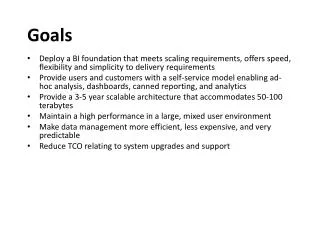
Goals
E N D
Presentation Transcript
Goals • Lay out some basic crypto concepts • Yes, there will be occasional formulas and details • Analyze their roles in some common protocols and applications • Roughly, the crypto architecture of the ‘Net • Become educated lay users of crypto implemented by trained professionals ™ • No, you shouldn’t try this at home :-) Crypto for IT Staff Mad-Sage
Non Goals • No proofs • Hardly any history • Skipping or simplifying many implementation details • Not a tutorial on the protocols & apps • Tonight’s focus is on the crypto • We won’t become either cryptographers (designers) or cryptanalysts (breakers) Crypto for IT Staff Mad-Sage
Outline • Warmup • Two cipher examples, tonight’s notations • 8 Cryptographic primitives • Block ciphers, public key algorithms, … • Decomposing applications and protocols • PGP, Certificates, TLS (SSL), SSH, IPSEC,… • Guidance • key lengths, snake oil, trust models, do’s and don’ts, … Crypto for IT Staff Mad-Sage
Warm up Introduction and Notation Crypto for IT Staff Mad-Sage
An (old) Cipher example M: I came, I saw, I conquered. C: L fdph, L vdz, L frqtxhuhg. • Start with a plaintext message (M), encrypt(via a monoalphabetic circular shift), obtaining obfuscated ciphertext(C). • Decrypt the ciphertext C back to plaintext M via the opposite shift • Very easily broken, via letter frequency statistics plus the word boundaries. Crypto for IT Staff Mad-Sage
A better (Renaissance) Cipher M: blaise is much harder K: HOLSTE IN BLAI SEISMU C: izlali qf nfcp zezvql • Depends on a secret key (holstein) • Incorporates feedback (autokey) • Ciphers the same letter differently • E.g. ‘h’ becomes p,z; ‘z’ comes from l,h,r • “a” is weak – it leaks plain and key text Crypto for IT Staff Mad-Sage
Notation – persons A is for Alice (sender, client) B is for Bob (receiver, server) V is for Victor (an eavesdropper / spy / bad guy / black hat) T is for Theresa (a trusted third party) Crypto for IT Staff Mad-Sage
Notation - crypto M = plaintext message (file, packet, …) C = encrypted ciphertext of M k, k1, k2, k3 = secret symmetric keys K{As} = Alice’s private (secret) key, K{Bp} = Bob’s public key E(k,M) = encrypt plaintext M via key k Using whatever algorithm we’re working with D(k,C) = decrypt ciphertext C via key k Crypto for IT Staff Mad-Sage
Notation - math p, q = large prime numbers xor = exclusive or 1 xor 1 = 0 mod = modular arithmetic 5 mod 3 = 2 ^ = exponentiation 2^(2^4) + 1 = 65537 || = string concatenation “a”||”b” = “ab” <> = vectors or lists <1,2,’sha1’> [ ] = text slice/block, { } = annotation Crypto for IT Staff Mad-Sage
8 cryptographic primitives (building blocks) Part One Crypto for IT Staff Mad-Sage
1: symmetric secret key block ciphers Symmetric A enciphers and B deciphers with the same key Secret Key The security depends only on how well A and B protect their shared key. Block works on chunks of message, usually 64 or 128 bits Cipher output size of gobbledegook ~ input size of message Crypto for IT Staff Mad-Sage
Block cipher design goals • Avalanche • 1 bit change in input flips 50% of output bits • Non-correlation • No input bit correlates with any output bit. No pair of input bits … No triple of input bits … • Full dependency • Each output bit depends on all input bits • Key dependent, with hardly any weak keys • No attacks easier than guessing for the key • 2^(N-1) tries are needed to break a single N-bit key Crypto for IT Staff Mad-Sage
How to make a block cipher • use multiple rounds of interleaved confusion (via substitution) and diffusion (via permutation) • Claude Shannon, c. 1945 • cryptographically strong • easy in either hardware or software • 1 byte table lookups do substitution • circular shifts with and/or/xor do permutation Crypto for IT Staff Mad-Sage
Commonly used block ciphers • RC2, 3DES, IDEA, CAST, AES, … • What our data are actually protected by • Pro: • Fast, Strong • Con: • Alice and Bob will need an out-of-band method for sharing a secret key Crypto for IT Staff Mad-Sage
DES – Data Encryption Standard • 64 bit blocks, 56 bit key, 16 S-P rounds • Details are complex; see FIPS 46-2 • The first good civilian block cipher to be widely used. • Proposed by IBM in 1972, modified by NSA, adopted by NIST in 1976. • Initially controversial. The NSA changed the S-boxes and reduced the key size. Civilian verdict after 30 years of cryptanalysis: actually, they improved it. • Brute forced (publicly): 1997. • NIST had finally put out an RFP seeking AES … • Unsafe: Moore’s Law has killed 56 bit keys! Crypto for IT Staff Mad-Sage
Safe variants of DES • DESX: E(k1, M xor k2) xor k3 • k2 and k3 provide pre- and post- whitening, like unix password salt. • net strength ~ 2^120; as fast as DES • Extensively used by Microsoft in Win2K • 3DES: E(k3, D(k2, E(k1, M))) • If k1=k2=k3, degenerates to DES • Often used with just two keys: k3=k1 • net strength ~ 2^112; sluggish but oddly popular Crypto for IT Staff Mad-Sage
Some 3DES cryptanalysis points • Due to a meet in the middle attack, 3DES only offers 2^112 resistance to an attacker with 2^56 dictionary temp space • Unknown if 3 keys is actually stronger than 2 • Due to the same attack, 2DES wouldn’t be enough stronger than 1DES • E-D-E resists the class of differentialattacks better than E-E-E Crypto for IT Staff Mad-Sage
3 more good block ciphers • IDEA: International Data Encryption Algorithm • 64 bit blocks, 128 bit key, 8 Rounds • But: patented until 2008, and the Swiss want royalties • CAST-128 • 64 bit blocks, 128 bit key, 16 rounds • RFC-2144; a good choice for interoperability • AES Advanced Encryption Standard (FIPS 197) • Belgian Rijndael cipher won the design competition • Block size is 128 bit, has 3 key size/round variations 128 bit / 10 rounds , 192 / 12, 256 / 14 Crypto for IT Staff Mad-Sage
2: block cipher usage modes • What if our message isn’t 64 bits? • Too short: pad, ideally with random bits • Too long: chop into multiple blocks • Do we want inter-block feedback? • Do we care about error propagation? • Military radios: yes. Computers: no. • 4-7 modes in common use • AES has 23 proposed modes … so far (See NIST SP 800-38a) Crypto for IT Staff Mad-Sage
Mode ECB: Electronic Code Book • Encrypt each block independently • Simplest mode, adds no space overhead • Not good for long messages • Victor knows that identical ciphertext came from identical plaintext, which reveals message structure • Victor can conduct known text attacks to build a code book • If Victor is a man in the middle, he can fiddle whole blocks undetected Crypto for IT Staff Mad-Sage
man in the middle attacks • Instead of Alice <-> Bob, we might have Alice <-> Victor <-> Bob • Some things Victor can do: • tell different lies to Alice than to Bob • pass their traffic, but record it • inject packets, or delete packets • change packet contents • replay packet streams • Lots of effort goes into preventing this! Crypto for IT Staff Mad-Sage
Mode CBC: Cipher Block Chaining • Start, block 0: xor a random initialization vector • Block worth of salt / whitening bits (64 bits for DES) • Unlike key, IV is not secret C[0] = E(k, M[0] xor IV) M[0] = D(k, C[0]) xor IV • Middle, blocks j: xor prior ciphertext C[j] = E(k, M[j] xor C[j-1]) M[j] = D(k, C[k]) xor C[j-1] • Option: end with a ciphertext stealing gimmick? • Details omitted. Off-line users have a cute ploy with the last two blocks which avoids trailing padding bits. Crypto for IT Staff Mad-Sage
3: Diffie – Hellman key exchange • An on-line protocol for Alice and Bob to generate a shared secret S • Widely used, e.g. in SSH, TLS, IPSEC • Depends on the difficulty of the discrete logarithm problem Computing z = g^w mod p is easy z = 2^4 mod 11 … z = 5 Inverse, finding w given z, g, p is hard 3 = 2^ w mod 11 … w = ? Crypto for IT Staff Mad-Sage
Diffie-Hellman details 1. start: large prime p, generator g, 1 < g < p. These can be public, and can be reused. 2. Alice: pick x, send A = g^x mod p picks a random x, computes A, sends <A,p,g> to Bob. X is secret, Message <A,p,g> is unencrypted. 3. Bob: pick y, send B = g^y mod p picks a random y, computes B , sends B to Alice. Y is also secret, B is again unencrypted. 4. Both: compute S = g ^ (x*y) mod p Alice: S=B^x mod p. Bob: S=A^y mod p. • Victor, eavesdropping on p,g,A,B, can’t find S Crypto for IT Staff Mad-Sage
4: Public Key: proposed Diffie & Hellman also analyzed the possibilities of asymmetric cryptosystems • Alice would use one key to encrypt, Bob would use a different key to decrypt. • allows key exchange and digital signature protocols • Needs a one way trapdoor function • Hard to invert, except when you possess an extra secret Crypto for IT Staff Mad-Sage
Public Key: realized • A flurry of candidates for one way trapdoor functions were proposed. Three survived: • Factoring, discrete logarithms, elliptic curves • It’s all number theory: modular exponentiation in finite fields and groups • But: they are all slow and weak • 1000x slower than block ciphers, or worse • Solutions much faster than key guessing exist • significantly vulnerable to known text attacks Crypto for IT Staff Mad-Sage
Public key: RSA (factoring) • Choose p, q large random primes. Let N=p*q • p and q are 350-2000 bits (10^155-10^600) • Choose e relatively prime to (p-1)*(q-1) • E can be reused; 65537 is popular. • Compute d = 1/e mod (p-1)*(q-1) • Private key is <d>. Public key is <N,e> • Alice discards p,q, or keeps them secret with d • Encrypt: C = M^e mod N • Decrypt: M = C^d mod N Crypto for IT Staff Mad-Sage
Pubkey: ElGamal (discrete log) • choose large random prime p, and random g, x less than p. Let y = g^x mod p. • private key is x; public key is <y, g, p> • encrypt: • choose new, previously unused random k, relatively prime to p-1. • let a = g^k mod p, b = ((y^k) * M) mod p. • Ciphertext: C = <a, b> • decrypt: M = b/(a^x) mod p Crypto for IT Staff Mad-Sage
Pubkey: Elliptic curves • Elliptic curve cryptography is based on the integer solutions to equations of the form: Y^2 = X^3 +a*X + b (coefficients a and b are from a finite field) • The trapdoor problem is scalar multiplication, g = s * f, for curves f,g • Not yet widely used; details omitted. • Appeal is shorter key sizes Crypto for IT Staff Mad-Sage
5: cryptographic hash functions • Also known as message digest algorithms • E.g. MD5, SHA-1, Haval, RIPEM-160, … • Design goals: • fast, fixed size output, one-way (exponential work to invert), strongly collision free, avalanche property, … • NB: CRC32 flunks all the crypto properties • Used for: identifying blob contents • messages, files, packets, PGP keys, … Crypto for IT Staff Mad-Sage
Two popular hashes • MD5: 128 bits (RFC 1321) • Derived from the RC4 stream cipher. • Don’t use it in new apps • SHA1: 160 bits (FIPS 180-1) • An NSA tweak of SHA, a stronger cousin of MD5 • Currently a good choice • hash size should be 2x block cipher key size. • due to a birthday attack, some breaks of an N-bit hash function average only 2^(N/2) operations • Yes, NIST will have longer ones to accompany AES. Crypto for IT Staff Mad-Sage
6: HMAC • Keyed hash based message authentication code (RFC 2104) • detects various man-in-the-middle attacks • Uses a shared secret key k, a hash algorithm H (twice), and special constants ipad, opad. • HMAC(k,H,M) = H((k xor opad) || H((k xor ipad) || M)) • Example from a TLS 1.0 packet: • HMAC(write_key, sha1, record_seq_no || C) • An alternative: last block from CBC-mode cipher Crypto for IT Staff Mad-Sage
7: Digital Signature Algorithms • Goal: validate Alice’s message to Bob • Authenticate sender • Prevent tampering • May provide non-repudiation • Tactic: encipher a message hash H via a public key algorithm. H=SHA1 is popular. • RSA example: (PGP, rfc2437, PKCS#1, X9.31) • Alice: send SIG = E(K{As}, H(M)) • Bob: compare H(M) =? D(K{Ap}, SIG) Crypto for IT Staff Mad-Sage
NIST DSA, slide 1 of 3: signing • Alice: create secret key x, public key <p,q,g,y> • p 512-1024 bit prime, q 160 bit prime factor of p-1 • Choose a random large x for secret key, with x < q • g = f^((p-1)/q) mod p, with f < p-1 such that g > 1 • y = g^x mod p • Using SHA-1 as H(), compute signature <r,s> • choose random k < q • Let r = (g^k mod p) mod q, s = ((H(M) + x*r)/k) mod q Crypto for IT Staff Mad-Sage
NIST DSA, 2 of 3: verifying Bob: obtain public DSA key of Alice: <p,q,g,y> Receive message M with signature <r,s> Compute: w = 1/s mod qu1 = (H(M) * w) mod q, u2 = (r*w) mod qv = ((g^u1 * y^u2) mod p) mod q If v=r, then Alice’s signature of M is valid Crypto for IT Staff Mad-Sage
NIST DSA, 3 of 3: comments • DSA annoyances • 1024 bit p / 160 bit q will soon be too small • Bob is doing more work than Alice • See FIPS 186-2 “Digital Signature Standard” (DSS) for 3 choices: • DSA (discrete logs) (FIPS 186) • X9.31 (an RSA variant) (FIPS 186-1) • Elliptic curves (FIPS 186-2) Crypto for IT Staff Mad-Sage
8: cryptographic pseudorandom number generating functions • A good CPRNG is very important. • You did notice how many “random” p,q,k,x,y,IV values we’ve been picking, right? • CPRNG problems are often the weakest link • Design goals: • can't invert, can't deduce seed, can't predict runs, no bit correlations, no weak seeds, … • Seed it with real entropy • Disk spindle speed wobbles, thermal noise Crypto for IT Staff Mad-Sage
Summary: crypto primitives • 5 basic primitives • Symmetric secret key block ciphers (3DES, AES, …) • Diffie-Hellman key exchange • Public key encryption (RSA, ElGamal, Elliptic) • Hash functions (MD5, SHA1, …) • Crypto psuedo random number generators • 3 more things we built from those: • Block cipher usage modes: ECB, CBC, … • HMAC (from hash + key + usage) • Digital signatures (from hash + public key) Crypto for IT Staff Mad-Sage
Decomposing Applications and Protocols Part two Crypto for IT Staff Mad-Sage
Signed, encrypted e-mail: PGP Alice sending e-mail M to Bob, with Bcc to self • Choose a signing algorithm (RSA), private/public key pair <K{As}, K{Ap}>, a block cipher (IDEA), a hash algorithm (SHA1), and a compression algorithm (ZLIB) • Seed CPRNG with entropy, set up block cipher. Generate: • a random 128 bit session key k • a random 64 bit initialization vector IV Crypto for IT Staff Mad-Sage
PGP e-mail: Alice to Bob (2 of 7) • Compute signature: hash message, encrypt (RSA) with Alice’s private key: SIG =E(K{As}, SHA1(M)) • Compress and encrypt M (idea/cbc mode) C = E(k, IV, zlib(M)) • Encrypt the session key with each recipients (Bob, Alice), RSA public key: E(K{Bp}, k) E(K{Ap}, k) Crypto for IT Staff Mad-Sage
PGP e-mail: Alice to Bob (3 of 7) • Assemble a multipart nested message: < <E(K{Bp}, k), E(K{Ap}, k)>, <‘idea’, IV, ‘zlib’, C>, <‘sha1’, SIG > > • ascii-encode the result, e-mail and archive it. Crypto for IT Staff Mad-Sage
PGP e-mail 4: Bob receiving • Bob locates his copy of the session key, decrypts it with his private RSA key: k = D{rsa}(K{Bs}, ...) • Bob decrypts ciphertext, decompresses it M = Expand( D{idea-cbc}(k, IV, C) ) • Bob checks the signature, using the hash algorithm and Alice’s public key K{Ap}: SHA1(M) =? D{rsa}(K{Ap}, SIG) Crypto for IT Staff Mad-Sage
PGP mail 5: primitive roles • Block cipher in CBC mode • Strong and fast: protects the message • CPRNG • session key, initialization vector, padding, … • Hash functions • Identification of message and key packets • Public key algorithms • distribute session key, sign message hash Crypto for IT Staff Mad-Sage
PGP mail 6: crypto remarks • Compressing plaintext improves strength • 100% of standards are naïve about signing • Signing cryptotext invites repudiation issues and is subject to Anderson’s attack. Don’t do it. • Signing plaintext really needs an IV for strength and a signed recipient name to detect forwarding • Public keys are slow, weak, and long-lived • Used only on small, random things: session keys and hashes Crypto for IT Staff Mad-Sage
PGP: v4 keys • Our example used v3 RSA Legacy keys • A single RSA key pair is used for both encryption and signing • Symmetric cipher is always IDEA • Newfangled version 4 keys are better: • separate encryption and signing key pairs • Rubber hose decryption attack: court order • Can use RSA/RSA or Elgamal/DSA (called DH/DSS) • Can use other block ciphers: CAST, 3DES, AES, … Crypto for IT Staff Mad-Sage
Interlude: Microsoft EFS • Tweak our our PGP example: • put Alice’s keys in a certificate • make Bob the file system recovery agent • let message M be a disk file • We'd be very near to Microsoft’s Encrypting File System • Win2K and XP use DESX as the cipher • Recent service packs added AES Crypto for IT Staff Mad-Sage
Passphrase protection (1 of 2) • Alice chooses a secret passphrase • 4-10 words, at least 20 chars, stuff • Run the encryption by: • Pick a random seed and cipher IV • K = HMAC(seed, SHA1, passphrase) • C = E{cbc}(K, IV, M) • Result is <seed, IV, C> • Securely erase M, K • Disk blocks, memory, swap space, file system slack space, … Crypto for IT Staff Mad-Sage
Passphrase protection (2 of 2) • Used by PGP, Tripwire, Digital Certificates to protect private keys • Other PGP uses: • file protection without public keys • broadcast e-mail (e.g. by FIRST) • Victor will try to brute force the passphrase • 20 characters of monocase English words is only 26 bits of entropy Crypto for IT Staff Mad-Sage
digital certificates: (1 of 4) • X.509 v3 / RFC 3280 (April 2002) • Roughly, a nested structure < blob, <algorithm, signature>>, with blob <version, serialNumber, algorithm, issuer, validity_period, subject_name, subject_public_key, …> • How you find them: Certificate: <issuer, serial_number> (Theresa) Subject: <subject_name, public_key> (Alice, Bob) Crypto for IT Staff Mad-Sage