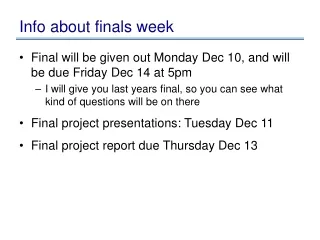
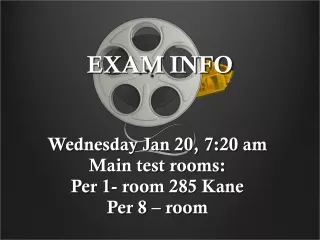
Info about exam
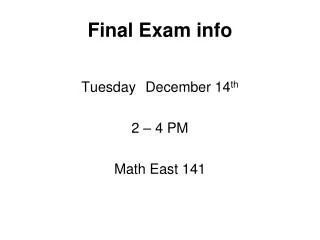
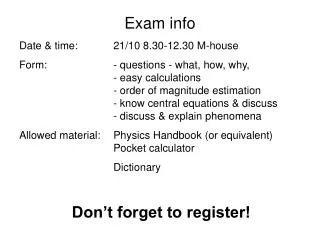
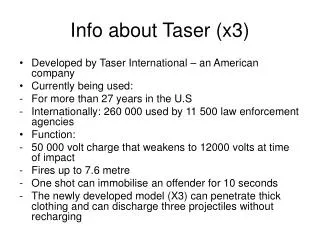
Info about exam. Exam dates. Exam period sat 8.5. - fri 21.5.2010 1st exam , date ? Second exam in August 2010 ( before semester starts ) Third exam in October 2010 Fourth exam in December 2010 Any idea when you want to take the exam ? These are open book exams .

Info about exam
E N D
Presentation Transcript
Examdates • Examperiodsat 8.5. - fri 21.5.2010 • 1st exam, date? • Secondexam in August 2010 (beforesemesterstarts) • Thirdexam in October 2010 • Fourthexam in December 2010 • Any idea whenyouwant to take the exam? Theseareopenbookexams. • Coursematerial, articles, anythingyouwant to bringwithyou. • Ifyoupassed the assignments, youonlyneed to read the first set of articles. • Ifyoudidn’tpass the assignments, youneed to readbothsets of articles.
Examarticles Lectureslides + Ifassignmentspassed, also: • Adams and Sasse: Usersarenot the enemy • Good and Krekelberg: Usability and privacy: a study of Kazaa P2P file-sharing • Tygar and Whitten: Why Johnny Can’tEncrypt • Cranor et al: Beyond Concern: Understanding Net Users' Attitudes About Online Privacy • Cheskin: eCommerceTrustStudy • Nielsen: TrustorBust: CommunicatingTrustworthiness in Web Design • Norman: WhenSecurityGets in the Way • Schehter et al: The Emperor's New Security Indicators Ifassignmentsnotpassed, on top of the abovelist of articles, also: • Smetters and Good: How Users Use Access Control • Ackerman et al: Privacy Issues and Human-Computer Interaction • Dhamija: Why Phishing Works • Chiasson et al: A Second Look at the Usability of Click-Based Graphical Passwords. Symposium On Usable Privacy and Security • Camp: Mental models of privacy and security • Lindgaard: Attention Web Designers: Youhave 50 milliseconds to make a goodfirst impression!