Internet Control Message Protocol (ICMP)
Internet Control Message Protocol (ICMP). Objective. Why need ICMP? ICMP in relation to IP ICMP Format and Message Types Utilities that use ICMP: Ping Traceroute. ICMP.

Internet Control Message Protocol (ICMP)
E N D
Presentation Transcript
Objective • Why need ICMP? • ICMP in relation to IP • ICMP Format and Message Types • Utilities that use ICMP: • Ping • Traceroute
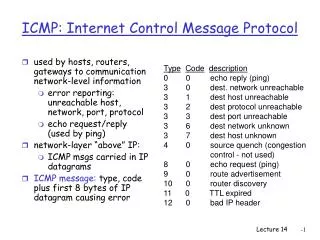
ICMP The IP protocol has no error-reporting or error-correcting mechanism. The IP protocol also lacks a mechanism for host and management queries. The Internet Control Message Protocol (ICMP) has been designed to compensate for the above two deficiencies. It is a companion to the IP protocol. Topics discussed in this section: Types of MessagesMessage FormatError Reporting and Query Debugging Tools
Why ICMP? • IP provides an unreliable, connectionless datagram delivery service. • Datagram travels from gateway to gateway until it reaches the destination host’s network, where it would be sent directly. • Question is: What happens if a gateway cannot route or deliver a datagram or if the gateway detects an unusual condition like network congestion?
Why ICMP? (cont.) • The designers separated such a mechanism from IP to simplify the main-stream IP. • The special-purpose mechanism --- Internet Control Message Protocol (ICMP) --- is considered a required part of IP and must be included in every IP implementation. • How do these ICMP messages travel? of course using IP services
Why ICMP? (cont.) • The destination of an ICMP message is not an application program or user, but the IP software on that machine. • The ICMP allows gateways to send error or control messages to other gateways or hosts; ICMP provides communication between the IP software on one machine and the IP software on another.
ICMP error messages • ICMP always reports error messages to the original source. • No ICMP error message will be generated inresponse to a datagram carrying an ICMP error message. • No ICMP error message will be generated for afragmented datagram that is not the first fragment. • No ICMP error message will be generated for adatagram having a multicast address. • No ICMP error message will be generated for adatagram having a special address such as 127.0.0.0 or 0.0.0.0.
ICMP Message Encapsulation ICMP Header ICMP Data IP Header IP Data Frame Header Frame Data Physical layer
ICMP Message Format • 8-bit integer message TYPE that identifies the message • 8-bit CODE field that provides further information about the message type • 16-bit CHECKSUM field (Internet-type checksum covering the whole of ICMP)
ICMP Echo Request/Echo Reply • Testing Destination Reachability and Status • A debugging aid for network managers: echo request and echo reply (ping command) • Echo Request and Reply Message Format • TYPE 8 for request • TYPE 0 for reply
ICMP Dest. Unreachable (Type=3) Reports of Unreachable Destinations- Unreachability of what? Code Meaning 0 network unreachable 1 host unreachable 2 protocol unreachable 3 port unreachable 4 fragmentation needed and DF set 5 source route failed 6 destination network unknown 7 destination host unknown 8 source host isolated 9 communication with destination network administratively prohibited 10 communication with destination host administratively prohibited
Congestion and Datagram Flow Control • Usually, congested gateways send one source quench message for every datagram that they discard. • A source quench message is a request for the source to reduce its current rate of datagram transmission. • No reversal of ICMP source quench request. A host lowers the rate at which it sends on the receipt of a source quench messages; it then gradually increases the rate as long as no further source quench are received.
ICMP Source Quench Format Code (0) Type (4) Checksum Unused, must be zero Internet Header + First 8 bytes of datagram ... • Sent each time a datagram is discarded
ICMP Redirect Message Type (5) Code (0-3) Checksum Gateway Internet Address Internet Header + First 8 bytes of datagram ...
net3 net1 net2 Host A R2 R1 ICMP Redirect Message • If Host A sends a packet destined to net3 to R2 Then • R2 relays the packet to R1 • R2 sends ICMP redirect message to Host A • A should update its Routing Table with the entry • (Network ID:net3; Next Hop: R1)
ICMP Time Exceeded message • sent whenever a datagram is discarded because TTL reached zero, using Type 11- Code 0 • sent when time set to collect fragments belonging to a particular packet expires, using Type 11 - Code 1
Clock Synchronization and Transit Time Estimation • A machine can obtain time from another machine, using timestamp request message. • Time stamp is a 32-bit quantity representing m-seconds elapsed since midnight. The receiving machine responds with timestamp reply message, which contains originate, receive, and transmit timestamps, with proper request-reply message association.
Obtaining a Subnet Mask A host can send an address mask request message to a gateway and receive address mask reply message. Such a message can be sent directly or broadcast, using type 17 for request 18 for reply, and code 0
Utilities that Use ICMP • PING: sends ICMP Echo Requests and monitors ICMP Echo Replies • TraceRoute: Sends a sequence of ICMP Echo Requests with increasing TTL values starting from 1 and monitors the ICMP Time Exceeded Messages (reported by routers along the path to destination) or ICMP Echo Reply from destination
Ping Example We use the ping program to test the server fhda.edu. The result is shown on the next slide. The ping program sends messages with sequence numbers starting from 0. For each probe it gives us the RTT time. The TTL (time to live) field in the IP datagram that encapsulates an ICMP message has been set to 62. At the beginning, ping defines the number of data bytes as 56 and the total number of bytes as 84. It is obvious that if we add 8 bytes of ICMP header and 20 bytes of IP header to 56, the result is 84. However, note that in each probe ping defines the number of bytes as 64. This is the total number of bytes in the ICMP packet (56 + 8).
TraceRoute Example We use the traceroute program to find the route from the computer where utility is running to the server fhda.edu. The following shows the result: The unnumbered line after the command shows that the destination is 153.18.8.1. The packet contains 38 bytes: 20 bytes of IP header, 8 bytes of UDP header, and 10 bytes of application data. The application data are used by traceroute to keep track of the packets.
TraceRoute Example (continued) The first line shows the first router visited. The router is named Dcore.fhda.edu with IP address 153.18.31.254. The first round-trip time was 0.995 ms, the second was 0.899 ms, and the third was 0.878 ms. The second line shows the second router visited. The router is named Dbackup.fhda.edu with IP address 153.18.251.4. The three round-trip times are also shown. The third line shows the destination host. We know that this is the destination host because there are no more lines. The destination host is the server fhda.edu, but it is named tiptoe.fhda.edu with the IP address 153.18.8.1. The three round-trip times are also shown.