server 2008 R2 and then deploy a domain-based DFS namespace by deselecting DFS Windows Server 2008 mode. • Deploy a standalone DFS namespace with Windows Server 2008 mode enabled. • Deploy a domain-based DFS namespace with Windows Server 2008 mode enabled.
Configure advanced audit policies (1/2) Implement auditing using Group Policy and AuditPol.exe Know difference between basic Audit Policy settings and advanced Audit Policy settings To manually enable Advanced Audit subcategory auditing (high overhead for widespread use): auditpol /set /subcategory:"RPC Events" /success:enable Auditpol has a /backup switch and a /restore switch Global object access auditing (for file system or registry – automatically applies to all objects) For Global auditing, watch for situations that don’t also enable Audit File System and Audit Registry audit policy settings (required) Advanced Audit Policy settings take precedence over basic Audit Policy settings http://www.pass4sureexam.co/70-410.html
Configure advanced audit policies (2/2) Create expression-based audit policies Audit anybody not in Payroll that tries to access the sensitive payroll spreadsheets (can be set directly on a file/folder or in global policy), can be combined with Dynamic Access Control Create removable device audit policies Requires Windows 8 or Windows Server 2012 Logs event when users attempt to access a removable storage device (Audit Removable Storage) Can also log removable storage device events (Audit Handle Manipulation) http://www.pass4sureexam.co/70-410.html
Configure DNS zones (1/2) Configure primary and secondary zones Primary zone can be stored in file or in AD DS – authoritative source for the zone Secondary zone cannot be stored in AD DS and is a read-only copy of a primary zone Configure stub zones Stub zone used to identify authoritative DNS servers for a zone – useful in a merger/acquisition Watch for scenarios that offer stub zone and conditional forwarding as potential solutions Stub zones best when needing to dynamically maintain authoritative DNS servers for child zone Configure conditional forwarders Forwards to specific DNS servers which can then build up a cache for efficient resolution Often the best solution for merger/acquisition but can also speed up internal name resolution http://www.pass4sureexam.co/70-410.html
Configure DNS zones (2/2) Configure zone and conditional forward storage in Active Directory DNS must be a domain controller, zone must be primary/stub/conditional Replication for integrated zones – all DNS + DCs in forest, all DNS + DCs in domain, all DCs in domain, all DCs in partition Configure zone delegation Key scenarios – delegate management, distribute load/improve perf/fault tolerance Configure zone transfer settings All servers, listed name servers, specific list – best security is specific list Configure notify settings Can notify name servers which helps secondary servers have more consistent DNS data
Configure DNS records (1/2) Create configure Resource Records (RR) including A, AAAA, PTR, SOA, NS, SRV, CNAME, and MX records Know that AAAA is IPv6 A record Use dnscmd /recordaddfor mass record creation (or PowerShell) Add-DnsServerResourceRecord-A -Name “test" -ZoneName "woodgrovebank.com" -IPv4Address 172.16.1.200 Configure zone scavenging Must enable at server level and at zone level (watch for troubleshooting scenarios or choose all) Must also be enabled at resource record level (by default it is, but watch for troubleshooting) Cleans up dynamic records only (not static) Avoid DNScmd.exe /ageallrecords
Configure DNS records (2/2) Configure record options including TTL and weight TTL default is 1 hour – can be updated at zone level or individual resource record level Weight default is 100 with a possible range of 0-65535 (higher means usually picked more) Configure round robin On and working by default, can disable with registry edit for certain resource record types HKLM\System\CurrentControlSet\Services\DNS\Parameters\DoNotRoundRobinTypes Local subnet priority takes precedence over round-robin for multi-homed names Configure secure dynamic updates Secure updates option only available when a zone is AD DS integrated Run dnscmd/Config woodgrovebank.com /AllowUpdate2 to force a zone to secure only
VPN and Routing Install and configure the Remote Access role • Add-WindowsFeatureRemoteAccess -IncludeManagementTools–IncludeAllSubFeature • Run the Configure and Enable Routing and Remote Access wizard Implement Network Address Translation (NAT) Need two interfaces prior to enabling via wizard Configure VPN settings For SSTP, need to select the proper SSL certificate post install Configure remote dial-in settings for users Default in AD is control access through NPS Network Policy Need to adjust policy or create new policy in order to allow users in Configure routing IPv4 and IPv6 static routes, DHCP relay, need to enable router for protocol
DirectAccess (1/2) Implement server requirements No longer require PKI (can use Kerberos proxy over HTTPS instead along with port 443) New simplified deployment but then won’t get force tunneling, Network Access Protection (NAP) integration, or two-factor authentication Can use a single NIC card behind NAT (Windows Server 2012 required) Remote access servers and all client computers must be domain members IPv6 not required and IPv6 transition technologies are used (however, IPv6 = best performance) Implement client configuration Need to have security groups in place and then create GPOs http://www.pass4sureexam.co/70-410.html
DirectAccess (2/2) Configure DNS for DirectAccess Name Resolution Policy Table (NRPT) – used to send specific queries to specific DNS servers (otherwise, use normal name resolution) – Windows 7 or later required (config via GPO) Configure certificates for DirectAccess If using internal CA or self-signed certificate, CRL distribution point must be available externally Can’t use self-signed cert in a multi-site environment Internal PKI is required if Kerberos proxy over HTTPS not available/possible http://www.pass4sureexam.co/70-410.html
Example question You are the system administrator for Tailspin Toys. You administer the Active Directory Domain Services (AD DS) environment along with DNS. Recently, another administrator added a new DNS Address (A) record for www2.tailspintoy.com. The record points to 10.10.5.254. Forward name resolution is fully functional. However, the web administrators are reporting that 10.10.5.254 is not resolving to www2.tailspintoys.com. You need to ensure that 10.10.5.254 resolves to www2.tailspintoys.com. What should you do? • Add a second Address (A) record for 10.10.5.254 and point it to www2.tailspintoys.com. • Add a second Address (AAAA) record for 10.10.5.254 and point it to www2.tailspintoys.com. • Add a PTR record for www2.tailspintoys.com and point it to 10.10.5.254. • Add a PTR record for 10.10.5.254 and point it to www2.tailspintoys.com. http://www.pass4sureexam.co/70-410.html
Configure NPS (1/2) Configure multiple RADIUS server infrastructures 5 parts – access clients (laptops), access servers (VPN/wirelessdevices), NPS servers (RADIUS server), NPS proxies (RADIUS proxy, faulttolerance by usingtwowith one being a backup, domainmembershipoptional, use NETSH to copy config from one proxy to another), user accountDBs (such as AD DS) Configure RADIUS clients Required: shared secret, friendlyname, FQDN or IP, optionalisvendor info (e.g. Cisco) Manage RADIUS templates Watch for questions involving administrative overhead as that may indicate the creation of a template or use of existing template. http://www.pass4sureexam.co/70-410.html
Configure NPS (2/2) Configure RADIUS accounting Can log to SQL DB, text file on local computer, bothsimultaneously, or SQL withtext file logging for failover (if SQL loggingfails, continue to log via text file) If logging stops (out of disk, SQL down), userscan’tget in (watchfor situations that call out default install and suddenloss of functionality– couldbe out of diskspace, considermovinglogging to non-system disk) Configure certificates Certificate-based auth - NPS servers need a server certificate Minimize administrative overhead in large environment – autoenrollment http://www.pass4sureexam.co/70-410.html