Key Exchange: Part II
Key Exchange: Part II. ECE 498YH / CS 498YH: Computer Security. Slides borrowed/adapted from Matt Bishop. Midterm Timing. October 10 October 12 October 17 October 19 October 23. Summary of Last Lecture. Randomness of CBC output RSA for signing and verification Cryptographic checksums

Key Exchange: Part II
E N D
Presentation Transcript
Key Exchange: Part II ECE 498YH / CS 498YH: Computer Security Slides borrowed/adapted from Matt Bishop
Midterm Timing • October 10 • October 12 • October 17 • October 19 • October 23
Summary of Last Lecture • Randomness of CBC output • RSA for signing and verification • Cryptographic checksums • Key Exchange: • Simple exchange • Needham-Schroeder • Denning-Sacco • Otway-Rees (timestamps) (involve Bob)
Kerberos • Authentication system • Based on Needham-Schroeder with Denning-Sacco modification • Central server plays role of trusted third party (“Trent ”) • Ticket • Issuer vouches for identity of requester of service • Authenticator • Identifies sender Adapted from Matt Bishop
Idea • User u authenticates to Kerberos server • Obtains ticket Tu,TGS for ticket granting service (TGS) • User u wants to use service s: • User sends authenticator Au, ticket Tu,TGS to TGS asking for ticket for service • TGS sends ticket Tu,s to user • User sends Au, Tu,s to server as request to use s • Details follow Adapted from Matt Bishop
Ticket • Credential saying issuer has identified ticket requester • Example ticket issued to user u for service s Tu,s = s || { u || u’s address || valid time || ku,s } ks where: • ku,s is session key for user and service • Valid time is interval for which ticket valid • u’s address may be IP address or something else • Note: more fields, but not relevant here Adapted from Matt Bishop
Authenticator • Credential containing identity of sender of ticket • Used to confirm sender is entity to which ticket was issued • Example: authenticator user u generates for service s Au,s = { u || generation time || kt } ku,s where: • kt is alternate session key • Generation time is when authenticator generated • Note: more fields, not relevant here Adapted from Matt Bishop
Protocol user || TGS user Trent { ku,TGS } ku || Tu,TGS Trent user service || Au,TGS || Tu,TGS user TGS user || { ku,s } ku,TGS || Tu,s user TGS Au,s || Tu,s user service { t + 1 } ku,s user service Adapted from Matt Bishop
Analysis • First two steps get user ticket to use TGS • User u can obtain session key only if u knows key shared with Trent • Next four steps show how u gets and uses ticket for service s • Service s validates request by checking sender (using Au,s) is same as entity ticket issued to • Step 6 optional; used when u requests confirmation Adapted from Matt Bishop
Problems • Relies on synchronized clocks • If not synchronized and old tickets, authenticators not cached, replay is possible • Tickets have some fixed fields • Dictionary attacks possible • Kerberos 4 session keys weak (had much less than 56 bits of randomness); researchers at Purdue found them from tickets in minutes Adapted from Matt Bishop
Public Key Key Exchange • Here interchange keys known • eA, eB Alice and Bob’s public keys known to all • dA, dB Alice and Bob’s private keys known only to owner • Simple protocol • ks is desired session key { ks } eB Alice Bob Adapted from Matt Bishop
Problem and Solution • Vulnerable to forgery or replay • Because eB known to anyone, Bob has no assurance that Alice sent message • Simple fix uses Alice’s private key • ks is desired session key { { ks } dA } eB Alice Bob Adapted from Matt Bishop
Notes • Can include message enciphered with ks • Assumes Bob has Alice’s public key, and vice versa • If not, each must get it from public server • If keys not bound to identity of owner, attacker Eve can launch a man-in-the-middle attack (next slide; Trent is public server providing public keys) • Solution to this (binding identity to keys) discussed later as public key infrastructure (PKI) Adapted from Matt Bishop
Man-in-the-Middle Attack Eve intercepts request send Bob’s public key Alice Trent send Bob’s public key Trent Eve eB Trent Eve eE Eve Alice { ks } eE Eve intercepts message Bob Alice { ks } eB Bob Eve Adapted from Matt Bishop
Key Generation • Goal: generate keys that are difficult to guess • Problem statement: given a set of K potential keys, choose one randomly • Equivalent to selecting a random number between 0 and K–1 inclusive • Why is this hard: generating random numbers • Actually, numbers are usually pseudo-random, that is, generated by an algorithm Adapted from Matt Bishop
What is “Random”? • Sequence of cryptographically random numbers: a sequence of numbers n1, n2, … such that for any integer k > 0, an observer cannot predict nk even if all of n1, …, nk–1 are known • Best: physical source of randomness • Random pulses • Electromagnetic phenomena • Characteristics of computing environment such as disk latency • Ambient background noise Adapted from Matt Bishop
What is “Pseudorandom”? • Sequence of cryptographically pseudorandom numbers: sequence of numbers intended to simulate a sequence of cryptographically random numbers but generated by an algorithm • Very difficult to do this well • Linear congruential generators [nk = (ank–1 + b) mod n] broken • Polynomial congruential generators [nk = (ajnk–1j + … + a1nk–1 a0) mod n] broken too • Here, “broken” means next (or previous) number in sequence can be determined Adapted from Matt Bishop
Best Good Pseudorandom Numbers • Strong mixing function: function of 2 or more inputs with each bit of output depending on some nonlinear function of all input bits • Examples: DES, MD5, SHA-1 • Use on UNIX-based systems: (date; ps gaux) | md5 where “ps gaux” lists all information about all processes on system Adapted from Matt Bishop
Different Pseudorandom Numbers Blum Blum Shub PRNG: • Based on the hardness of factoring • Pick random primes p, q and random x0 • p,q should satisfy some properties • xn+1 = xn2 mod pq • Random number is the least-significant log log pqbits of xn • Can show that breaking this is as hard as factoring
Cryptographic Key Infrastructure • Goal: bind identity to key • Classical: not possible as all keys are shared • Use protocols to agree on a shared key (see earlier) • Public key: bind identity to public key • Crucial as people will use key to communicate with principal whose identity is bound to key • Erroneous binding means no secrecy between principals • Assume principal identified by an acceptable name Adapted from Matt Bishop
Certificates • Create token (message) containing • Identity of principal (here, Alice) • Corresponding public key • Timestamp (when issued) • Other information (perhaps identity of signer) signed by trusted authority (here, Trent ) CA = { eA || Alice || T } dC Adapted from Matt Bishop
Use • Bob gets Alice’s certificate • If he knows Trent ’s public key, he can decipher the certificate • When was certificate issued? • Is the principal Alice? • Now Bob has Alice’s public key • Problem: Bob needs Trent ’s public key to validate certificate • Problem pushed “up” a level • Two approaches: Merkle’s tree, signature chains Adapted from Matt Bishop
Merkle Hash Trees • Merkle Tree allows authentication of a collection of values given a single authentic value: Distribute root to all verifiers P = H(L || R) b’i = H(bi) bi
Merkle’s Tree Scheme • Keep certificates in a file • Changing any certificate changes the file • Use crypto hash functions to detect this • Define hashes recursively • h is hash function • Ci is certificate i • Hash of file (h(1,4) in example) known to all h(1,4) h(1,2) h(3,4) h(1,1) h(2,2) h(3,3) h(4,4) C1C2C3C4 Adapted from Matt Bishop
Validation • To validate C1: • Compute h(1, 1) • Obtain h(2, 2) • Compute h(1, 2) • Obtain h(3, 4) • Compute h(1,4) • Compare to known h(1, 4) • Need to know hashes of children of nodes on path that are not computed h(1,4) h(1,2) h(3,4) h(1,1) h(2,2) h(3,3) h(4,4) C1C2C3C4 Adapted from Matt Bishop
Details • f: DDD maps bit strings to bit strings • h: NND maps integers to bit strings • if i ≥ j, h(i, j) = f(Ci, Cj) • if i < j, h(i, j) = f(h(i, (i+j)/2),h((i+j)/2+1, j)) Adapted from Matt Bishop
Problem • File must be available for validation • Otherwise, can’t recompute hash at root of tree • Intermediate hashes would do • Not practical in most circumstances • Too many certificates and users • Users and certificates distributed over widely separated systems Adapted from Matt Bishop
Certificate Signature Chains • Create certificate • Generate hash of certificate • Encipher hash with issuer’s private key • Validate • Obtain issuer’s public key • Decipher enciphered hash • Recompute hash from certificate and compare • Problem: getting issuer’s public key Adapted from Matt Bishop
X.509 Chains • Some certificate components in X.509v3: • Version • Serial number • Signature algorithm identifier: hash algorithm • Issuer’s name; uniquely identifies issuer • Interval of validity • Subject’s name; uniquely identifies subject • Subject’s public key • Signature: enciphered hash Adapted from Matt Bishop
X.509 Certificate Validation • Obtain issuer’s public key • The one for the particular signature algorithm • Decipher signature • Gives hash of certificate • Recompute hash from certificate and compare • If they differ, there’s a problem • Check interval of validity • This confirms that certificate is current Adapted from Matt Bishop
Issuers • Certification Authority (CA): entity that issues certificates • Multiple issuers pose validation problem • Alice’s CA is Trent ; Bob’s CA is Don; how can Alice validate Bob’s certificate? • Have Trent and Don cross-certify • Each issues certificate for the other Adapted from Matt Bishop
Validation and Cross-Certifying • Certificates: • Trent <<Alice>> • Dan<<Bob> • Trent <<Dan>> • Dan<<Trent >> • Alice validates Bob’s certificate • Alice obtains Trent <<Dan>> • Alice uses (known) public key of Trent to validate Trent <<Dan>> • Alice uses Trent <<Dan>> to validate Dan<<Bob>> Adapted from Matt Bishop
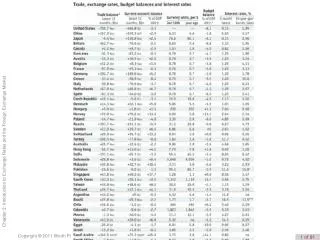
X.509 Certificates In Practice [AuthRoot\Certificates\74207441729CDD92EC7931D823108DC28192E2BB] [AuthRoot\Certificates\742C3192E607E424EB4549542BE1BBC53E6174E2] [AuthRoot\Certificates\7639C71847E151B5C7EA01C758FBF12ABA298F7A] [AuthRoot\Certificates\78E9DD0650624DB9CB36B50767F209B843BE15B3] [AuthRoot\Certificates\81968B3AEF1CDC70F5FA3269C292A3635BD123D3] [AuthRoot\Certificates\838E30F77FDD14AA385ED145009C0E2236494FAA] [AuthRoot\Certificates\85371CA6E550143DCE2803471BDE3A09E8F8770F] [AuthRoot\Certificates\85A408C09C193E5D51587DCDD61330FD8CDE37BF] [AuthRoot\Certificates\879F4BEE05DF98583BE360D633E70D3FFE9871AF] [AuthRoot\Certificates\8EB03FC3CF7BB292866268B751223DB5103405CB] [AuthRoot\Certificates\9078C5A28F9A4325C2A7C73813CDFE13C20F934E] [AuthRoot\Certificates\90AEA26985FF14804C434952ECE9608477AF556F] [AuthRoot\Certificates\90DEDE9E4C4E9F6FD88617579DD391BC65A68964] [AuthRoot\Certificates\96974CD6B663A7184526B1D648AD815CF51E801A] [AuthRoot\Certificates\97817950D81C9670CC34D809CF794431367EF474] [AuthRoot\Certificates\97E2E99636A547554F838FBA38B82E74F89A830A] [AuthRoot\Certificates\99A69BE61AFE886B4D2B82007CB854FC317E1539] [AuthRoot\Certificates\9BACF3B664EAC5A17BED08437C72E4ACDA12F7E7] [AuthRoot\Certificates\9E6CEB179185A29EC6060CA53E1974AF94AF59D4] [AuthRoot\Certificates\9FC796E8F8524F863AE1496D381242105F1B78F5] [AuthRoot\Certificates\A399F76F0CBF4C9DA55E4AC24E8960984B2905B6] [AuthRoot\Certificates\A3E31E20B2E46A328520472D0CDE9523E7260C6D] [AuthRoot\Certificates\A5EC73D48C34FCBEF1005AEB85843524BBFAB727] [AuthRoot\Certificates\AB48F333DB04ABB9C072DA5B0CC1D057F0369B46] [AuthRoot\Certificates\ACED5F6553FD25CE015F1F7A483B6A749F6178C6] [AuthRoot\Certificates\B172B1A56D95F91FE50287E14D37EA6A4463768A] [AuthRoot\Certificates\B19DD096DCD4E3E0FD676885505A672C438D4E9C] [AuthRoot\Certificates\B3EAC44776C9C81CEAF29D95B6CCA0081B67EC9D] [AuthRoot\Certificates\B5D303BF8682E152919D83F184ED05F1DCE5370C] [AuthRoot\Certificates\B6AF5BE5F878A00114C3D7FEF8C775C34CCD17B6] [AuthRoot\Certificates\B72FFF92D2CE43DE0A8D4C548C503726A81E2B93] [AuthRoot\Certificates\BC9219DDC98E14BF1A781F6E280B04C27F902712] [AuthRoot\Certificates\BE36A4562FB2EE05DBB3D32323ADF445084ED656] [AuthRoot\Certificates\CABB51672400588E6419F1D40878D0403AA20264] [AuthRoot\Certificates\CFDEFE102FDA05BBE4C78D2E4423589005B2571D] [AuthRoot\Certificates\CFF360F524CB20F1FEAD89006F7F586A285B2D5B] [AuthRoot\Certificates\CFF810FB2C4FFC0156BFE1E1FABCB418C68D31C5] [AuthRoot\Certificates\D23209AD23D314232174E40D7F9D62139786633A] [AuthRoot\Certificates\D29F6C98BEFC6D986521543EE8BE56CEBC288CF3] [AuthRoot\Certificates\D2EDF88B41B6FE01461D6E2834EC7C8F6C77721E] [AuthRoot\Certificates\DA40188B9189A3EDEEAEDA97FE2F9DF5B7D18A41] [AuthRoot\Certificates\DBAC3C7AA4254DA1AA5CAAD68468CB88EEDDEEA8] [AuthRoot\Certificates\E12DFB4B41D7D9C32B30514BAC1D81D8385E2D46] [AuthRoot\Certificates\E392512F0ACFF505DFF6DE067F7537E165EA574B] [AuthRoot\Certificates\E4554333CA390E128B8BF81D90B70F4002D1D6E9] [AuthRoot\Certificates\E5DF743CB601C49B9843DCAB8CE86A81109FE48E] [AuthRoot\Certificates\EBBC0E2D020CA69B222C2BFFD203CB8BF5A82766] [AuthRoot\Certificates\EC0C3716EA9EDFADD35DFBD55608E60A05D3CBF3] [AuthRoot\Certificates\EF2DACCBEABB682D32CE4ABD6CB90025236C07BC] [AuthRoot\Certificates\F44095C238AC73FC4F77BF8F98DF70F8F091BC52] [AuthRoot\Certificates\F88015D3F98479E1DA553D24FD42BA3F43886AEF] [AuthRoot\Certificates\0048F8D37B153F6EA2798C323EF4F318A5624A9E] [AuthRoot\Certificates\00EA522C8A9C06AA3ECCE0B4FA6CDC21D92E8099] [AuthRoot\Certificates\0483ED3399AC3608058722EDBC5E4600E3BEF9D7] [AuthRoot\Certificates\049811056AFE9FD0F5BE01685AACE6A5D1C4454C] [AuthRoot\Certificates\0B77BEBBCB7AA24705DECC0FBD6A02FC7ABD9B52] [AuthRoot\Certificates\1331F48A5DA8E01DAACA1BB0C17044ACFEF755BB] [AuthRoot\Certificates\1F55E8839BAC30728BE7108EDE7B0BB0D3298224] [AuthRoot\Certificates\209900B63D955728140CD13622D8C687A4EB0085] [AuthRoot\Certificates\216B2A29E62A00CE820146D8244141B92511B279] [AuthRoot\Certificates\23E594945195F2414803B4D564D2A3A3F5D88B8C] [AuthRoot\Certificates\24A40A1F573643A67F0A4B0749F6A22BF28ABB6B] [AuthRoot\Certificates\24BA6D6C8A5B5837A48DB5FAE919EA675C94D217] [AuthRoot\Certificates\273EE12457FDC4F90C55E82B56167F62F532E547] [AuthRoot\Certificates\284F55C41A1A7A3F8328D4C262FB376ED6096F24] [AuthRoot\Certificates\2F173F7DE99667AFA57AF80AA2D1B12FAC830338] [AuthRoot\Certificates\317A2AD07F2B335EF5A1C34E4B57E8B7D8F1FCA6] [AuthRoot\Certificates\36863563FD5128C7BEA6F005CFE9B43668086CCE] [AuthRoot\Certificates\394FF6850B06BE52E51856CC10E180E882B385CC] [AuthRoot\Certificates\3F85F2BB4A62B0B58BE1614ABB0D4631B4BEF8BA] [AuthRoot\Certificates\4072BA31FEC351438480F62E6CB95508461EAB2F] [AuthRoot\Certificates\40E78C1D523D1CD9954FAC1A1AB3BD3CBAA15BFC] [AuthRoot\Certificates\43DDB1FFF3B49B73831407F6BC8B975023D07C50] [AuthRoot\Certificates\43F9B110D5BAFD48225231B0D0082B372FEF9A54] [AuthRoot\Certificates\4463C531D7CCC1006794612BB656D3BF8257846F] [AuthRoot\Certificates\47AFB915CDA26D82467B97FA42914468726138DD] [AuthRoot\Certificates\4B421F7515F6AE8A6ECEF97F6982A400A4D9224E] [AuthRoot\Certificates\4BA7B9DDD68788E12FF852E1A024204BF286A8F6] [AuthRoot\Certificates\4C95A9902ABE0777CED18D6ACCC3372D2748381E] [AuthRoot\Certificates\4EF2E6670AC9B5091FE06BE0E5483EAAD6BA32D9] [AuthRoot\Certificates\4EFCED9C6BDD0C985CA3C7D253063C5BE6FC620C] [AuthRoot\Certificates\4F65566336DB6598581D584A596C87934D5F2AB4] [AuthRoot\Certificates\54F9C163759F19045121A319F64C2D0555B7E073] [AuthRoot\Certificates\58119F0E128287EA50FDD987456F4F78DCFAD6D4] [AuthRoot\Certificates\5B4E0EC28EBD8292A51782241281AD9FEEDD4E4C] [AuthRoot\Certificates\5D989CDB159611365165641B560FDBEA2AC23EF1] [AuthRoot\Certificates\5E5A168867BFFF00987D0B1DC2AB466C4264F956] [AuthRoot\Certificates\5E997CA5945AAB75FFD14804A974BF2AE1DFE7E1] [AuthRoot\Certificates\627F8D7827656399D27D7F9044C9FEB3F33EFA9A] [AuthRoot\Certificates\6372C49DA9FFF051B8B5C7D4E5AAE30384024B9C] [AuthRoot\Certificates\6782AAE0EDEEE21A5839D3C0CD14680A4F60142A] [AuthRoot\Certificates\67EB337B684CEB0EC2B0760AB488278CDD9597DD] [AuthRoot\Certificates\687EC17E0602E3CD3F7DFBD7E28D57A0199A3F44] [AuthRoot\Certificates\688B6EB807E8EDA5C7B17C4393D0795F0FAE155F] [AuthRoot\Certificates\68ED18B309CD5291C0D3357C1D1141BF883866B1] [AuthRoot\Certificates\69BD8CF49CD300FB592E1793CA556AF3ECAA35FB] [AuthRoot\Certificates\6A174570A916FBE84453EED3D070A1D8DA442829] [AuthRoot\Certificates\720FC15DDC27D456D098FABF3CDD78D31EF5A8DA] [AuthRoot\Certificates\7A74410FB0CD5C972A364B71BF031D88A6510E9E] [AuthRoot\Certificates\7AC5FFF8DCBC5583176877073BF751735E9BD358] [AuthRoot\Certificates\7CA04FD8064C1CAA32A37AA94375038E8DF8DDC0] [AuthRoot\Certificates\7E784A101C8265CC2DE1F16D47B440CAD90A1945] [CA\Certificates\063DA67748F0ECCC690D319BCDCD0E72AC8D48D5] [CA\Certificates\109F1CAED645BB78B3EA2B94C0697C740733031C] [CA\Certificates\12519AE9CD777A560184F1FBD54215222E95E71F] [CA\Certificates\189271E573FED295A8C130EAF357A20C4A9F115E] [CA\Certificates\2D69A20EC4F0CD19037FD6D6246B1EE0EC41BA22] [CA\Certificates\7B02312BACC59EC388FEAE12FD277F6A9FB4FAC1] [CA\Certificates\8B24CD8D8B58C6DA72ACE097C7B1E3CEA4DC3DC6] [CA\Certificates\9F025D9F58711A605EB0694B0E8BC0CA4F25FD6F] [CA\Certificates\BA9E3C32562A67128CAABD4AB0C500BEE1D0C256] [CA\Certificates\E5215D3460C2C20BBE2D9FE5FB665DAA2C0E225C] [CA\Certificates\F6357239B7C39725BD8000646E4A0D18EBCE4CFA] [CA\Certificates\FE622EA7B33CA46519AB39736A66B8F6E41FF157] [CA\Certificates\FEE449EE0E3965A5246F000E87FDE2A065FD89D4] • Who do you trust as a CA? [ROOT\Certificates\18F7C1FCC3090203FD5BAA2F861A754976C8DD25] [ROOT\Certificates\245C97DF7514E7CF2DF8BE72AE957B9E04741E85] [ROOT\Certificates\74CDD21C2F1D104F8940DFFE7E6F035756E2F5D0] [ROOT\Certificates\7F88CD7223F3C813818C994614A89C99FA3B5247] [ROOT\Certificates\A43489159A520F0D93D032CCAF37E7FE20A8B419] [ROOT\Certificates\CDD4EEAE6000AC7F40C3802C171E30148030C072]
PGP Chains • OpenPGP certificates structured into packets • One public key packet • Zero or more signature packets • Public key packet: • Version (3 or 4; 3 compatible with all versions of PGP, 4 not compatible with older versions of PGP) • Creation time • Validity period (not present in version 3) • Public key algorithm, associated parameters • Public key Adapted from Matt Bishop
OpenPGP Signature Packet • Version 3 signature packet • Version (3) • Signature type (level of trust) • Creation time (when next fields hashed) • Signer’s key identifier (identifies key to encipher hash) • Public key algorithm (used to encipher hash) • Hash algorithm • Part of signed hash (used for quick check) • Signature (enciphered hash) • Version 4 packet more complex Adapted from Matt Bishop
Signing • Single certificate may have multiple signatures • Notion of “trust” embedded in each signature • Range from “untrusted” to “ultimate trust” • Signer defines meaning of trust level (no standards!) • All version 4 keys signed by subject • Called “self-signing” Adapted from Matt Bishop
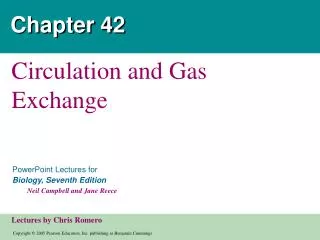
Validating Certificates • Alice needs to validate Bob’s OpenPGP cert • Does not know Fred, Giselle, or Ellen • Alice gets Giselle’s cert • Knows Henry slightly, but his signature is at “casual” level of trust • Alice gets Ellen’s cert • Knows Jack, so uses his cert to validate Ellen’s, then hers to validate Bob’s Arrows show signatures Self signatures not shown Jack Henry Ellen Irene Giselle Fred Bob Adapted from Matt Bishop
Storing Keys • Multi-user or networked systems: attackers may defeat access control mechanisms • Encipher file containing key • Attacker can monitor keystrokes to decipher files • Key will be resident in memory that attacker may be able to read • Use physical devices like “smart card” • Key never enters system • Card can be stolen, so have 2 devices combine bits to make single key Adapted from Matt Bishop
Key Escrow • Key escrow system allows authorized third party to recover key • Useful when keys belong to roles, such as system operator, rather than individuals • Business: recovery of backup keys • Law enforcement: recovery of keys that authorized parties require access to • Goal: provide this without weakening cryptosystem • Very controversial Adapted from Matt Bishop
Desirable Properties • Escrow system should not depend on encipherment algorithm • Privacy protection mechanisms must work from end to end and be part of user interface • Requirements must map to key exchange protocol • System supporting key escrow must require all parties to authenticate themselves • If message to be observable for limited time, key escrow system must ensure keys valid for that period of time only Adapted from Matt Bishop
Components • User security component • Does the encipherment, decipherment • Supports the key escrow component • Key escrow component • Manages storage, use of data recovery keys • Data recovery component • Does key recovery Adapted from Matt Bishop
Example: ESS, Clipper Chip • Escrow Encryption Standard • Set of interlocking components • Designed to balance need for law enforcement access to enciphered traffic with citizens’ right to privacy • Clipper chip prepares per-message escrow information • Each chip numbered uniquely by UID • Special facility programs chip • Key Escrow Decrypt Processor (KEDP) • Available to agencies authorized to read messages Adapted from Matt Bishop
User Security Component • Unique device key kunique • Non-unique family key kfamily • Cipher is Skipjack • Classical cipher: 80 bit key, 64 bit input, output blocks • Generates Law Enforcement Access Field (LEAF) of 128 bits: • { UID || { ksession } kunique || hash } kfamily • hash: 16 bit authenticator from session key and initialization vector Adapted from Matt Bishop
Programming User Components • Done in a secure facility • Two escrow agencies needed • Agents from each present • Each supplies a random seed and key number • Family key components combined to get kfamily • Key numbers combined to make key component enciphering key kcomp • Random seeds mixed with other data to produce sequence of unique keys kunique • Each chip imprinted with UID, kunique, kfamily Adapted from Matt Bishop
The Escrow Components • During initialization of user security component, process creates ku1 and ku2 where kunique = ku1ku2 • First escrow agency gets { ku1 } kcomp • Second escrow agency gets { ku2 } kcomp Adapted from Matt Bishop
Obtaining Access • Alice obtains legal authorization to read message • She runs message LEAF through KEDP • LEAF is { UID || { ksession } kunique || hash } kfamily • KEDP uses (known) kfamily to validate LEAF, obtain sending device’s UID • Authorization, LEAF taken to escrow agencies Adapted from Matt Bishop
Agencies’ Role • Each validates authorization • Each supplies { kui } kcomp, corresponding key number • KEDP takes these and LEAF: • Key numbers produce kcomp • kcomp produces ku1 and ku2 • ku1 and ku2 produce kunique • kunique and LEAF produce ksession Adapted from Matt Bishop
Problems • hash too short • LEAF 128 bits, so given a hash: • 2112 LEAFs show this as a valid hash • 1 has actual session key, UID • Takes about 42 minutes to generate a LEAF with a valid hash but meaningless session key and UID • Turns out deployed devices would prevent this attack • Scheme does not meet temporal requirement • As kunique fixed for each unit, once message is read, any future messages can be read Adapted from Matt Bishop
Yaksha Security System • Key escrow system meeting all 5 criteria • Based on RSA, central server • Central server (Yaksha server) generates session key • Each user has 2 private keys • Alice’s modulus nA, public key eA • First private key dAA known only to Alice • Second private key dAY known only to Yaksha central server • dAAdAY = dA mod (nA) Adapted from Matt Bishop
Alice and Bob • Alice wants to send message to Bob • Alice asks Yaksha server for session key • Yaksha server generates ksession • Yaksha server sends Alice the key as: CA = (ksession)dAYeA mod nA • Alice computes (CA)dAA mod nA = ksession Adapted from Matt Bishop