Verifiable Databases and RAM Programs
Verifiable Databases and RAM Programs. Yupeng Zhang , Daniel Genkin , Jonathan Katz, Dimitrios Papadopoulos and Charalampos Papamanthou. Cloud Computing. Universities. Companies. Individuals. Security Issue: Integrity. Universities. Server failure Software error


Verifiable Databases and RAM Programs
E N D
Presentation Transcript
Verifiable Databases and RAM Programs Yupeng Zhang, Daniel Genkin, Jonathan Katz, Dimitrios Papadopoulos and CharalamposPapamanthou
Cloud Computing Universities Companies Individuals
Security Issue: Integrity Universities Server failure Software error Data tampering in transmission Random answer Malicious server behavior … Companies Individuals
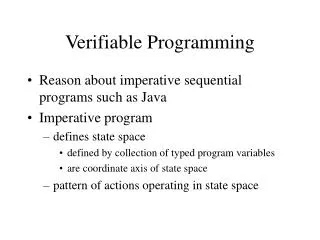
Agenda • Background on verifiable computation • Our construction • Applications to Verifiable Databases and RAM Programs
Verifiable Computation client server function result + proof digest δ Verification: or data
Efficiency Measures of Verifiable Computation setup time prover time client server function result + proof digest δ Verification: or proof size data verification time
Prior Work in Verifiable Computation 1. Customized Approach • File read and write [Merkle87, NN00, …] • Range search [Tamassia03, GPT07, …] • Set operations [PTT11, CPPT14, KPP+14, …] • Graph algorithms [GTTC03, ZPK14, Grob14, …] • Database queries [ZKP15, …] • Efficient • Only support limited operations Expressiveness databse graph sets range read/write Efficiency
Prior Work in Verifiable Databases 2. Generic Approach (E.g., SNARK[PHGR13, BCGTV13, BFRS+13, BISW17, …]) • Supports all functions that can be modeled as arithmetic circuits • Constant proof size, fast verification time • Large setup time & prover time • Function specific setup Expressiveness SNARK databse graph sets range read/write Efficiency
Our Contribution • Supports arbitrary computations in NP • Up to 2 orders of magnitude faster than SNARKs • Comparable efficiency to customized VC for databases • No function specific setup Expressiveness Our argument system SNARK databse graph sets range read/write Efficiency
Interactive Proof (IP)[GKR08, CMT12, …] Example: polynomial expansion server client Expand f(x) for me • g(x) = 6x3+49x2+128x+105 Polynomial f(x) = (x+3)(3x+5)(2x+7) If f(x) - g(x) ≠ 0, but f(r) - g(r) = 0, →r is a root of f(x) - g(x), →Pr[r is a root] = • pick a random value r, test f(r) - g(r) = 0
Interactive Proof (IP)[GKR08, CMT12, …] Input Output (result) server client Output fout(x) fout(rout) …… r1 × × f1(x) f1(r1) …… × + × f2(x) …… rin …… fd-2(x) fin(rin) …… …… × × + fd-1(x) …… + × + fin(x) = a0+a1x+a2x2+… (Low degree extension) Check the relationship at a random point (Sumcheck protocol) a0 a1 a2 a3 …… Input (data) fin(rin)
Using IP for Verifiable Computation • No setup time • Fast prover time (no crypto operations) • Storage of the data locally (Last step: evaluate a polynomial defined by the input at a random point)
Delegating Data to the Server • Our solution: Verifiable Polynomial Delegation (VPD) [KZG10, PST13] server evaluation point a client f(a) + proof digest δf (32Bytes) Verification: or f(x)
Our Interactive Argument Protocol function (modeled as a circuit) server client result IP … digest δfin of fin(x) for the data Interactive proof (except last step) data … fin(rin) VPD rin • fin(rin) + proof fin(rin) or Verification of polynomial delegation
Using IP for Verifiable Databases • No setup time • Fast prover time (no crypto operations) • Storage of the data locally (Last step: evaluate a polynomial defined by the input at a random point)
Supporting Auxiliary Inputs from Server • Some functions are hard to compute using arithmetic circuits E.g., Integer division a÷b • They are easy to verify with inputs from the server: a = q × b + r • Functions in NP • Interactive Proof does not support auxiliary input (Last step: evaluate a polynomial defined by the input at a random point)
Supporting Auxiliary Inputs from Server • Our solution: Extractable Verifiable Polynomial Delegation (VPD) digest δf client server commitment of the auxiliary inputs with extractability evaluation point a f(a) + proof f(x) Verification: or Result: extending IP (GKR, CMT etc.) to NP computations
Our Interactive Argument Protocol 2.0 fin(x) = f1(x) +f2(x) function (modeled as a circuit with auxiliary inputs) auxiliary inputs server client digestδf2 result IP digest δf1 of f1(x) for the data … Interactive proof (except last step) digest δf2 of f2(x) for auxiliary inputs data … fin(rin) VPD rin • f1(rin), f2(rin) + proofs f1(rin), f2(rin) or Verification of polynomial delegation
Our Interactive Argument Protocol • Setup only for the data, not for functions • Faster prover time (crypto operations is only linear to the input size, does not depend on the circuit size) • Supports auxiliary inputs • Dynamic data (details in paper)
Verifiable Databases SQL database queries client server result + proof digest δ Verification: or database
Example 1. SELECTSUM (l_extendedprice* (1 - l_discount)) AS revenueFROM lineitem, partWHERE 2. ( p_partkey = l_partkey 3. ANDp_brand = ‘Brand#41’ 4. ANDp_containerIN (‘SM CASE’, ‘SM BOX’, ‘SM PACK’, ‘SM PKG’) 5. ANDl_quantity >= 7 ANDl_quantity <= 7 + 10 6. ANDp_sizeBETWEEN 1 AND 5 7. ANDl_shipmodeIN (‘AIR’, ‘AIR REG’) 8. ANDl_shipinstruct = ‘DELIVER IN PERSON’ ) 9. OR 10. ( p_partkey = l_partkey 11. ANDp_brand = ‘Brand#14’ 12. ANDp_containerIN (‘MED BAG’, ‘MED BOX’,‘MED PKG’, ‘MED PACK’) 13. ANDl_quantity >= 14 ANDl_quantity <= 14 + 10 14. ANDp_sizeBETWEEN 1 AND 10 15. ANDl_shipmodeIN (‘AIR’, ‘AIR REG’) 16. ANDl_shipinstruct = ‘DELIVER IN PERSON’ ) 17. OR 18. ( p_partkey = l_partkey 19. ANDp_brand = ‘Brand#23’ 20. ANDp_containerIN (‘LG CASE’, ‘LG BOX’, ‘LG PACK’, ‘LG PKG’) 21. ANDl_quantity >= 25 ANDl_quantity <= 25 + 10 22. ANDp_sizeBETWEEN 1 AND 15 23. ANDl_shipmodeIN (‘AIR’, ‘AIR REG’) 24. ANDl_shipinstruct = ‘DELIVER IN PERSON’ ); Query #19 of the TPC-H benchmark http://www.tpc.org/tpch
Comparison with Prior Work Queries and database: TPC-H benchmark Database size: 6 million rows × 13 columns (2.8GB) in the largest table. MySQL 0.67s 100 hours* 7 hours 0.4 hour 54 hours* 1.8 hours 1.3 hours 6 ms 232 ms 148 ms 184 KB 0.3 KB 28 KB 325 hours* 0 hour 1.4 hours 171 hours* 4.16s 398ms 40 ms 0.3 KB 103 KB
Expressive SQL Update Query #15: create a new table on the fly by range and sum Old table: 2.8GB new table: 1.7MB
vSQL • Comparable efficiency, better expressiveness compared to customized VC • Up to 2 orders of magnitude faster compared to SNARKs • Setup only for database, no query dependent setup
RAM to Circuit Reduction [BCTV14] By time: state1 • CPU state • Time • Program counter • Instruction number • Flag • Registers • ….. state2 state3 …… stateT
RAM to Circuit Reduction [BCTV14] By time: By memory: state1 state'1 E.g., Add r1, r2, r3 Sorting Network CPU step Memory consistency state2 state'2 Memory consistency CPU step state3 state'3 …… …… CPU step Memory consistency stateT state'T
Inefficiency: Preprocessing By time: state1 CPU step • CPU step • All possible CPU instructions: • ADD, MUL, JMP, CMP, LOAD,… state2 CPU step state3 …… CPU step stateT
Our New RAM to Circuit Reduction By Instruction: By time: By Memory: state1 state''1 state'1 Add Sorting Network Sorting Network state2 state''2 state'2 # of Add Add state3 state'3 state''3 # of Load …… …… …… Load stateT state''T state'T
Our New RAM to Circuit Reduction By Instruction: By time: By Memory: state1 state''1 state'1 Add Permuta-tion protocol Permuta-tion protocol state2 state''2 state'2 # of Add Add state3 state'3 state''3 # of Load …… …… …… Load stateT state''T state'T
Our New Verifiable RAM • Prover time linear in #of CPU steps T (vs T log2 T in [BCTV14]) • 8× faster prover time • 120× smaller memory consumption. Up to 2 million CPU steps (vs 32K in [BCTV14])
Summary Verifiable Polynomial Delegation + Interactive Proof • vSQL, verifiable databases • Verifiable RAM Ongoing work: • Zero-knowledge with applications to crypto-currencies Thank you!!! Q&A
Inefficiency: Preprocessing By memory: state'1 Memory consistency state'2 Memory check for every CPU state Memory consistency state'3 …… Memory consistency state'T
Our New RAM to Circuit Reduction By Memory: Memory check only for states accessing memory state'1 state'2 state'3 …… state'T
Our New RAM to Circuit Reduction By Instruction: By time: By Memory: state1 state''1 state'1 Add Sorting Network Sorting Network state2 state''2 state'2 # of Add Add state3 state''3 # of Load …… …… Load stateT state''T