Tempest and Echelon
330 likes | 666 Vues
Tempest and Echelon. INTRODUCTION. Echelon Developed by National Security Agency of USA. A secret project to spy on people by tracing their messages. To find out the terrorist activities across the globe. The allies of USA in this project- UK, Australia, New Zealand and Canada.

Tempest and Echelon
E N D
Presentation Transcript
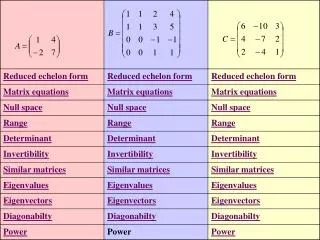
INTRODUCTION Echelon • Developed by National Security Agency of USA. • A secret project to spy on people by tracing their messages. • To find out the terrorist activities across the globe. • The allies of USA in this project- UK, Australia, New Zealand and Canada. • Developed with the highest computing power connected through the satellites all over the world. • Sniffing of messages over a network or any transmission media, even wireless.
INTRODUCTION (cont:) Tempest • Stands for “Transient Electro-Magnetic Pulse Emanation Standard”. • Main theory - Any electronic or electrical device emits electromagnetic radiations of specific key when it is operated. • Intercept electromagnetic waves over the air. • It even sniffs signals emanating from computer screens(range of few Kilometers). • Can detect keystrokes without network connection.
Inside TEMPEST • Refers to the study of compromising emanation. • Compromising Emanations(CE) are defined as unintentional intelligence-bearing signals. • CE consist of electrical or acoustical energy unintentionally emitted by a source • THE energy may relate to the original message , which leads to the recovery of plain text. • Can propagate through space and near by conductors.
Sources of TEMPEST • Functional Sources: • Incidental Sources:. Propagation of TEMPEST Signals • Electromagnetic Radiation • Line Conduction • Fortuitous Conduction • Acoustics
Technology Behind Tempest • Uses the electromagnetic waves propagated from the electronic devices intentionally or unintentionally. • It traces all electromagnetic radiation from the victim’s monitor, keyboard, even pc memory and hard disk, and then it reproduces the signals. • Enables the intruder to hack without any connection to the victim’s computer.
Technology Behind Tempest cont: • Snooping in to a computer’s VDU > Video display units output their frame buffer content periodically > Use character recognition techniques to give a better SNR • Snooping on CPUs • Execution of a known pattern of instructions • If signals caused by any instruction are lost in the noise, correlation techniques can be used.
Protection from TEMPEST • TEMPEST testing and selection of appropriate devices • TEMPEST Fonts • TEMPEST Proof walls
Tempest Testing And Selection • An equipment or system tested is called equipment under test (EUT). • An EUT can be visualized as an input/output box which receives an input signal and produces an output signal. The figure below shows this. Fig 2
Tempest Testing And Selection cont: • Because of design weaknesses, some unintentional signals may be generated in an EUT and emitted through space. • Such unintentional signals are the object of detection and measurement during TEMPEST tests. • Test types are of three, they are 1. Electric radiation test 2. Magnetic radiation test 3. Conduction test
TEMPEST FONTS • TEMPEST fonts are used for protecting the computers form the eavesdropper. • The software will filter that text and show that font as the most convenient way • The filtered text looks rather blurred and unpleasant in the magnified representation. • The loss in text quality is almost unnoticeable for the user at the computer screen
TEMPEST FONTS CONT: • The text on the left is displayed with a conventional • font. • Text on the right has been filtered to protect itself • from interception. • User can see practically no difference between the • fonts • Text disappears from the eavesdropping monitor True text Filtered text Fig 3
TEMPEST Proof Walls • TEMPEST proof walls are developed for preventing from TEMPEST attacks. • These walls are specially designed for reflecting the electromagnetic waves back to the same room it self. • TEMPEST –Proof walls are the most effective one
Inside ECHELON • Satellite photography • Electromagnetic signals(SIGINT) of any kind are intercepted and analysed • Radar stations, may provide valuable information about the organisation of enemy air defences • Monitoring other states, spy satellites is also useful
Interception On spot • Conversations: planted microphones (bugs) or laser equipment which picks up vibrations in window panes. • Screens emit radiation. • Telephone, fax, and e-mail messages can be intercepted if the eavesdropper taps into a cable leaving the relevant building. • Mobile phone can be intercepted if the interception station is situated in the same radio cell.
Scope for interception from aircraft and ships • AWACS aircraft are used for the purpose of locating other aircraft over long distances. • The slow-flying EP-3 spy plane used by the US Navy has the capability to intercept microwave and short-wave transmissions. • Submarines are used to intercept military radio transmissions.
The scope for interception by spy satellites (The Backbone of Echelon) • The satellites move in a complex elliptical orbit, to cover a larger area of the earth in one day. • The signals received are transmitted to the receiving station by means of a strongly-focused, 24GHz downlink.
The automatic analysis of intercepted communications • Use of Directories and Keywords. • Using the modern techniques for searching by use of the sophisticated speech recognition software and OCR software. • An echelon system can intercept about billions of messages every hour.
Keywords and ECHELON dictionaries • KEYWORD - “ Sensitive Words” to find out the messages which carries the sensitive information. • DICTIONARIES - The database containing the keywords • Each of these station dictionaries is given codeword
The Problems of Echelon:- • The Echelon system will not provide any privacy for our own people in home and abroad. • Every military secret is public to NSA and it’s allies, even though if we are hiding that from their eyes. • We have to ensure that these systems are protected from intrusion and if it occurs the result will be hazardous.
Conclusion • Tempest is the technology for spying from electronic equipments with out any physical contact. • Echelon is the vast network formed by NSA and its allies all over the world to intercept the messages sent through any transmission media. • Nothing can be hidden from the these systems. • Unfortunately our India does not have a Tempest equipment developed and we are not a part of Echelon network developed by NSA • We have to develop one such for empowering our intelligence agencies and military agencies.