Internet Worm propagation
50 likes | 78 Vues
Explore the methods and incidents of internet worm propagation like Code Red, Slammer, and Blaster, along with the risks posed by email viruses. Learn about attacking vulnerabilities, honeypots, HoneyNets, and the emerging trend of botnets.

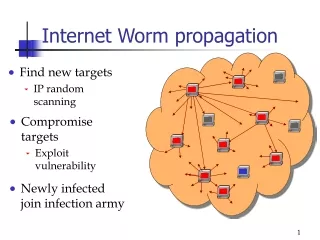
Internet Worm propagation
E N D
Presentation Transcript
Internet Worm propagation • Find new targets • IP random scanning • Compromise targets • Exploit vulnerability Newly infected join infection army
Worm Infection Incidents • Code Red (Jul. 2001) : 360,000 infected in 14 hours • Slammer (Jan. 2003) : 75,000 infected in 10minutesCongested parts of Internet (ATMs down…) • Blaster (Aug. 2003): 150,000 ~ 8 million infected DDOS attack (shut down domain windowsupdate.com) • Witty (Mar. 2004) : 12,000 infected in half an hourAttackvulnerabilityin ISS security products • Sasser (May 2004): 500,000 infected within two days Infection faster than human response !
Email Virus and Attacks • Email Viruses: • Executable code in email attachment • Social engineering trick to fool users to click attachment • Sender is your friend (faked email header information) • Email appears to come from security, failed report, etc • Infection procedure: • Set up SMTP engine • Find all email addresses to send email to • Avoid some email domains
Honeypot and HoneyNet • Honeypot: A honeypot is a fictitious vulnerable IT system used for the purpose of being attacked, probed, exploited and compromised • Attract attack • Analyze attacking code, attacking behavior • Find out how to defend • HoneyNet: a network (physical/virtual) of honeypots • Covering a large number of IP addresses • Monitor more attacking incidents
New Attack Trend --- Botnet • Botnet: a network of infected hosts controlled by an attacker • Each host is installed with “bot” • Hosts can be compromised by any mechansims • Email, worm scan, network share, malicious web… • Attacks: DDoS (extortion), spam, phishing, ads abuse, new attack attacker controller controller bot bot bot