Internet Protocol Security (IP Sec)
Internet Protocol Security (IP Sec). Securing Intranets and Extranets at all levels. Major Cryptographic Systems. Layer. Cryptographic System. Application. Kerberos. Transport. SSL/TLS. WAN e.g. Internet. IPsec. Data Link. PPTP, L2TP (really only a tunneling system). Physical.

Internet Protocol Security (IP Sec)
E N D
Presentation Transcript
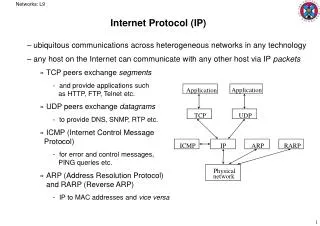
Major Cryptographic Systems Layer Cryptographic System Application Kerberos Transport SSL/TLS WAN e.g. Internet IPsec Data Link PPTP, L2TP (really only a tunneling system) Physical Not applicable. No messages are sent at this layer—only individual bits
Securing Network Communication: What Are the Challenges? Challenges to securing network communication include: • Preventing data modification while in transit • Preventing data from being read and interpreted while in transit • Keeping data secure from unauthorized users • Keeping data from being captured and replayed
What Is Internet Protocol Security? IPSec: A framework of open standards to ensure private, secure communications over IP networks through the use of cryptographic security services IPSec provides the following benefits: • Transparent to users and applications • Provides restricted access to servers • Customizable security configuration • Centralized IPSec policy administration through Active Directory • Supports authentication and encryption of traffic. • Certifies the originator of the packet. • Protects the data from interception and tampering while in transit.
IPsec • IPSec consists of two Internet protocol extensions: the Authentication Header (AH) and the Encapsulating Security Payload (ESP) that support creation of secure networks. • Access is controlled by a companion key management protocol called the Internet Key Exchange (IKE).
IPsec • Together, IPSec and IKE ensure that authorized parties may exchange private IP packets securely over a public network. • Packet content is kept confidential by applying encryption and protected against modification through digital signing. IPSec can be used to securely “tunnel” packets to routers or firewalls over a WAN, or to securely “transport” packets end to- end between desktops and servers.
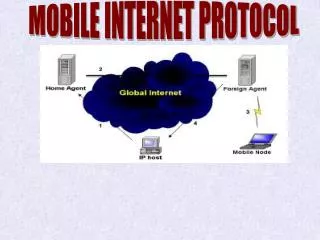
IPsec Operation: Transport Modes Site Network Site Network Secure Connection Security in Site Network Security in Site Network Extra Software Required Extra Software Required Secure on the WAN e.g. Internet
IPsec Operation: Tunnel Modes IPsec Server IPsec Server Site Network Site Network Tunneled Connection No Security in Site Network No Security in Site Network No Extra Software No Extra Software Secure on the WAN e.g. Internet
Security Association (SA) • One of the most important concepts in IPSec is called a Security Association (SA). Defined in RFC 1825. • SAs are the combination of a given Security Parameter Index (SPI) and Destination Address. • SAs are one way. A minimum of two SAs are required for a single IPSec connection.
Security Association (SA) • SAs contain parameters including: • Authentication algorithm and algorithm mode • Encryption algorithm and algorithm mode • Key(s) used with the authentication/encryption algorithm(s) • Lifetime of the key • Lifetime of the SA • Source Address(es) of the SA • Sensitivity level (ie Secret or Unclassified)
How IPSec works: Phase 1 • Internet Key Exchange (IKE) is used to setup IPSec. • IKE Phase 1: • Establishes a secure, authenticated channel between the two computers • Authenticates and protects the identities of the peers • Negotiates what SA policy to use • Performs an authenticated shared secret keys exchange • Sets up a secure tunnel for phase 2 • Main Mode or Aggressive mode
How IPSec works: Phase 1 • Main Mode IKE • Negotiate algorithms & hashes. • Generate shared secret keys using a Diffie-Hillman exchange. • Verification of Identities. • Aggressive Mode IKE • Squeezes all negotiation, key exchange, etc. into less packets. • Advantage: Less network traffic & faster than main mode. • Disadvantage: Information exchanged before a secure channel is created. Vulnerable to sniffing.
Establishing IPsec Security Associations Using IKE Internet Key Exchange Security Association UDP Port 500 Party A Party B First establish IKE association andprotected session Then create IPsec SAs within the Protection of the IKE session. IPsec SAs
How IPSec works: Phase 2 • An AH or ESP packet is then sent using the agreed upon “main” SA during the IKE phase 1. • IKE Phase 2 • Negotiates IPSec SA parameters • Establishes IPSec security associations for specific connections (like FTP, telnet, etc) • Renegotiates IPSec SAs periodically • Optionally performs an additional Diffie-Hellman exchange
How IPSec works: Communication • Once Phase 2 has established an SA for a particular connection, all traffic on that connection is communicated using the SA. • IKE Phase 1 exchange uses UDP Port 500. • AH uses IP protocol 51. • ESP uses IP protocol 50.
3-phase strategy in general terms that can be applied to many different enterprises Phase One: A Simple, Generic Policy
3-phase strategy in general terms that can be applied to many different enterprises Phase Two: Custom Workgroups
Phase Three: Adding Trust Infrastructure • Replacing pre-shared keys with credentials enabling strong authentication. • In homogenous Windows environments, Kerberos tickets might be used. • In all other environments, including mixed Windows networks; a Public Key Infrastructure should be used. • IPSec partners can be authenticated with “raw” public keys, but most enterprises will prefer X.509 digital certificates verified by a trusted CA. • PKI combines strong access control with scalable administration through the use of CA hierarchies, cross-certification, and delegation.