Anomaly Detection in System Calls for Training Data
80 likes | 310 Vues
Explore the process of anomaly detection using system call sequence training data. Understand the normal system behavior and identify deviations for enhanced security measures.

Anomaly Detection in System Calls for Training Data
E N D
Presentation Transcript
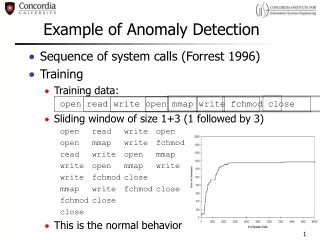
Example of Anomaly Detection • Sequence of system calls (Forrest 1996) • Training • Training data: open read write open mmap write fchmod close • Sliding window of size 1+3 (1 followed by 3) open read write open open mmap write fchmod read write open mmap write open mmap write write fchmod close mmap write fchmod close fchmod close close • This is the normal behavior
Example of Anomaly Detection • Detection open read write open open mmap write fchmod read write open mmap write open mmap write write fchmod close mmap write fchmod close fchmod close close • open read readopen mmap write fchmod close • Differs in 5 places: • Second read should be write (1st line) • Second read should be write (3rd line) • Second open should be write (3rd line) • mmap should be open (3rd line) • write should be mmap (3rd line) • 18 possible places of difference • 18=5*3+2+1 • Mismatch rate 5/18 28% ? A pre-defined threshold
Stack Frame c o d e r e t a d d r r e t a d d r 3 GB w/o Randomization b u f Exploit!
Stack Frame c o d e r e t a d d r r e t a d d r 3 GB w/ Randomization b u f b u f crash
Stack Frame c o d e r e t a d d r r e t a d d r De-Randomization 1 Pad b u f crash Step 1
Stack Frame c o d e r e t a d d r r e t a d d r De-Randomization 2 Pad b u f crash Step 2
Stack Frame c o d e r e t a d d r r e t a d d r De-Randomization 3 Pad b u f Exploit! 216 seconds (avg.) to de-randomize! Step 3 http://www.stanford.edu/~blp/papers/asrandom.pdf
c o d e Spraying Attacks • Exploit a buggy application and “spray” attack code in write-able user-level memory areas b u f Exploit!