Understanding Routing Algorithms and Congestion Control Mechanisms in Networking
E N D
Presentation Transcript
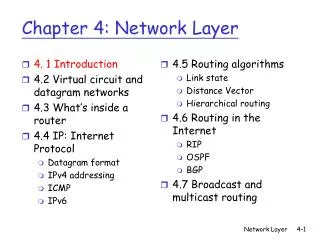
Review: Routing algorithms • Distance Vector algorithm. • What information is maintained in each router? • How to distribute the global network information? • How to compute the new routing table? • Distance Vector algorithm • what is the major problem of this algorithm? • The count to infinity problem. • Link State algorithm • What information is gathered by each router? • How to distribute the global network information? • How to compute the new routing table?
Next issue: Congestion control • What is congestion control? Mechanisms to prevent hosts from flooding the network. • Congestion control .vs. flow control? • Both typically require the sender to slow down. • Causes are different • flow control -- link, local • congestion control -- network, global • Example: • 50 stations are connected by a 10Mbps Ethernet, all stations want to send data at 500Kbps. • 50 stations are connected by a 10Mbps Ethernet, one station wants to send data to another station at 500Kbps. The receiving station can only process data at 100Kbps.
Congestion control mechanisms: • Open loop (proactive): prevent the congestion from happening. • Closed loop (reactive): detect the congestion and do something to fix the problem. • Traffic shaping: • congestion is typically caused by bursty traffic • traffic shaping forces the traffic to be not so bursty • Leaky Bucket algorithm. • each host connected to the network has an interface containing a "leaky bucket” (a queue) • Packets can arrive at any rate • Packets are discarded when the bucket overflows. • Packets depart at a constant rate. • Example: a burst data of 200Mbps for 40 ms, using leaky bucket algorithm with a data rate of 16Mbps?
Congestion control mechanisms: • Traffic shaping: • The leaky bucket algorithm has a constant data rate, we want the communication to be a little bursty when the computer needs it. • Token bucket algorithm. • A packet can go if there is a token. The token is destroyed after the packet is gone. • A token is generated very T second • Tokens can be accumulated to an upper bound. • Many variations. A token bucket algorithm is typically described using three parameters: (burst size, average rate, max rate) • Admission control • like the telephone system, when there is congestion, reject service to avoid making the situation worse
Choke packet: (used in both VC and datagram) • Each router monitors the utilization of its output lines • When the utilization is above a threshold, send chock packet to the source host • The source will then slow down sending the packets to the same destination. • The source will avoid listening to the choking packet for a while • Hop by Hop chock packet • LA to NY at 155Mbps, 30 msec, 4.6Mb in the place that causes congestion, choke packets sending to the source may take too long to take effect • Instead, ask every intermediate router to slow down. • quick relief at the point of congestion • more buffer at upstream routers
load shedding • I am congested now, let me drop some packets to make the network easilier. • Which packet to drop? • based on service: ftp -- wine policy (older is better), real time -- milk policy (newer is better) • indicated by the source which packets that are more important. (prioritize packets)
Next issue: Internetworking. • many networks exist: ATM, Ethernet, DECNET ... • These networks have lot of differences: • services: connection-oriented and connectionless • Protocols: IP, SNA, IPX • Addressing: Flat and hierachical • Packet size: • Quality of Service: support or not • Error Handling: • How to send packets from one network to another network?
Two types of internetworking. • Concatenated Virtual Circuits: • A connection to a remote host is set up by concatenating virtual circuits in all networks it passes by. • Gateways response for converting packet format and maintaining VC. • Work best when all network have the same properties. • all reliable, all unreliable. • Can also be done on transport layer for datagram subnets. • Connectionless internetworking: • inject datagrams into subnets and hope for the best • packets may not follow the same route • also works on VC subnet.
Some problems with internetworking • format conversion can be hard: • Example: IP address is different of OSI address (phone number) IP address <--> OSI address IP address <--> IPX address • fragmentation: • Maximum packet size is different in different networks • Fragmentation deals with the cases when large packet sends to the network whose maximum packet size is small. • How to do this? • solution 1: make it not happening, network unreachable.
Solution 2: chop the large packet into small fragments and send fragments as individual internet packets. • Problem: when to put the packet back together? • at gateways: • transparent to other networks • high overhead -- all packet must pass through the same exit gateway • at the destination: • every fragment is treated as an internet packet • smart end hosts (may not always be true) • fragments must be numbered • retransmission overhead (can be complicated).
Tunneling. • Internetworking for the general case is extremely difficult. • Common case: source and destination are on the same type of network. Different networks in between. • How it works? • Source sends packets to an intermediate gateway • Intermediate gateways put the whole packet into the payload field (don't interpret). • The destination will understand the packet. • Firewalls: • routers with packet filtering capability • forward a packet only when the packet passes its testing.