ATM Technology in Telephone Networks: Benefits and Challenges
670 likes | 788 Vues
Explore the significance of ATM technology in telephone networks, its internal benefits, implications for network design, and the evolving landscape toward gigabit speeds. Understand the key assumptions behind the ATM conceptual model and the architectural principles shaping its deployment.

ATM Technology in Telephone Networks: Benefits and Challenges
E N D
Presentation Transcript
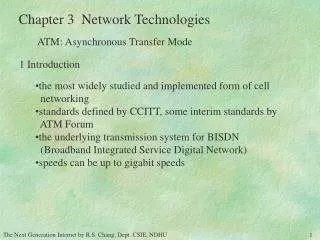
Chapter 3 Network Technologies ATM: Asynchronous Transfer Mode 1 Introduction • the most widely studied and implemented form of cell • networking • standards defined by CCITT, some interim standards by • ATM Forum • the underlying transmission system for BISDN • (Broadband Integrated Service Digital Network) • speeds can be up to gigabit speeds
Chapter 3 Network Technologies 2. ATM Inside the Telephone Networks ATM is tremendously useful inside a telephone network. It is important to understand these internal benefits of ATM because the ATM standards occasionally reflect internal telephony requirements Two important telephone networks changes: • becoming increasingly computerized • consolidation of transmission lines because of fiber
Chapter 3 Network Technologies 2. ATM Inside the Telephone Networks increased computerization • routing of calls, traffic management, and control • services (話中插接,多線獨用電話自動尋線, • 指定轉接,勿干擾,按時叫醒 ,簡速撥號,三方通話,080,081…) • require keeping much more information on-line • voice channel and common signaling channel(data channel) It would be nice if both the data network and telephone network could be built from the same technology.
Chapter 3 Network Technologies 2. ATM Inside the Telephone Networks increasing use of optical fiber consolidation of transmission lines multiplexing far more circuits onto the same link multiplexing is difficult and expensive easier to multiplex separately addressed packets than to multiplex mixes of individual bits
Chapter 3 Network Technologies 2. ATM Inside the Telephone Networks The telephone community is designing ATM to meet two sets of goals: (1) to meet its own internal needs for a more flexible transmission technology (2) to allow it to offer new services to users
Chapter 3 Network Technologies 2. ATM Inside the Telephone Networks ATM a data communication technology developed by the telephone community for the telephone community The ATM standards have occasionally clashed with the needs of the data communications community Because ATM meets an internal telephony need, ATM will be implemented. Data communications must learn it and adapt to it. But, It may not be so after the advances in gigabit packet networks.
Chapter 3 Network Technologies 3. ATM Conceptual Model At least four major assumptions lie behind the design of ATM: (1) ATM networks will be organized in a hierarchy (2) ATM will be a connection-oriented service (3) Most networks for ATM to run will be fiber optic networks (4) It is desirable to support very low cost attachments (equipment) closely mirror the state of many of the telephone networks over which ATM is deployed
Chapter 3 Network Technologies 3. ATM Conceptual Model From these assumptions come a number of architectural principles critical to ATM. point 1: hierarchical networks Method of interconnecting varies depending on where the connection point is in the hierarchy. • users' equipment to networks: UNI(user-network interface), • to provide an interface to the user equipment that supports • multiplexing and to protect an ATM provider's network from • misbehaved user equipment • network to network: NNI(network-network interface), to • provide smooth interconnection between independently • operated ATM networks -node
Chapter 3 Network Technologies 3. ATM Conceptual Model From these assumptions come a number of architectural principles critical to ATM. point 2: connection-oriented • Because connection setup is required, ATM channel • identifiers can be kept short (28 bits). (compared to end-to-end) • Because ATM is hierarchical, the channel identifiers • also have a hierarchical structure(channel id+path id). • Backbone switches are allowed to route just on the path • identifier.
Chapter 3 Network Technologies 3. ATM Conceptual Model From these assumptions come a number of architectural principles critical to ATM. point 3: run on fiber optic networks • minimize errors and loss (to that of fiber:1 in 1012) • overloaded switches drop a burst of cells • To minimize the effects of such overloads, ATM • rank cells, and the expectation is that high-priority • cells will have loss rates comparable to that of optical • fiber.
Chapter 3 Network Technologies 3. ATM Conceptual Model From these assumptions come a number of architectural principles critical to ATM. point 4: low cost attachment equipment • ATM standards bodies chose to prohibit cell reordering • Prohibiting cell reordering allows attachments to use • simpler form of buffering. (use FIFO memory instead of • RAM or no buffering at all) • Switch has to maintain the ordering (complex switch)
Chapter 3 Network Technologies 3. ATM Conceptual Model Speed Hierarchy SONET CCITT Data rate Payload rate Designation designation (Mbps) (Mbps) STS-1/OC-1 51.84 50.112 STS-3/OC-3 STM-1 155.52 150.336 STS-9/OC-9 STM-3 466.56 451.008 STS-12/OC-12 STM-4 622.08 601.344 STS-18/OC-18 STM-6 933.12 902.016 STS-24/OC-24 STM-8 1244.16 1202.688 STS-36/OC-36 STM-12 1866.24 1804.032 STS-48/OC-48 STM-16 2488.32 2405.376 SONET: Synchronous Optical Network STS: Synchronous Transport Signal, OC: Optical Carrier STM: Synchronous Transport Module
Chapter 3 Network Technologies 4. ATM Cell Format ATM Protocol Structure ATM End System ATM End System ATM Adaptation Layer (AAL) ATM Layer Physical Layer ATM Adaptation Layer (AAL) ATM Layer Physical Layer ATM Switch ATM Layer Physical Layer physical medium
Chapter 3 Network Technologies 4. ATM Cell Format AAL: Convergence(CS), Segmentation and Reassembly(SAR) ATM: Generic flow control, Cell header generation/extraction Cell VPI/VCI translation, Cell multiplex and demultiplex Physical Transmission Convergence: Cell rate decoupling, HEC sequence generation/verification, Cell delineation, Transmission frame adaptation, Transmission frame generation/recovery Physical Medium: Bit timing
Chapter 3 Network Technologies 4. ATM Cell Format header 5 bytes data, 48 bytes used by UNI, NNI, and switches to route the cell contain one of the ATM adaptation layer data
Chapter 3 Network Technologies 4. ATM Cell Format data camp voice camp Why 48 data bytes? 128 16 The result of the compromise is that the ATM cell size is considered a poor size for use with both voice and data. 64 32 48 Study from Internet traffic profile indicates 20% overhead. In ATM, to send a 50 bytes mail overhead=
Chapter 3 Network Technologies 5. ATM Cell Header at the NNI The ATM cell header has two formats: one is for cells being given to a UNI by an ATM user, the other is for cell crossing an NNI. The format for the NNI is slightly simpler and is discussed first.
Chapter 3 Network Technologies 5. ATM Cell Header at the NNI bits 8 7 6 5 4 3 2 1 Virtual Path Identifier (VPI) Virtual Channel Identifier(VCI) payload type CLP cell loss priority (1 for low priority) Header CRC
Chapter 3 Network Technologies 5. ATM Cell Header at the NNI The Virtual Channel and Virtual Path Identifiers 16 bits 12 bits The combination of the VPI and VCI is a unique address for a connection. And depending on the location in the network topology, ATM switches route based on both VPI and VCI, or just on the VPI.
Chapter 3 Network Technologies 5. ATM Cell Header at the NNI The Virtual Channel and Virtual Path Identifiers VC VC VP VP Transmission Path VP VP VC VC
Chapter 3 Network Technologies 5. ATM Cell Header at the NNI The Virtual Channel and Virtual Path Identifiers easier hop-by-hop routing small hop identifiers cannot be used as global identifiers solution: make VPI and VCI unique on a hop-by-hop basis
Chapter 3 Network Technologies 5. ATM Cell Header at the NNI
Chapter 3 Network Technologies 5. ATM Cell Header at the NNI Payload-Type Field: indicate user trafficor OAM (Opeartion, Administration, and Management) traffic User traffic 0 0/1 0/1 user signalling bit (used by one of the adaptation layers to mark the end of each datagram) congestion bit 1 if congested
Chapter 3 Network Technologies 5. ATM Cell Header at the NNI Cell Loss Priority: Discard cells with CLP=1 first serve two roles: (1) provide modest flexibility with two levels of traffic priority Encourage ATM users to periodically send some extra data into the network, but to allow the network to drop this extra traffic if the network is overloaded (2) some protection against abusive users ATM standards permits the network to set the CLP bit in as many cells as necessary to reduce the number of priority cells to the agreed upon rate
Chapter 3 Network Technologies 6 ATM at the User-Network Interface bits 8 7 6 5 4 3 2 1 virtual path generic flow control identifier Virtual Channel Identifier(VCI) payload type CLP Header CRC support control of the ATM traffic flow in a customer network, it can be used to alleviate short-term overload conditions (user-to-network direction) at the UNI. If not used, zero is assumed.
Chapter 3 Network Technologies 6 ATM at the User-Network Interface bus Problems with the ATM UNI (1) GFC field is almost useless (2) reduced VPI number means reduced connection at where it will be needed badly (3) having two different ATM cell formats is generally a bad idea (not a concatenative protocol) UNI ATM network UNI ring
Chapter 3 Network Technologies 5. ATM Cell Header at the NNI Payload-Type Field: indicate user trafficor OAM (Operation, Administration, and Management) traffic OAM traffic bit pattern definition 100 OAM link associated cell 101 OAM end-to-end associated cell 110 Resource management cell 111 Reserved for future use
Chapter 3 Network Technologies 6 ATM at the User-Network Interface The advantage of concatenative protocols is that communication devices can be plugged into the network wherever needed. For example, IP, CLNP (ConnectionLess Network Protocol), Ethernet, etc. With nonconcatenative protocols, like ATM, one has worry whether the device matches the available interface. Furthermore, the UNI distinction is rather arbitrary.
Chapter 3 Network Technologies 7 Adaptation Layers The protocols for packaging data into cells are collectively referred to as the ATM adaptation layer; the individual protocols are referred to as AALs. datagrams, voice samples, video frames AAL AAL ATM network cells
Chapter 3 Network Technologies 7 Adaptation Layers Given all the various forms that digital data can appear in, how many different adaptation protocols are required to support all the diverse types of data that one might send over an ATM network? solution 1: no adaptation at all, applications take charge compromise interoperability solution 2: only one adaptation layer simple and ideal for interoperability
Chapter 3 Network Technologies 7 Adaptation Layers ITU's approach: It chose to develop a small suite of adaptation layer protocols, with different adaptation protocols optimized for different types of applications four class of applications: (1) constant bit-rate application: require bounded delay, telephones, data video systems (class A) (2) variable bit-rate applications: still require delay bounds (class B) (3) connection-oriented data applications: support X.25 data (class C) (4) connectionless data applications: support TCP/IP, TP4/CLNP (class D) A new class: available bit-rate
Chapter 3 Network Technologies 7 Adaptation Layers Class A Class B Class C Class D Timing relation between source and destination Required Not required constant variable Bit Rate connection- less connection oriented Connection mode
Chapter 3 Network Technologies 7 Adaptation Layers AAL 1: constant bit-rate service AAL 2: variable bit-rate service AAL 3, AAL 4: merged into AAL 3/4 (but not suitable for most data communications applications) AAL 5: Simple and Efficient Adaptation Layer protocol (SEAL)
Chapter 3 Network Technologies 7 Adaptation Layers ATM Convergence and SAR Protocols adaptation layer convergence sublayer segmentation and reassembly sublayer In retrospect, the two sublayers are so closely related that it is not clear that it is useful to consider them separately.
Chapter 3 Network Technologies 7 Adaptation Layers ATM Convergence and SAR Protocols AAL-SDU 1-to-many or many-to-1 CS-PDU padding H T unused SAR-PDUs (48 bytes) H: header PDU: protocol data unit T: trailer SDU: service data unit
Chapter 3 Network Technologies 8 Signaling an ATM Connection Before any ATM cells can be sent, an ATM connection must be established between the sender and receiver and a VCI/ VPI must be assigned to the connection at each hop. a signaling or setup protocol is needed, which concerns QoS negotiation
Chapter 3 Network Technologies 9 Putting the ATM Bits on the Wire ATM in SONET (OC-3 and Faster) 90 columns SONET Frames Cells 9 rows cells may cross row boundaries. transport overhead information payload overhead
Chapter 3 Network Technologies 10 Issues in ATM How will ATM Be Deployed and by Whom? by telephone community and computer communication community: difference in terminology, perspective, and their attitudes toward time (of implementation) Changing a telephone system to support new services requires a lot of time. The computer communication community is much more dynamic. (make major changes in technology every ten years or so.) consequences: stresses on the standards process missed opportunities for integration
Chapter 3 Network Technologies 10 Issues in ATM What Exactly Is ATM? ATM is a very general protocol, capable of providing a wide range of data services. But, for which services will ATM actually be used? ATM looks very different depending on one's perspective.
Chapter 3 Network Technologies 10 Issues in ATM What Exactly Is ATM? (1) Treat ATM as just one type of networking service among many Implications: One should try to make ATM as compatible with other types of networks as possible approach taken by the computing community (for example, AAL 5)
Chapter 3 Network Technologies 10 Issues in ATM What Exactly Is ATM? (2) Think of ATM is as a service that replaces bits on a wire with cells on a wire. One does not use an ATM service, one used a service over ATM. A system using video over ATM generally cannot communicate with a system using data over ATM. ITU's perspective
Chapter 3 Network Technologies 10 Issues in ATM What Exactly Is ATM? (3) Treating ATM as an internetworking protocol in its own right Become less and less feasible. ATM's nonconcatenative interface and the decision to use multiple AALs, both suggest that ATM will not be the same protocol for all the devices attached to an ATM network,
Chapter 3 Network Technologies 11 ATM LAN Emulation
Chapter 3 Network Technologies 11 ATM LAN Emulation Emulate LAN’s Broadcast
Chapter 3 Network Technologies 11 ATM LAN Emulation
Chapter 3 Network Technologies 11 ATM LAN Emulation
Chapter 3 Network Technologies 12 Other Issues in ATM Networks Traffic Shaping A source promises the network that the traffic a flow sends into the network will conform to a particular shape. • The network uses this information to: • decide whether to accept the flow (CAC: Connection Admission Control) • if accepted, how to manage the flow's traffic (UPC: Usage Parameter Control) Three major purposes: (1) The network knows what kind of traffic to expect. (2) The network can determine if the flow should be allowed to send. (3) The network can periodically monitor the flow's traffic and confirm that the flow is behaving as it promised.
Chapter 3 Network Technologies 12 Other Issues in ATM Networks Traffic Shaping Regulating traffic For a data rate of 100Mbps, consider the following two flows: (1) a single 100M bits packet every second (2) 1 K bits packet every 10 ms Their effects on the network may be very different. (For 1, long serialization time, large buffer space, ...) How a flow injects its data into the network can be as important as the amount of data it sends.
Chapter 3 Network Technologies 12 Other Issues in ATM Networks Traffic Shaping Isochronous shaping: Simple Leaky Bucket :bucket size, limit how much data may build up waiting for the network b b r :cell drain-out rate The primary effect of simple leaky bucket shaping is to coerce a bursty source of data into a flow of equally spaced cells, each cell being emitted 1/r units of time after the last one. r
Chapter 3 Network Technologies 12 Other Issues in ATM Networks Traffic Shaping Isochronous shaping: Simple Leaky Bucket The major appeal: easy to implement Each flow's traffic can be managed by a simple FIFO buffer with a timer set to go off every 1/r units of time It is also easy to describe and police. described simply by r and if a flow ever sends two cells together in less time than 1/r, the the flow is violating its promised traffic pattern