Device Management
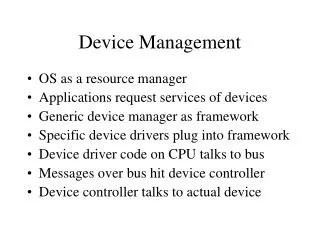
Device Management. Introduction. The operating system has an important role I managing the I/O operations.


Device Management
E N D
Presentation Transcript
Device Management www.eITnotes.com
Introduction • The operating system has an important role I managing the I/O operations. • Keeping track of the status of all devices, which requires special mechanisms. One commonly used mechanism is to have a database such as a Unit Control Block (UCB) associated with each device. • Deciding on policy to determine who gets a device, for how long, and when. A wide range of techniques is available for implementing theses polices. There are three basic techniques for implementing the policies of device management. www.eITnotes.com • Dedicated:- A technique whereby a device is assigned to a single process. • Shared:- A technique whereby a device is shared by many processors. • Virtual:- A technique whereby one physical device is simulated on another physical device..
Allocation:- Physical assigning a device to process. Likewise the corresponding control unit and • channel must be assigned. • De allocation policy and techniques. De allocation may be done on either process or a job. On a job level, a device is assigned for as long as the job exists in the system. On a process level, a device may be assigned for as long as the process needs it. • The module that keeps track of the status of device is called the I/O traffic controller. www.eITnotes.com
Introduction • I/O devices can be roughly grouped under three categories. • Human readable: Those devices that establish communication between computer and user. For example: Keyboard, mouse, printer etc • Machine readable: those devices that are suitable for communication with electronic equipment.. For example: disk, sensors, controllers etc… www.eITnotes.com • Communication: Those devices that are suitable for communication with remote devices. For example: Modems, routers, switches, etc…
Techniques for Device Management • Three major techniques are used to managing and allocating devices. • Dedicated Devices • Shared Devices • Virtual devices www.eITnotes.com
Dedicated Devices • A dedicated device is allocated to a job for the job’s entire duration. • Unfortunately, dedicated assignment may be inefficient if the job does not fully and continually utilize the device. • The other techniques, shared and virtual, are usually preferred whenever they are applicable. www.eITnotes.com
Shared Devices • Some devices such as disks, drums, and most other Direct Access Storage Devices (DASD) may be shared concurrently by several processes. • Several processes can read from a single disk at essentially at the same time. • The management of a shared device can become quite complicated, particularly if utmost efficiency is desired. For example, if two processes simultaneously request a read from Disk A, some mechanism must be employed to determine which request should be handled first. www.eITnotes.com
Virtual Devices • Some devices that would normally have to be dedicated may be converted into shared devices through techniques such as SPOOLING. (Simultaneous Peripheral Operation Online). • Spooling refers to a process of transferring data by placing it in a temporary working area where another program may access it for processing at a later point in time. • For example, a spooling program can read and copy all card input onto a disk at high speed. Later, when. A process tries to read a card, the spooling program intercepts the request and converts it to read from the Disk. www.eITnotes.com • Since a disk may be easily shared by several users, we have converted a dedicated device, changing one Card reader into many “virtual” card readers. This technique is equally applicable to a large number of Peripheral devices, such as printers and most dedicated slow input/output devices.