Enhancing Identity Management in Cloud Services: Challenges and Strategies
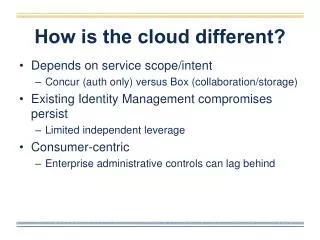
The difference in cloud services lies in their purpose and scope, like Concur's focus on authentication versus Box's collaboration features. Current identity management systems often fail to provide adequate independent leverage, prioritizing consumer needs while leaving enterprise controls lagging behind. To improve user management, institutions must adopt vendor-provided APIs and ensure automated de-provisioning of accounts. The goal is a campus-hosted system that empowers users with self-provisioning capabilities while maintaining security. Institutions should take charge of credential management, pushing vendors towards better solutions.

Enhancing Identity Management in Cloud Services: Challenges and Strategies
E N D
Presentation Transcript
How is the cloud different? • Depends on service scope/intent • Concur (auth only) versus Box (collaboration/storage) • Existing Identity Management compromises persist • Limited independent leverage • Consumer-centric • Enterprise administrative controls can lag behind
Identity In the Cloud? • Goal: • Campus-hosted system of record for entitled/active services • End-user self-provisioning for all services • Requires: • Vendor-provided user-management APIs • Disabling cloud-based identity management tools • Password change, account name change, etc. • Institution/cloud reconciliation • Automated de-provisioning of cloud accounts • Results in: • Institution is not dependent on cloud providers to know which services affiliates are provisioned for • Attestation capability
How Can You Help? • Spread the message: • Federated authentication • Institutions should manage credentials – not cloud providers • Continue to push vendors in this direction • Account Name does not equal Email Address • All our users have multiple institutional email addresses • We need role-based security • User-centric controls are insufficient for a managed service
Biggest Challenges • Identity Management compromises in favor of end-user features • Vendor maturity • Revoking campus credentials may not revoke access • Identity clean up for consumer-centric services • Affinities • No elegant solution for groups • Define the horizon